SPF Record Checker for Your Domain
Check Your SPF Record Now
Enter any domain below to instantly analyze its SPF record - free, no signup required.
We'll retrieve and analyze the live SPF record from DNS for your domain.
 ## **SPF Record Example**
Let’s consider this SPF record example-
```
v=spf1 a include: example.com ~all
```
Where,
- _v=spf1_ indicates the **version of SPF** used. Currently, there’s only one SPF version; so, all SPF TXT records begin with v=spf1 and include [ipv4 or ipv6](https://www.thousandeyes.com/learning/techtorials/ipv4-vs-ipv6) mail servers that domain owners trust.
- ‘a’ represents authorization of the system in the ‘domain a’ record to send email messages on behalf of the company and its mail server.
- The _include_ tag allows adding the **IP address of a third-party sender** having the rights to send emails from your site.
- The _~all_ mechanism specifies a **softfail**, which means emails failing SPF authentication checks will land in the spam folder of a recipient.
## **SPF Record Example**
Let’s consider this SPF record example-
```
v=spf1 a include: example.com ~all
```
Where,
- _v=spf1_ indicates the **version of SPF** used. Currently, there’s only one SPF version; so, all SPF TXT records begin with v=spf1 and include [ipv4 or ipv6](https://www.thousandeyes.com/learning/techtorials/ipv4-vs-ipv6) mail servers that domain owners trust.
- ‘a’ represents authorization of the system in the ‘domain a’ record to send email messages on behalf of the company and its mail server.
- The _include_ tag allows adding the **IP address of a third-party sender** having the rights to send emails from your site.
- The _~all_ mechanism specifies a **softfail**, which means emails failing SPF authentication checks will land in the spam folder of a recipient.
 ## **Elements Analyzed by an SPF Record Checker**
If you need an answer to ‘**is my SPF record correct**’ then you have to pass your record through an **SPF checker** that validates it against the following elements-
### **Presence of an SPF Record**
The foremost thing an **SPF record lookup** tool would do is check whether an SPF TXT record is published in your domain. If not, it will result in an error related to validity. In this case, you need to create an SPF record by following these steps-
#### **How to Create an SPF Record?**
- Create an extensive list of senders allowed to send emails from your domain. This includes web servers, [ISP and ESP mail servers](https://glockapps.com/blog/isps-and-esps-how-to-choose/), in-office mail servers, and third-party vendors.
- _If you have more than one domain, you must create SPF DNS records for **all of them**, including non-email-sending domains._
- Use an online SPF generator to create your record. Make sure you have knowledge of SPF syntax in advance.
- Publish the [SPF record](/spf-record-checker/spf-record-syntax/) to DNS.
- Test your record to see if there are any issues. You can get help from an **SPF lookup tool**.
### **Existence of Multiple SPF Records**
You can’t have more than one SPF record per domain. So, if you have found multiple records while performing an **SPF record check for a domain** of yours, then you have to merge them into one.
Generally, big email providers like Gmail and Microsoft Exchange [merge SPF records](https://www.mailerlite.com/help/how-to-merge-spf-records) **automatically**, and you don’t have to take care of it at all. But, small email providers lack this intelligence feature, and you have to do it manually by consolidating your DNS TXT entries.
_Please note that you can’t simply copy one TXT record and paste it into another to merge them. This will invalidate your record._
## **Elements Analyzed by an SPF Record Checker**
If you need an answer to ‘**is my SPF record correct**’ then you have to pass your record through an **SPF checker** that validates it against the following elements-
### **Presence of an SPF Record**
The foremost thing an **SPF record lookup** tool would do is check whether an SPF TXT record is published in your domain. If not, it will result in an error related to validity. In this case, you need to create an SPF record by following these steps-
#### **How to Create an SPF Record?**
- Create an extensive list of senders allowed to send emails from your domain. This includes web servers, [ISP and ESP mail servers](https://glockapps.com/blog/isps-and-esps-how-to-choose/), in-office mail servers, and third-party vendors.
- _If you have more than one domain, you must create SPF DNS records for **all of them**, including non-email-sending domains._
- Use an online SPF generator to create your record. Make sure you have knowledge of SPF syntax in advance.
- Publish the [SPF record](/spf-record-checker/spf-record-syntax/) to DNS.
- Test your record to see if there are any issues. You can get help from an **SPF lookup tool**.
### **Existence of Multiple SPF Records**
You can’t have more than one SPF record per domain. So, if you have found multiple records while performing an **SPF record check for a domain** of yours, then you have to merge them into one.
Generally, big email providers like Gmail and Microsoft Exchange [merge SPF records](https://www.mailerlite.com/help/how-to-merge-spf-records) **automatically**, and you don’t have to take care of it at all. But, small email providers lack this intelligence feature, and you have to do it manually by consolidating your DNS TXT entries.
_Please note that you can’t simply copy one TXT record and paste it into another to merge them. This will invalidate your record._
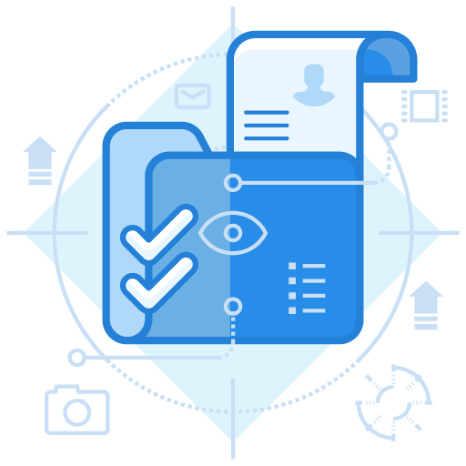
 [Image sourced](https://support.mailessentials.gfi.com/hc/en-us/articles/360015116740-How-MailEssentials-Sender-Policy-Framework-SPF-filter-works) from mailessentials.gfi.com
### **SPF Syntax Errors**
A [poorly constructed SPF record](https://support.securityscorecard.com/hc/en-us/articles/115003337866-Malformed-SPF-Record) has **syntax errors and typos** that invalidate it. Here’s what it should have-
- Beginning with _**v=spf1**_.
- Ending with the _all_ tag- _~all, -all,_ or _+all_
- No typographic errors.
### **Maximum Lookup Limit**
An email server’s resources are consumed upon each lookup, and that’s why there’s a limit of a maximum of **10 DNS SPF lookups**. The limit was imposed to avoid overloading the mail server.
Once the limit is reached, then either emails are returned or the list of authorized IP addresses is not retrieved. This gives malicious actors the opportunity to attempt [phishing attacks in your company’s name](https://www.digitalinformationworld.com/2023/04/75-e-commerce-phishing-attacks-exploit.html).
So, if you fail to be back within the limit despite making all the efforts, [AutoSPF](/)’s automatic **SPF flattening** service will resolve the issue.
### **Use of a PTR Mechanism**
The [PTR mechanism](http://www.open-spf.org/Mechanism/ptr/) is used for resolving a domain name to its corresponding IP address. Its conjunction with SPF records is deprecated due to its slow and unreliable nature. That’s why it can’t be resolved using diagnostic tools.
### **Use of the +all Tag**
An **SPF record checker** will return with a warning if your record includes a _+all_ tag. The inclusion of this tag allows anyone on the internet to send emails using your domain, and that’s not recommended. This will enable [hackers to exploit your domain](https://thehackernews.com/2023/08/phishers-exploit-salesforces-email.html) for sending fraudulent emails in your name.
### **Characters After the** **_‘all’_** **Tag**
There should be no character after the ‘all’ tag. So, if there’s any, your **SPF record checker** will highlight it. _The inclusion of characters after the ‘all’ tag invalidates your SPF record_.
### **SPF Type DNS**
The SPF-type DNS record is deprecated as RFC7208 and is no longer supported. Instead, you should use the TXT record type to generate a **valid SPF record** for your domain.
[Image sourced](https://support.mailessentials.gfi.com/hc/en-us/articles/360015116740-How-MailEssentials-Sender-Policy-Framework-SPF-filter-works) from mailessentials.gfi.com
### **SPF Syntax Errors**
A [poorly constructed SPF record](https://support.securityscorecard.com/hc/en-us/articles/115003337866-Malformed-SPF-Record) has **syntax errors and typos** that invalidate it. Here’s what it should have-
- Beginning with _**v=spf1**_.
- Ending with the _all_ tag- _~all, -all,_ or _+all_
- No typographic errors.
### **Maximum Lookup Limit**
An email server’s resources are consumed upon each lookup, and that’s why there’s a limit of a maximum of **10 DNS SPF lookups**. The limit was imposed to avoid overloading the mail server.
Once the limit is reached, then either emails are returned or the list of authorized IP addresses is not retrieved. This gives malicious actors the opportunity to attempt [phishing attacks in your company’s name](https://www.digitalinformationworld.com/2023/04/75-e-commerce-phishing-attacks-exploit.html).
So, if you fail to be back within the limit despite making all the efforts, [AutoSPF](/)’s automatic **SPF flattening** service will resolve the issue.
### **Use of a PTR Mechanism**
The [PTR mechanism](http://www.open-spf.org/Mechanism/ptr/) is used for resolving a domain name to its corresponding IP address. Its conjunction with SPF records is deprecated due to its slow and unreliable nature. That’s why it can’t be resolved using diagnostic tools.
### **Use of the +all Tag**
An **SPF record checker** will return with a warning if your record includes a _+all_ tag. The inclusion of this tag allows anyone on the internet to send emails using your domain, and that’s not recommended. This will enable [hackers to exploit your domain](https://thehackernews.com/2023/08/phishers-exploit-salesforces-email.html) for sending fraudulent emails in your name.
### **Characters After the** **_‘all’_** **Tag**
There should be no character after the ‘all’ tag. So, if there’s any, your **SPF record checker** will highlight it. _The inclusion of characters after the ‘all’ tag invalidates your SPF record_.
### **SPF Type DNS**
The SPF-type DNS record is deprecated as RFC7208 and is no longer supported. Instead, you should use the TXT record type to generate a **valid SPF record** for your domain.
 ### **Maximum Void Lookups**
The [void lookup limit](https://mxtoolbox.com/problem/spf/spf-void-lookups#:~:text=These%20are%20sometimes%20collectively%20referred,default%20of%20two%20is%20RECOMMENDED.) was introduced in RFC7208 and indicates DNS lookups that return an empty response (NOERROR with no answers) or an NXDOMAIN response. There shouldn’t be more than **2 DNS void lookups**, and this is separate from the maximum lookup limit.
### **MX Resource Records**
The **SPF record checker** highlights the inclusion of any MX (Mail Exchange) mechanism. You may use the MX mechanism only if your MX servers are used for outgoing emails.
However, the MX mechanism does not need to be used if the servers listed in your [MX records](https://www.labnol.org/gmail-mx-records-google-workspace-230427) are only used for incoming mail.
### **Null Values**
While performing an **SPF check online**, null values are highlighted as they create problems in delivering emails to desired recipients. _You can retain them if you have added them to the record of non-email-sending domains._
### **Maximum Void Lookups**
The [void lookup limit](https://mxtoolbox.com/problem/spf/spf-void-lookups#:~:text=These%20are%20sometimes%20collectively%20referred,default%20of%20two%20is%20RECOMMENDED.) was introduced in RFC7208 and indicates DNS lookups that return an empty response (NOERROR with no answers) or an NXDOMAIN response. There shouldn’t be more than **2 DNS void lookups**, and this is separate from the maximum lookup limit.
### **MX Resource Records**
The **SPF record checker** highlights the inclusion of any MX (Mail Exchange) mechanism. You may use the MX mechanism only if your MX servers are used for outgoing emails.
However, the MX mechanism does not need to be used if the servers listed in your [MX records](https://www.labnol.org/gmail-mx-records-google-workspace-230427) are only used for incoming mail.
### **Null Values**
While performing an **SPF check online**, null values are highlighted as they create problems in delivering emails to desired recipients. _You can retain them if you have added them to the record of non-email-sending domains._