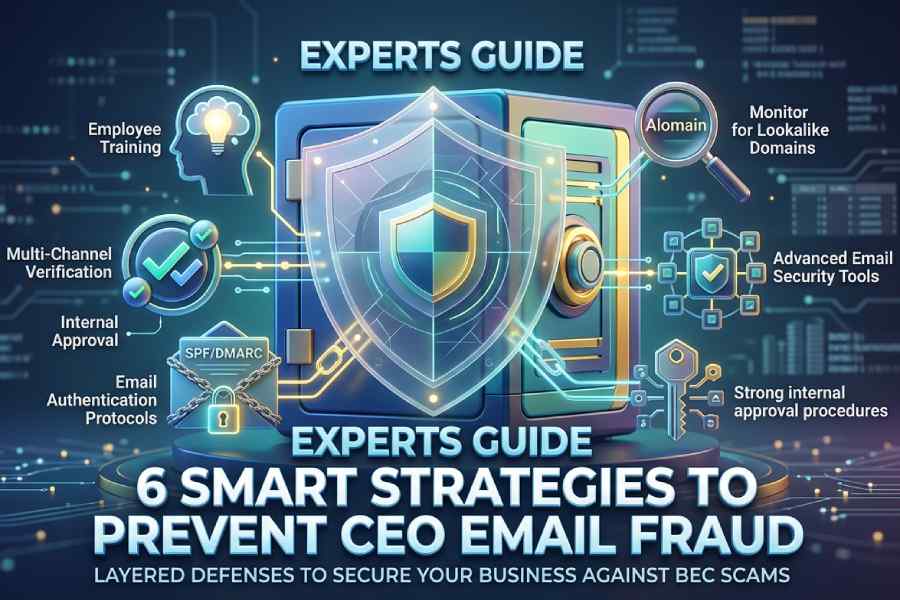
6 Smart Strategies to Prevent CEO Email Fraud

Quick Answer
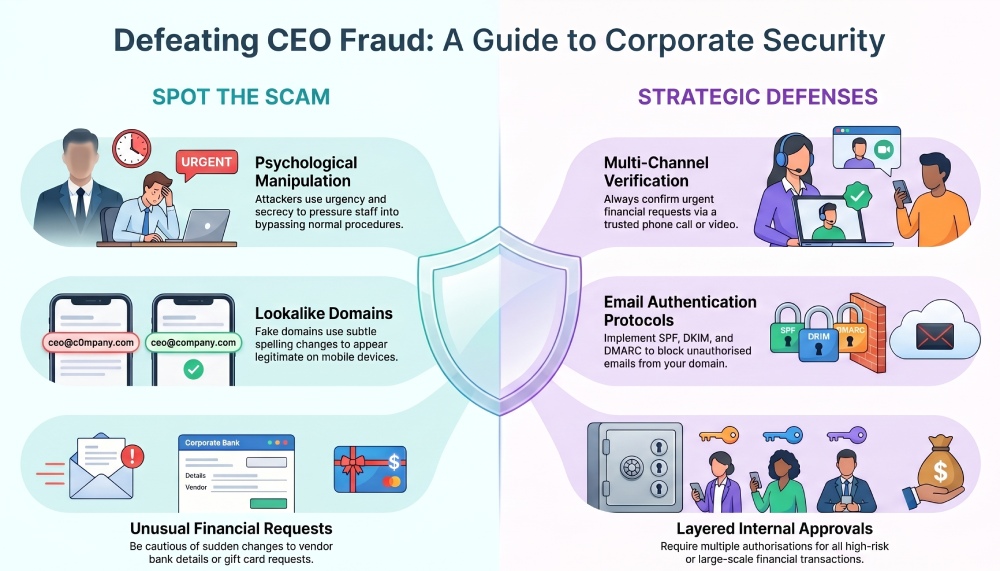
Cybercriminals are constantly improving their tactics, and one of the most damaging scams affecting businesses today is CEO email fraud. These attacks are carefully designed to look like legitimate requests from executives or senior leadership, often pressuring employees into transferring money, sharing confidential information, or approving sensitive transactions.
Cybercriminals are constantly improving their tactics, and one of the most damaging scams affecting businesses today is CEO email fraud. These attacks are carefully designed to look like legitimate requests from executives or senior leadership, often pressuring employees into transferring money, sharing confidential information, or approving sensitive transactions.
Because these messages appear urgent and authoritative, many organizations fall victim before realizing the email was fraudulent. A single successful attack can lead to major financial losses, reputational damage, and compromised customer trust.
Understanding how CEO fraud works, and how to stop it, is essential for every modern business.
What Is CEO Email Fraud?
CEO email fraud is a form of Business Email Compromise (BEC) in which attackers pretend to be a company executive, typically the CEO, CFO, or another senior leader. The goal is usually to manipulate employees into performing actions that benefit the attacker.
These emails often include:
- Fake payment requests
- Urgent wire transfer instructions
- Requests for payroll or tax documents
- Demands for confidential company information
- “Secret” or time-sensitive projects requiring immediate action
The attacker may spoof an executive’s email address, create a lookalike domain, or simply use the executive’s name in the sender field to appear authentic.
Since employees are naturally inclined to respond quickly to leadership requests, these scams can be extremely convincing.
Why CEO Fraud Is So Dangerous
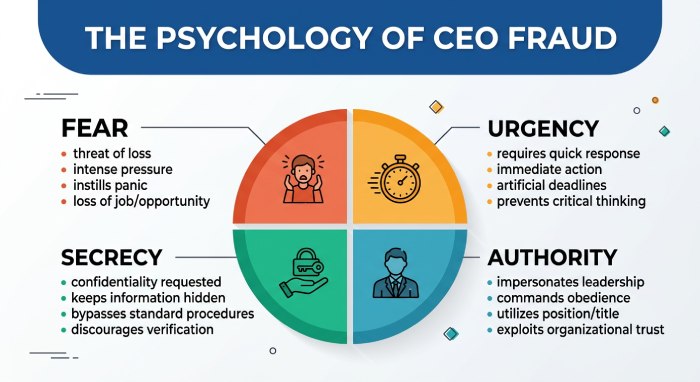
CEO fraud attacks are successful because they rely more on psychology than technology. Attackers use urgency, fear, and authority to push employees into acting without verification.
Common manipulation tactics include:
- Claiming the request is confidential
- Pressuring staff to act immediately
- Asking employees to bypass normal procedures
- Pretending the executive is traveling or unavailable
- Creating fake emergencies involving vendors or clients
Even organizations with strong cybersecurity systems can still become victims if employees are not properly trained to identify suspicious behavior.
In many cases, businesses lose substantial amounts of money within minutes because fraudulent wire transfers are processed before anyone questions the request.
1. Train Employees to Recognize CEO Fraud
Employee awareness is one of the strongest defenses against phishing and executive impersonation attacks.
Regular cybersecurity training should help staff identify warning signs such as:
- Unexpected payment requests
- Unusual urgency
- Changes in vendor banking details
- Requests for secrecy
- Misspelled email domains
- Suspicious attachments or links
Finance departments, HR teams, and executive assistants should receive advanced training because they are often primary targets.
Organizations should also run phishing simulations periodically to test how employees respond to suspicious messages in real-world scenarios.
2. Verify Financial Requests Through Another Channel
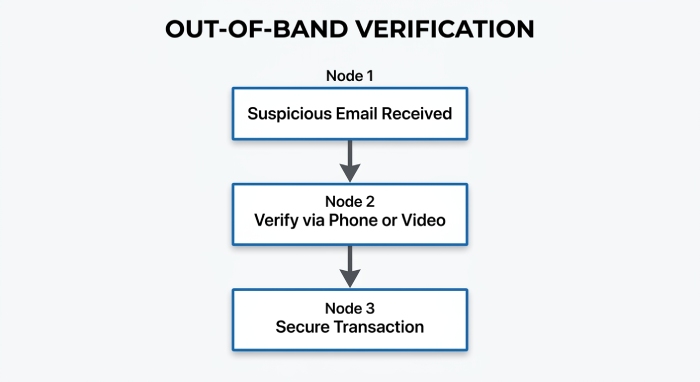
Businesses should never approve wire transfers or sensitive financial actions based solely on email communication.
A strong verification process may include:
- Phone confirmation with the executive
- Video verification
- Internal approval workflows
- Multi-person authorization for large payments
If an email requests urgent financial action, employees should independently verify the request using a trusted communication method, not by replying directly to the suspicious message.
This single step can prevent major financial losses.
3. Implement Email Authentication Protocols
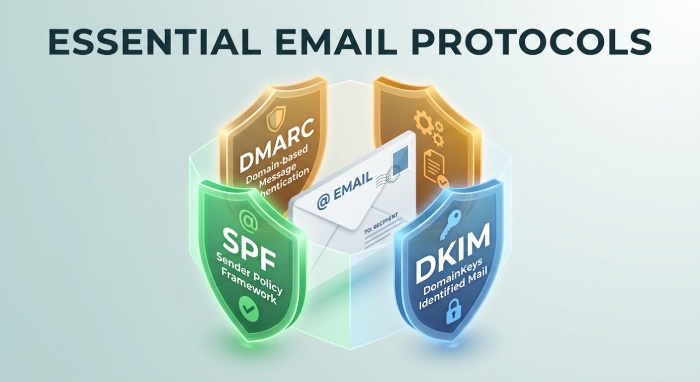
Email authentication technologies help organizations reduce spoofing and domain impersonation attacks.
Important protections include:
- SPF (Sender Policy Framework)
- DKIM (DomainKeys Identified Mail)
- DMARC (Domain-based Message Authentication, Reporting, and Conformance)
DMARC is especially valuable because it allows organizations to block unauthorized emails pretending to come from their domain.
When properly configured, these protocols can significantly reduce phishing attempts that use direct domain spoofing techniques. However, businesses should also understand that attackers may still use lookalike domains or display-name impersonation, which require additional protection layers.
4. Monitor for Lookalike Domains

Cybercriminals frequently register domains that closely resemble legitimate company domains.
For example:
- company-name.com → cornpany-name.com
- businessmail.com → businessmaiI.com
- example.org → examp1e.org
These fake domains can appear legitimate at first glance, especially on mobile devices where email addresses are less visible.
Businesses should actively monitor for suspicious domain registrations and consider purchasing similar domain variations to reduce impersonation risks.
Security teams can also configure email systems to flag messages originating from suspicious external domains that resemble internal company addresses.
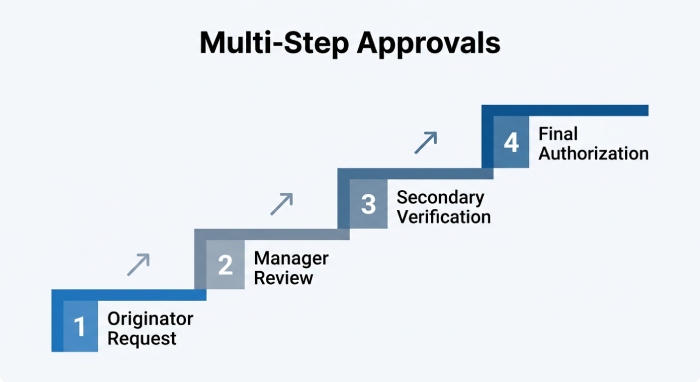
5. Strengthen Internal Approval Procedures
Weak financial controls create opportunities for attackers to exploit employees.
Organizations should establish clear policies for:
- Vendor payment changes
- International wire transfers
- Executive approvals
- Payroll updates
- Confidential data requests
No employee should have the ability to authorize high-risk transactions alone.
Implementing layered approval procedures ensures that suspicious requests receive additional scrutiny before action is taken.
6. Use Advanced Email Security Tools
Traditional spam filters are often not enough to stop sophisticated CEO fraud attempts.
Modern email security platforms can provide additional protection through:
- AI-driven phishing detection
- Behavioral analysis
- Display-name spoofing detection
- Domain similarity monitoring
- Real-time threat intelligence
Many solutions can also identify abnormal communication patterns, such as executives suddenly requesting unusual payments or sending emails outside normal business behavior.
Combining employee awareness with advanced email protection tools creates a much stronger defense against BEC attacks.
Common Signs of a CEO Fraud Email
Employees should be cautious if an email contains:
- Immediate payment demands
- Pressure to bypass procedures
- Confidential language
- Requests for gift cards or wire transfers
- Unexpected banking changes
- Poor grammar or unusual tone
- Slightly altered sender addresses
Even highly convincing emails should be verified before any sensitive action is taken.
Building a Long-Term Defense Against CEO Fraud
Stopping CEO fraud requires more than a single security solution. Businesses need a combination of:
- Employee education
- Strong email authentication
- Multi-step verification processes
- Secure financial procedures
- Ongoing threat monitoring
Attackers continuously adapt their methods, so organizations must regularly update their cybersecurity practices and train employees to recognize evolving threats.
Companies that take a proactive approach are far less likely to suffer financial damage or reputational harm from executive impersonation attacks.
CEO fraud may be one of the most effective phishing scams today, but with the right strategies in place, organizations can dramatically reduce their risk and protect both their finances and their reputation.
Topics

General Manager
Founder and General Manager of DuoCircle. Product strategy and commercial lead for AutoSPF's 2,000+ customer base.
LinkedIn Profile →