DMARC Adoption Benchmarks Across Industries Who’s Protected, Who Isn’t, and How Your Sector Really Compares

Quick Answer
Public conversation about DMARC has a framing problem. Vendor marketing tends to talk about “adoption” as if publishing a record is the finish line. The measurement data says otherwise. In December 2025, Red Sift analyzed 73.3 million domains drawn from the world’s most-used websites, major stock indices, and regulated groups.
Try Our Free DMARC Checker
Validate your DMARC policy, check alignment settings, and verify reporting configuration.
Check DMARC Record →
TL;DR
- DMARC publication is up. Enforcement isn’t. Only 14.9% of 73.3 million analyzed domains have any DMARC record at all, and just 2.5% enforce p=reject (Red Sift, December 2025).
- Only mandated sectors have reached real protection. The US federal government sits at 92% DMARC enforcement because of BOD 18-01. Most voluntary sectors are at a fraction of that (Valimail).
- Healthcare and utilities are exposed despite being high-value targets. US healthcare: 11% enforcement. US utilities: 8% enforcement. Both sit below the global average (Valimail).
- Publishing a record is not protection. Only 28.5% of domains with a DMARC record have reached p=reject, the rest are in “monitor mode” and can still be spoofed (Valimail via DMARC Report, 2024).
- The 2024-2025 mandates changed the game. Google and Yahoo (Feb 2024), Microsoft (May 2025), and PCI DSS v4.0 (Mar 2025) now require DMARC for bulk senders and payment processors (DMARC Report; Sendmarc).
- Even mandated domains are technically fragile. A 2025 survey of 713 US .gov domains found 60% had SPF errors, missing records, invalid syntax, or the 10-DNS-lookup problem, silently breaking DMARC (dmarcian).
1. The real global picture: 83.9% of domains aren’t authenticated at all
Public conversation about DMARC has a framing problem. Vendor marketing tends to talk about “adoption” as if publishing a record is the finish line. The measurement data says otherwise. In December 2025, Red Sift analyzed 73.3 million domains drawn from the world’s most-used websites, major stock indices, and regulated groups. Out of that sample, 83.9% had no visible DMARC record at all. Only 14.9% had any policy published, and of that small slice, the majority were at p=none (monitor mode). Just 2.5% of all domains, roughly 1.8 million, enforce p=reject, the only policy that actually blocks spoofed mail at the receiver.
That headline number reframes the entire conversation. When someone says “DMARC adoption is growing,” they usually mean the top row of the funnel. The bottom row, enforcement, tells a very different story. EasyDMARC’s 2026 analysis of the top 1.8 million domains by traffic found valid DMARC records grew from 523,921 in 2023 to 937,931 in early 2026, a 79% increase over three years, but still only about 52% of the top 1.8M. And across the same population, p=none remains the most common policy.
“Publishing a DMARC record is like installing a smoke alarm with the batteries still in the plastic. It tells you something happened, but it doesn’t stop anything.”
What it means: If you benchmark your organization only against “does it have a DMARC record?” you are benchmarking against the wrong question. The right benchmark is “are we at p=quarantine or p=reject, on every active domain, with aggregate reporting feeding a review process?” By that measure, the global median organization is unprotected. If you hit enforcement, you are already in the top 2.5% of the internet.
2. Sector-by-sector: the enforcement gap is enormous
Global averages hide the story. The interesting data is the variance between sectors. Valimail’s industry analysis, still the most-cited sector-by-sector enforcement breakdown, later corroborated by Sendmarc’s 2024 Cyberthreat Report, shows an enforcement spread that runs from 8% to 73% depending on which industry you’re looking at.
The table below consolidates the sector data from Valimail’s Email Fraud Landscape analysis. “Enforcement” here means p=quarantine or p=reject with no subdomain exceptions, the posture that actually prevents domain spoofing.
| Sector | Full DMARC Enforcement | Regulatory Driver |
|---|---|---|
| US federal government | 73% | BOD 18-01 (mandatory) |
| Global banks & financial services | 21% | Partial (regional) |
| Fortune 500 companies | 21% | None (voluntary) |
| Global technology | 19% | None (voluntary) |
| Billion-dollar public companies | 14% | None (voluntary) |
| US healthcare | 11% | HIPAA (indirect) |
| Global media | 10% | None |
| US utilities | 8% | None (voluntary) |
Two patterns jump out. First, enforcement tracks compulsion, not sophistication. Technology companies, the ones that build email infrastructure, sit at 19% enforcement, only marginally ahead of Fortune 500 companies as a whole. The US federal government sits at 73% not because civil servants understand DNS better than Google engineers, but because BOD 18-01 told them they had to. Second, the sectors most frequently targeted by phishing, healthcare, utilities, finance, are not the sectors with the strongest protection. US healthcare sits at 11% enforcement while simultaneously being the sector with the highest phishing exposure rate.
Update from 2024 data: Sendmarc’s 2024 Cyberthreat Report put the Fortune 500 active DMARC-use figure at 37.58%, with 15% of Fortune 500 domains having no DMARC record at all. The same report measured the global distribution of DMARC policies and found 68.2% at p=none, 12.1% at p=quarantine, and only 19.6% at p=reject. Four out of five DMARC-publishing organizations are not actually using DMARC to block fraud, they’re using it to watch fraud happen.
What it means: Your peer group’s DMARC posture is almost certainly worse than your intuition suggests. If you’re a mid-sized healthcare organization and you’re at p=none, you are not behind your sector, you are typical for your sector. That’s not reassurance; that’s a market-wide vulnerability, and attackers know it.
3. The federal mandate playbook: what BOD 18-01 actually taught us

The strongest natural experiment in DMARC deployment is the US federal government. In October 2017, DHS issued Binding Operational Directive 18-01, requiring all executive-branch civilian agencies to deploy SPF, DMARC, STARTTLS, and HTTPS with specific deadlines and the strongest policy (p=reject) for all second-level domains within one year. The GAO’s 2020 audit (GAO-20-133) then documented exactly what happened.
The headline findings are sobering for anyone who assumes mandates translate directly into outcomes. Within the 120-day deadline, only 3 of 83 federal agencies (4%) had fully addressed all of the directive’s requirements across all of their domains. One year after issuance, only 6 of 83 agencies (7%) had fully complied. The audit also observed that individual requirement completion rates were much higher, 83% to 99% depending on the specific requirement, but full end-to-end compliance across every domain simultaneously remained elusive.
And yet the aggregate result was still transformational. By 2020, Valimail measured 92% DMARC enforcement across US federal DMARC records and 75% protection across all federal domains, the highest rate of any measured cohort on the internet. The gap between 7% (fully compliant with every BOD 18-01 requirement) and 92% (at DMARC enforcement specifically) illustrates something important: DMARC enforcement is achievable quickly; end-to-end email security posture is not.
“DMARC enforcement is achievable in months. End-to-end email security posture, SPF cleanliness, DKIM everywhere, DMARC reporting actually reviewed, takes years.”
The federal playbook has evolved. In 2024-2025, CISA issued BOD 25-01, extending mandatory secure configuration baselines to Microsoft 365 and Google Workspace specifically, explicitly requiring DMARC policies within cloud productivity environments, not just on second-level domains. This matters because it acknowledges a reality most enterprises face: email doesn’t live on your mail server anymore. It lives in M365 or Google Workspace, and the DMARC alignment challenge follows you into the cloud.
The limits of mandates are visible even in the success stories. dmarcian’s September 2025 survey of 713 US government email domains found that 60% of those mandated, audited, high-scrutiny government domains had SPF errors, missing records, invalid syntax, multiple SPF records on a single domain, or records that exceed the 10-DNS-lookup limit and return PermError. When SPF silently fails, DMARC loses half of its authentication basis. A domain at p=reject with broken SPF is not the same posture as a domain at p=reject with clean SPF. The first still lets spoofed mail through if DKIM alignment is unreliable; the second does not.
What it means: If the US federal government, which has statutory authority, dedicated funding, and 7+ years of compliance scaffolding, can only reach 7% full compliance and still has 60% SPF misconfiguration rates, a private sector organization that treats DMARC as a quarterly IT task is not going to achieve enforcement on momentum alone. This is a change-management problem, not a technical one.
4. The regulatory cascade: 2024-2026 changed who has a choice
For most of DMARC’s existence (the standard has been stable since 2015 per NIST SP 800-177 Rev 1), deployment was a best-practice recommendation. Between February 2024 and March 2025, that changed. Four separate regulatory and industry forcings converged, and the effect on adoption curves is already measurable.
February 2024, Google and Yahoo bulk-sender requirements
Google and Yahoo announced that any domain sending 5,000+ daily messages to their users would be required to have SPF + DKIM + DMARC properly configured, or face delivery throttling and rejection (DMARC Report). This was the first time a consumer email provider effectively made DMARC mandatory for commercial email delivery, and because Gmail and Yahoo together account for a large share of global consumer inboxes, non-compliance is a deliverability disaster, not a theoretical risk.
March 2025, PCI DSS v4.0 enforcement date
PCI DSS v4.0, the payment card industry’s primary data security standard, took full effect on March 31, 2025 with a new DMARC requirement. Organizations handling payment card data must now implement DMARC policies set to quarantine or reject (Sendmarc 2024 Cyberthreat Report). Non-compliance carries suspension-of-processing risk, an existential threat for any organization that accepts card payments.
May 5, 2025, Microsoft bulk-sender enforcement
Microsoft matched Google and Yahoo’s requirements for Outlook.com, Hotmail.com, and Live.com. High-volume senders (5,000+ daily messages) without proper SPF, DKIM, and DMARC are now routed to junk initially and eventually rejected outright (DMARC Report). With Microsoft’s move, the three largest global email providers all enforce authentication, there is no longer a major consumer email service that accepts unauthenticated bulk mail.
2024-present, Sector and regional mandates
CISA’s BOD 25-01 extended DMARC to M365/Google Workspace in the US federal civilian branch. The UK NCSC, Canada’s CCCS, and Australia’s ASD all mandate DMARC for government domains. DORA now requires DMARC for EU regulated payment processors. The cumulative compliance matrix cited in Sendmarc’s 2024 Cyberthreat Report now includes: BOD 18-01, BOD 25-01, NIST SP 800-177, PCI DSS 4.0, GDPR, GLBA, HIPAA, CCPA, CMMC, and the Google/Yahoo/Microsoft bulk-sender rules. An organization of any meaningful size is almost certainly subject to at least one of these.
What it means: The era of DMARC as a “good idea we’ll get to” is over. For commercial email deliverability, for card payment processing, for federal contracting, for EU operations, DMARC is now a gating requirement. The question has shifted from “should we deploy DMARC?” to “how fast can we reach enforcement without breaking legitimate mail?”
5. The healthcare paradox: most targeted, least protected
No sector illustrates the gap between risk and readiness more starkly than healthcare. CISA’s April 2021 DMARC guidance for the Healthcare and Public Health sector opened with an unambiguous statement: phishing and spearphishing are “among the top attack vectors for healthcare organizations,” capable of causing “patient care impact, financial fraud, or protected health information (PHI) breaches and HIPAA fines.”
The exposure data confirms the threat model. Red Sift’s industry analysis reports that in 2024, 48% of healthcare organizations and 73% of financial institutions reported phishing attacks, and 61% of healthcare organizations lack proper protection against data breaches. This is exactly the category of attack DMARC is designed to blunt: an attacker spoofs hospital.example to send a patient a fake bill or a provider a fake credential-harvesting link. DMARC at enforcement stops that at the receiver.
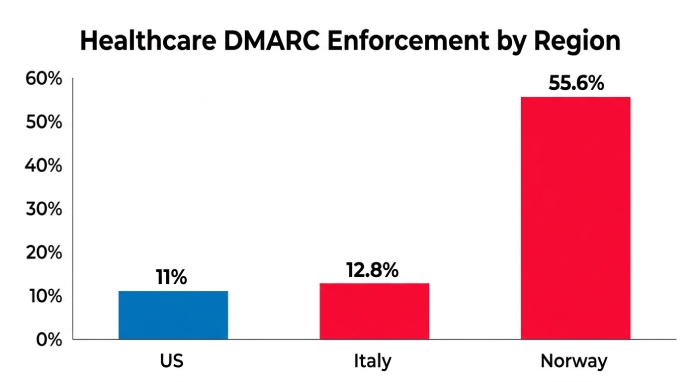
And yet US healthcare sits at 11% DMARC enforcement (Valimail). The contrast with regulated regional peers is instructive. PowerDMARC’s Norway DMARC Adoption Report 2025 found the Norwegian healthcare sector leads in strictest p=reject adoption at 55.6%, closely followed by Norwegian financial services at 44.7%. Why is Norwegian healthcare five times more protected than US healthcare? GDPR. NIS2. Direct regulator pressure on healthcare specifically, not just payment processors. Where regulators explicitly demand email authentication, healthcare organizations deliver it.
Italy tells the mirror story. PowerDMARC’s Italy 2025 report found that only 12.8% of Italian healthcare domains enforce p=reject, and 1 in 4 healthcare domains lack DMARC entirely. Same regulatory framework as Norway on paper, very different enforcement reality in practice. The pattern generalizes: healthcare adoption tracks the intensity of specific regulatory attention, not the existence of general frameworks.
“Where regulators explicitly demand email authentication, healthcare organizations deliver it. Where regulators assume they will, they don’t.
What it means: If you run email for a healthcare organization, you are not operating in a sector that will protect itself through peer pressure. The most targeted sector in cybersecurity is also one of the least authenticated. That creates an outsized opportunity for attackers, and an outsized opportunity for any single organization that moves to enforcement ahead of its peers. A hospital at p=reject with clean SPF is not just protected; it’s differentiated.
6. The SPF-lookup trap hiding inside every DMARC deployment
Here is the single most under-reported finding in the DMARC literature. dmarcian’s 2025 survey of 713 US government email domains, all of them subject to BOD 18-01 and therefore under compulsory DMARC mandate, found that 60% had SPF errors. Not DMARC errors. SPF errors: missing records, invalid syntax, multiple SPF records on one domain (which breaks SPF entirely), and, most importantly, records that exceed RFC 7208’s 10-DNS-lookup limit and return PermError.
This is a structural failure mode that most DMARC conversations skip over. DMARC evaluates whether a message passes SPF-with-alignment or DKIM-with-alignment. When your SPF record exceeds 10 DNS lookups, every include, a, mx, and redirect mechanism after the tenth returns PermError, and SPF authentication silently fails. If DKIM is also misconfigured (a common second problem), DMARC fails alignment, and a domain at p=reject starts rejecting its own legitimate mail. Mail ops rolls the policy back to p=none, the organization declares DMARC “not ready,” and the attack surface stays open.
The 10-lookup ceiling is not a theoretical concern. A typical enterprise today integrates include: mechanisms for marketing automation, transactional mail, HR platforms, CRM, helpdesk, ERP, CDN mail relay, and security vendors. Each include typically consumes 1-3 DNS lookups of its own (because includes nest). Industry tracking by Valimail found that only 28.5% of domains with a published DMARC record have reached p=reject. The rest are stuck at p=none, and SPF complexity is one of the main reasons teams don’t feel safe moving forward.
What it means: Before you tighten your DMARC policy, audit your SPF record. Use an SPF checker that counts nested lookups, not just the visible mechanisms. If you are at 8 or more, you are one vendor away from silent DMARC failure. This is the specific problem SPF flattening solves: it resolves nested includes into a compact, IP-based record that stays under the ceiling while continuing to authorize every legitimate sender, and the refresh has to be automated, because vendor IP pools change weekly.
7. The 90-day path from ‘we have DMARC’ to ‘we’re actually protected’
This is the practical question every leader reading benchmark data is actually asking: “given that my sector is under-protected, how fast can we move, and what’s the sequence?” The data supports a specific answer.
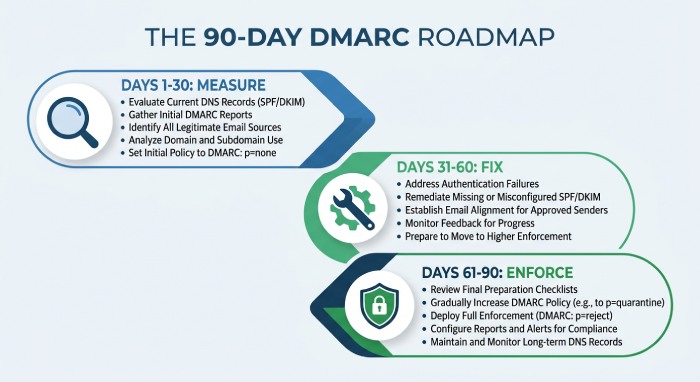
Days 1-30: Measure, don’t guess
- Run an SPF lookup audit across every sending domain and subdomain. This is step zero. Count nested lookups, not just visible include: mechanisms. If any domain is at 8 or higher, flatten it before doing anything else with DMARC. The dmarcian data says you’re almost certainly among the 60% with issues you haven’t found yet.
- Publish DMARC at p=none on every active domain, including parked and legacy domains. Attackers prefer unmonitored domains for lookalike spoofing precisely because they usually have no DMARC. Publishing a p=none record with a reporting address (rua=) costs nothing and gives you visibility into who is already impersonating you.
- Wire DMARC aggregate reports to a parser. Raw XML reports are unusable at scale. Use a DMARC analysis platform to ingest them automatically. Without this, step 2 is performative.
- Benchmark your current position against this article’s sector data. If you’re in a sector at 11%-21% enforcement and you’re at p=none, moving to enforcement puts you ahead of 80%+ of your peer group.
Days 31-60: Fix what’s broken, don’t tighten yet
- For each vendor in your aggregate reports, align or sign. For each third-party sender, either (a) add them to your SPF record via authorized-sender mechanism, (b) enable DKIM signing with your domain as the d= value, or (c) move them to a dedicated subdomain with its own policy.
- Delegate bulk mail to subdomains. Marketing, transactional, HR, each should send from its own subdomain (marketing.example.com, mail.example.com). This lets you apply different DMARC policies at different risk levels and protects your primary domain’s reputation.
- Deploy BIMI prep. BIMI, which shows your verified logo next to authenticated mail in Gmail, Apple Mail, and others, requires DMARC at p=quarantine or p=reject. Getting the artwork and VMC certificate in queue now means you can turn it on the day you reach enforcement.
Days 61-90: Move to enforcement, gradually
- Move to p=quarantine with pct=10. DMARC’s pct tag lets you apply the policy to a percentage of failing mail. Start at 10%. Read reports daily for two weeks. Look for legitimate senders that suddenly show failures you didn’t know about.
- Ramp: pct=25 → 50 → 75 → 100. Each ramp step should run for 2-3 weeks with no legitimate-mail failures before increasing. Industry guidance suggests this full ramp takes 90-180 days for complex sending environments; shorter for simpler ones.
- Move from p=quarantine pct=100 to p=reject. At this point, receiving servers silently drop mail that fails DMARC rather than delivering to spam. This is the only posture that actually stops domain spoofing. By this point, aggregate reports should show 99%+ alignment on legitimate mail.
- Lock in a quarterly authentication review. Vendors change. Subdomains appear. Marketing teams adopt new platforms. DMARC posture decays unless someone owns it. A 30-minute quarterly review of aggregate reports catches drift before it becomes a breach.
8. Bottom line: the benchmarks tell a simple story
Four data points summarize the state of DMARC in 2026. First, global publication is rising, EasyDMARC measured 79% growth in valid records between 2023 and 2026, but enforcement has barely moved; only 2.5% of domains are at p=reject. Second, only mandated sectors protect themselves; the US federal government’s 92% enforcement rate stands alone because BOD 18-01 required it. Third, the sectors most exposed to phishing, healthcare at 11% enforcement, utilities at 8%, are also the least protected, creating a systemic risk attackers are already exploiting. Fourth, 60% of even mandated government domains still have SPF errors that silently break DMARC regardless of policy.
The benchmark you should use against your own organization is not your competitors. They are almost certainly in the same underprotected state you are. The benchmark that matters is p=reject with clean SPF on every active domain, and by that measure, reaching enforcement puts you in the top few percent of the internet. The regulatory cascade of 2024-2025 (Google, Yahoo, Microsoft, PCI DSS 4.0, BOD 25-01) has removed the remaining reasons to wait. Every organization that processes payments, sends commercial email, handles federal data, or operates in a regulated European market is now subject to at least one DMARC mandate.
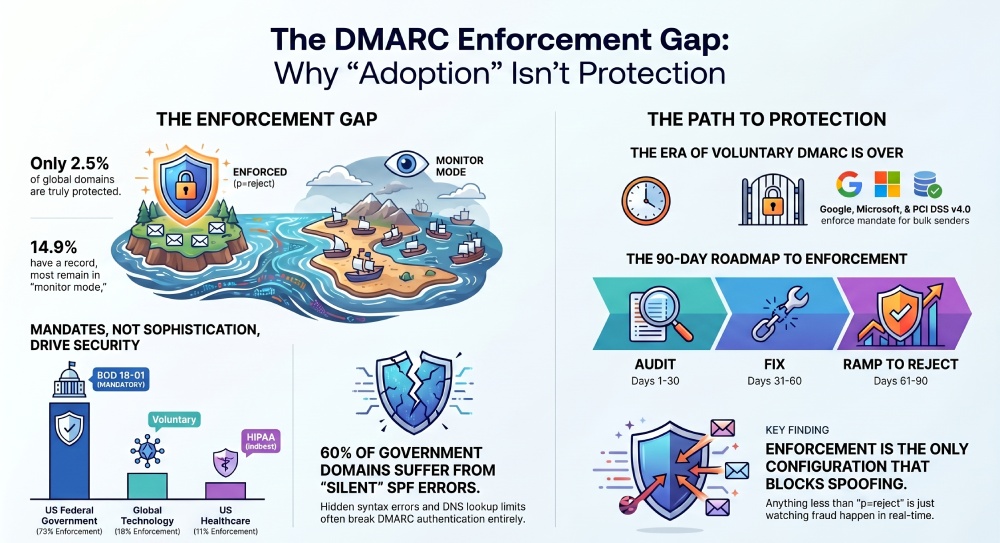
The single most useful number in this article: 28.5%. That is the percentage of domains with a published DMARC record that have actually reached p=reject. If you publish DMARC and stop there, you are in the 71.5% who are not protected, you have just turned on a monitoring dashboard. Reaching enforcement is the only configuration that blocks domain spoofing. Everything before that is just watching it happen.
References
Every statistic in this article is sourced from a publicly accessible primary-source document, US government audit reports (GAO), regulatory directives (CISA), federal standards (NIST), vendor measurement studies with documented methodology (Valimail, Sendmarc, Red Sift, EasyDMARC, PowerDMARC, dmarcian), and industry technical references. All URLs are written out in full so attribution survives format conversion.
- GAO-20-133: DHS Directives Have Strengthened Federal Cybersecurity. https://www.gao.gov/assets/gao-20-133.pdf
- CISA Cybersecurity Performance Goals Adoption Report. https://www.cisa.gov/sites/default/files/2025-01/CPG%20Adoption%20Report.pdf
- CISA BOD 18-01: Enhance Email and Web Security. https://www.cisa.gov/news-events/directives/bod-18-01-enhance-email-and-web-security
- CISA BOD 25-01: Secure Cloud Services Required Configurations. https://www.cisa.gov/news-events/directives/bod-25-01-implementing-secure-practices-cloud-services
- CISA DMARC Healthcare Guidance. https://www.cisa.gov/sites/default/files/publications/CISA%20DMARC%20HDO_040721_508.pdf
- NIST SP 800-177 Rev 1: Trustworthy Email. https://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.800-177r1.pdf
- NIST Technical Note 1945: Email Authentication Mechanisms. https://nvlpubs.nist.gov/nistpubs/TechnicalNotes/NIST.TN.1945.pdf
- Valimail Email Fraud Landscape, Over 1 Million DMARC-Enabled Domains. https://www.valimail.com/wp-content/uploads/2021/05/Research-report_-Sender-identity-movement-continues-with-over-1-million-DMARC-enabled-domains.pdf
- Sendmarc & ARMD Digital: State of Email Security & DMARC 2024 Cyberthreat Report. https://armd.digital/wp-content/uploads/2024/10/ARMD.digital-Sendmarc-2024-Cyberthreat-ReportR.pdf
- Red Sift: Achieving DMARC Adoption, A Global Approach. https://redsift.com/guides/red-sifts-guide-to-global-dmarc-adoption
- EasyDMARC 2026 Adoption & Enforcement Report. https://easydmarc.com/blog/ebook/dmarc-adoption-report-2026
- PowerDMARC Norway DMARC & MTA-STS Adoption Report 2025. https://powerdmarc.com/norway-dmarc-adoption-report/
- PowerDMARC Italy DMARC Report 2025. https://powerdmarc.com/italy-dmarc-adoption-report/
- dmarcian: Understanding CISA BOD 25-01 DMARC Requirements. https://dmarcian.com/cisa-bod-25-01-dmarc-requirements-microsoft-google/
- DMARC Report: Microsoft DMARC Requirements May 2025. https://dmarcreport.com/blog/microsoft-outlook-dmarc-requirements-may-2025
- DMARC Report: Enforcement Timeline Roadmap. https://dmarcreport.com/blog/dmarc-enforcement-timeline-none-to-reject-roadmap
Topics

General Manager
Founder and General Manager of DuoCircle. Product strategy and commercial lead for AutoSPF's 2,000+ customer base.
LinkedIn Profile →