Email Authentication in Government and Critical Infrastructure

Quick Answer
Public administration was the single most frequently targeted sector in the EU in 2024, accounting for 19% of all cyber incidents tracked by ENISA, with transport at 11% in second place (ENISA Threat Landscape 2024). That pattern continued in 2025.
A Global Compliance Report, What Works, What’s Broken, and What’s Next
TL;DR
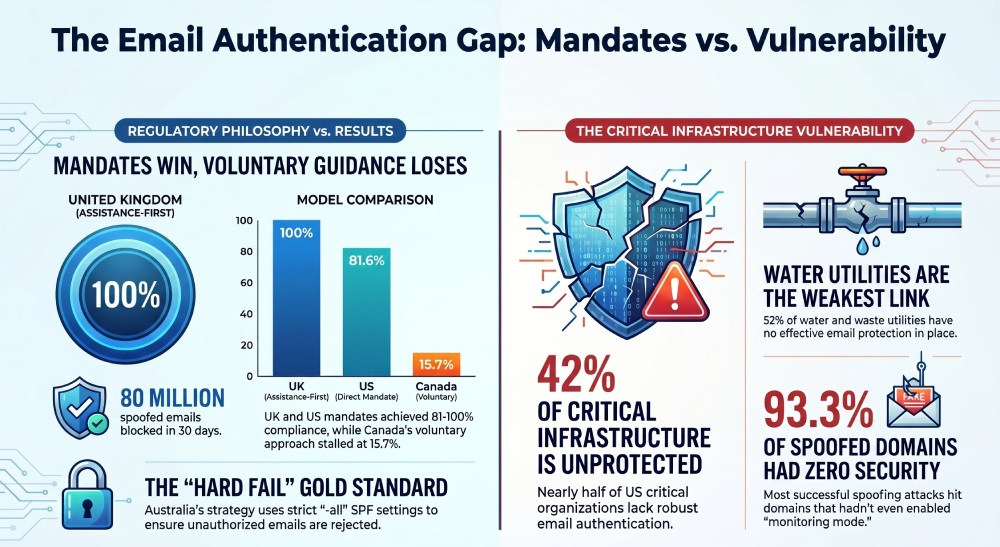
- Government mandates work, but only where they have teeth. The US reached 81.6% of .gov domains at DMARC p=reject by 2023 (Validity). The UK hit 100% strict DMARC across all central government departments by end of 2022 (NCSC ACD-6). Both followed direct-mandate models with multi-year sustained enforcement.
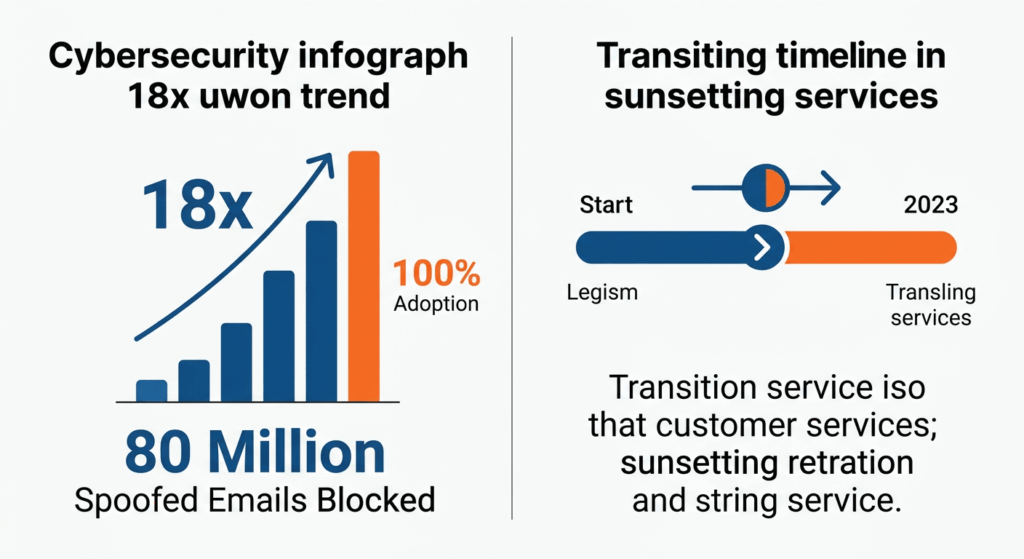
- The measurable outcome is staggering. In a single 30-day window, the UK’s Active Cyber Defence blocked over 80 million spoofed emails claiming to come from government domains (NCSC). That is authentication in action, not authentication on paper.
- Five jurisdictions, five different approaches. US (mandate-first), UK (assistance-first), Australia (embed in the ISM), EU (cascade via NIS2), Canada (voluntary). Each has produced measurable but divergent results.
- Critical infrastructure is where mandates stop working. Red Sift’s November 2025 analysis of 840 US critical-infrastructure organizations found 42% lack robust email authentication. Water and waste utilities are worst, 52% unprotected (Red Sift; WaterWorld).
- Globally, the floor is still dire. 83.9% of 73.3 million analyzed domains worldwide have no DMARC record at all (Red Sift). Only 2.5% are at p=reject.
- 93.3% of government domains that suffered email spoofing attacks had not enabled email authentication, even in monitoring mode. The authentication gap is the single largest preventable vulnerability in government email (McGuire).
1. Why government and critical infrastructure are the front lines
Public administration was the single most frequently targeted sector in the EU in 2024, accounting for 19% of all cyber incidents tracked by ENISA, with transport at 11% in second place (ENISA Threat Landscape 2024). That pattern continued in 2025. ENISA’s Public Administration Sectorial Threat Landscape documented a Q4 2024 surge, with over 40% of annual data-breach incidents in public administration occurring in a single quarter (ENISA Public Administration TL).
The targeting is not accidental. Government and critical infrastructure domains carry unique trust, citizens open emails from them, vendors process payments based on them, and emergency notifications reach public inboxes through them. A successful spoofed email from a water utility, a federal agency, or a hospital system doesn’t just produce a fraudulent transaction; it erodes the public-trust infrastructure that underlies modern governance. The result: threat actors specifically target these sectors because the impersonation payoff is highest.
The defensive response to this asymmetric risk has been uneven across jurisdictions. The United States mandated DMARC enforcement for federal agencies in 2017. The United Kingdom built a voluntary-but-incentivized assistance program. Australia embedded DMARC into its Information Security Manual. The European Union is cascading requirements through the NIS2 Directive. Canada has chosen voluntary guidance. Five approaches, five outcomes, and the differences between them are instructive for any IT leader deciding how to approach email authentication in their own jurisdiction.
What follows is a data-driven comparison: what each jurisdiction did, what measurable outcome they achieved, and what the gaps reveal about where the next five years of regulation will focus.

2. The five jurisdictions at a glance
Before digging into each case, a side-by-side comparison. All five approaches have produced measurable results, but only two (US and UK) have reached enforcement rates that approach saturation. The rest are still climbing, and the rates of climb differ dramatically by regulatory philosophy.
| Jurisdiction | Regulatory model | Key instrument | Measured outcome | Year started |
|---|---|---|---|---|
| United States | Direct mandate with enforcement deadline | CISA Binding Operational Directive 18-01 | 81.6% of .gov domains at p=reject by 2023 | October 2017 |
| United Kingdom | Assistance-first with centralized tooling | NCSC Active Cyber Defence / Mail Check | 100% central government at strict DMARC by end of 2022 | November 2016 |
| Australia | Embed in information-security baseline | ACSC Information Security Manual (ISM-1799); Essential Eight | Federally mandatory; sector-wide rates not publicly tracked | September 2022 (formal DMARC reject control) |
| European Union | Cascade through sector-wide cyber directive | NIS2 Directive / Commission Implementing Regulation 2024/2690 | Transposition ongoing; covered entities still progressing | October 2024 (NIS2 transposition deadline) |
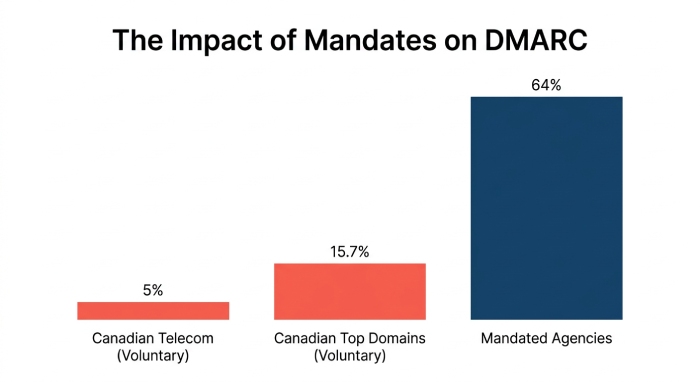
| Canada | Voluntary guidance without direct mandate | CCCS advisory; sector-specific recommendations | 15.7% at enforcement; telecom lowest at 5% | N/A, voluntary |
What it means: Mandates with teeth produce saturation-level compliance. Voluntary guidance, even well-intentioned, consistently produces compliance rates of 15-20% at enforcement. The gap between the UK (100%) and Canada (15.7%) is not a technical gap. It is a regulatory-philosophy gap. Any jurisdiction looking at the UK’s result should understand that the precondition was not a better protocol, it was a mandate backed by government-provided tooling and a named program officer in every department.
3. United States, the mandate-first model
On October 16, 2017, the US Department of Homeland Security (now CISA) issued Binding Operational Directive 18-01, making the United States the first major government to mandate DMARC at full enforcement (p=reject) across federal executive branch civilian agencies. The directive established a four-step compliance ladder: 30 days to submit an Agency Plan of Action, 90 days to publish valid SPF/DMARC at minimum p=none with aggregate reporting, 120 days to disable SSLv2/SSLv3 and 3DES/RC4 ciphers on mail servers, and 12 months to reach full DMARC p=reject for all second-level domains and mail-sending hosts.
The trajectory was measurable from the start. By September 2018-11 months after BOD 18-01 was issued, Agari’s analysis showed DMARC fully implemented on 64% of 1,144 federal domains at p=reject, with 83% having at least a p=none policy. In the same period, the Fortune 500 had two-thirds (67%) with no DMARC policy of any kind. The US government, long criticized for cybersecurity lag, was outperforming the Fortune 500 by more than 2x on one of the most important security protocols available.
“Setting a DMARC policy of ‘reject’ provides the strongest protection against spoofed email, ensuring that unauthenticated messages are rejected at the mail server, even before delivery.”
, CISA, Binding Operational Directive 18-01
By 2023, six years in, the US federal DMARC posture had reached 81.6% of .gov domains at strict p=reject enforcement. This is the highest sustained DMARC-enforcement rate of any comparable domain set, public or private, anywhere in the world. It represents the most mature authentication deployment at scale that exists.
But the story is not uniformly triumphant. The Government Accountability Office’s GAO-20-133 audit of February 2020, a government-auditing-government assessment of BOD 18-01, found that while DHS directives were ‘often effective in strengthening federal cybersecurity,’ both ‘agencies and DHS didn’t always complete the directives’ actions on time’ and that ‘DHS did not consistently ensure that agencies fully complied with the directives.’ The mandate’s effectiveness depended as much on enforcement discipline as on the directive’s text.
What it means: The US model is mandate-first, tracking-second, naming-and-shaming-third. The compliance ladder (30/90/120/365 days) is the most-copied deployment pattern in subsequent government mandates. The 81.6% enforcement rate is the ‘what sustained enforcement looks like’ benchmark that every IT leader should be able to quote. But the GAO’s critique is equally important: a mandate without consistent enforcement is a mandate that produces inconsistent results. Any jurisdiction attempting to copy BOD 18-01 should plan for the enforcement apparatus, not just the directive text.
4. United Kingdom, the assistance-first model
The UK’s approach was different from the outset. In November 2016, a year before BOD 18-01, the UK government launched the Active Cyber Defence (ACD) programme, with the stated goal of ‘tackling in a relatively automated and transparent way, a significant proportion of the cyber attacks that hit the UK.’ At the center of ACD was Mail Check, a free NCSC-provided platform for UK public-sector, academic, and charity organizations to assess their email security posture and implement DMARC.
The strategic difference mattered. The US said: comply or face political consequence. The UK said: we’ll provide the tools, the dashboard, and the tactical support, and we’ll measure who uses them. By 2022, that approach had reached a landmark result. 100% of all UK central government departments had adopted a strict DMARC policy, up from 91% at the end of 2021. Six years into ACD, the UK had achieved saturation across central government without a CISA-style mandate.
The operational outcome is quantifiable and striking. In the 30 days immediately before the NCSC ACD Year 6 report was published, over 80 million spoofed emails were blocked from UK central government domains, as a direct result of strict DMARC implementation. That is 2.7 million blocked spoof attempts per day, every day, from a single sector. In the early ACD program, June 2017 alone, DMARC blocked 30.3 million spoofed emails claiming to come from UK government systems, with an average of 4.5 million blocked per month in that early period. The before-and-after is a roughly 18x increase in daily blocked spoof volume after six years of sustained mandate.
“Many cyber-attacks exploit the trust that exists between the government and its citizens. By implementing DMARC, the NCSC set out to make it harder for the cybercriminals to exploit people in this way.”
, Lawfare, evaluating the UK Active Cyber Defence Program
The UK model produced a second-order outcome that is harder to measure but easier to feel: the Mail Check user base grew to approximately 17,000 UK organizations relying on the service for DMARC reporting and email security visibility. NCSC’s own analysis found that a school subscribed to Mail Check was over 4 times more likely to have a securely configured DMARC policy than an equivalent non-subscribed school. Government-provided tooling directly and measurably improved sector-wide security posture, even in sectors (schools, charities) that were not mandated to participate.
On March 24, 2025, NCSC Mail Check discontinued DMARC aggregate reporting (RUA), DMARC Insights, DKIM checks, and TLS reporting. On March 31, 2026, Mail Check and Web Check will be fully retired. NCSC’s stated rationale: ‘ACD 2.0’ pivots from government-provided services to supporting a mature commercial cybersecurity marketplace. The 17,000 organizations that depended on Mail Check now need commercial alternatives.
What it means: The UK model shows that assistance-first can match or exceed mandate-first outcomes, but only when assistance includes funded government tooling, named department-level program officers (the Government Security Centre for Cyber was critical), and multi-year sustained investment. The retirement of Mail Check also illustrates the risk: government-provided tooling creates dependencies that need transition planning when the program sunsets. For any organization still on Mail Check, the runway to March 31, 2026 is short. The market has matured, but the transition window is not infinite.
5. Australia, the embed-in-the-baseline model
Australia’s approach differs from both the US and UK. Rather than issuing a standalone email authentication mandate, the Australian Cyber Security Centre (ACSC) embedded DMARC requirements directly into the Information Security Manual, the foundational document that governs cybersecurity for federal government entities. As of September 2022, ISM control ISM-1799 states plainly: ‘Incoming emails are rejected if they do not pass DMARC checks.’ That single sentence carries the regulatory weight of a mandate, but lives inside a broader document that governs every aspect of federal information security.
The ACSC Strategies to Mitigate Cyber Security Incidents, first published in 2017 and updated through 2023, takes the approach a step further, calling specifically for ‘hard fail’ SPF TXT and DMARC DNS records to mitigate emails that spoof the organisation’s domain. The word ‘hard fail’ is distinctive Australian regulatory phrasing: it means SPF records must end in -all, not the weaker ~all softfail posture. Combined with DMARC at enforcement, this produces one of the strictest authentication postures of any government.
The enforcement mechanism is the Protective Security Policy Framework (PSPF), which mandates that government entities implement the Essential Eight at Maturity Level 3. Essential Eight is ACSC’s baseline cyber-resilience framework, and while it is ‘not a formal compliance standard,’ implementation is mandatory for Australian federal government agencies under the ISM. In practice, this means DMARC at enforcement is embedded in the baseline security requirement every federal agency must meet, without a standalone directive naming it.
What it means: Australia’s model is structurally different from both the US and UK. Rather than a directive that sits alongside other regulations, DMARC is woven into the foundational security document that governs everything. The advantage: compliance becomes an integrated part of ‘what it means to be secure,’ not an add-on project. The disadvantage: public-sector adoption rates are harder to track because DMARC is one control among hundreds in the ISM, not a standalone measurement. For any government or regulated-industry IT leader, the lesson is that where you place the control matters as much as the control’s strength. Australia’s embedding approach is the most durable of the five models, a single future administration can’t ‘revoke DMARC’ without gutting the entire ISM.
6. European Union, the cascade-via-directives model
The European Union does not (yet) have a directly comparable DMARC mandate to CISA BOD 18-01. What it has is NIS2, the Network and Information Security Directive, specifically Commission Implementing Regulation (EU) 2024/2690 of 17 October 2024, which establishes cybersecurity risk management requirements for entities operating in critical sectors. DMARC is not named in the directive as a specific requirement; it is incorporated by reference through ENISA’s technical implementation guidance and the broader baseline of ‘cybersecurity risk management measures.’
The EU’s chosen mechanism is the cascade: a broader cybersecurity directive that imposes obligations across many sectors simultaneously, with technical bodies (ENISA) providing the implementation detail. The ENISA Threat Landscape 2024 identified public administration as the most targeted sector (19% of all EU cyber incidents), with data-breach incidents in public administration surging in Q4 2024 to account for over 40% of annual data incidents in a single quarter (ENISA Public Administration TL). The regulatory urgency is not theoretical; it is reactive to measured threat.
The 2025 threat landscape intensified the pressure. ENISA’s October 2025 Threat Landscape report analyzed 4,875 cybersecurity incidents across the July 2024 to June 2025 reporting window, and documented that AI-supported phishing campaigns ‘reportedly represented more than 80 percent of observed social engineering activity worldwide, with adversaries leveraging jailbroken models, synthetic media and model poisoning techniques to enhance their operational effectiveness.’ The threat model that NIS2 is responding to is not static; it is compounding.
“The threat landscape depicted in this edition reflects how the cyber threat landscape is shifting toward mixed, possibly convergent pressure, with fewer single high impact incidents, and more continuous, diversified and convergent campaigns that collectively erode resilience.”
, ENISA Threat Landscape 2025
What it means: The EU’s cascade model produces a slower initial ramp but a broader eventual scope than the US or UK approaches. NIS2 covers critical sectors the US BOD 18-01 doesn’t touch, private-sector finance, energy, transport, health, digital infrastructure, and more. For EU organizations in NIS2-covered sectors, DMARC at enforcement is not currently named as a specific requirement, but it is an effectively mandatory control under the ‘cybersecurity risk management measures’ umbrella. Expect that ambiguity to resolve in favor of explicit DMARC language in subsequent ENISA guidance. The organizations that implement proactively are ahead of the curve; the organizations waiting for a named directive are already behind.
7. Canada and the cost of voluntary guidance
Canada provides the control case. The Canadian Centre for Cyber Security (CCCS) promotes DMARC adoption through guidance documents, advisory notes, and sector-specific recommendations, but without the direct mandate CISA issued, the tooling NCSC provided, or the regulatory embedding Australia chose. The result is predictable and measurable.
Analysis of 140 top Canadian domains across sectors found that only 52.8% had DMARC records at all, with just 15.7% at enforcement (p=quarantine or p=reject). The Canadian telecommunications sector, which operates the critical communications infrastructure of the country, had the LOWEST DMARC adoption in the dataset: only 5% of telecom domains at enforcement. For context, the US federal government reached 64% at enforcement within 11 months of BOD 18-01. Canada’s telecom sector, eight years into the global DMARC conversation, sits at 5%.
The gap is not a technical gap. Canadian telecoms have access to the same protocols, the same tooling, and the same operational expertise as their US, UK, and Australian counterparts. The gap is regulatory. Voluntary guidance without enforcement mechanisms consistently produces single-digit enforcement rates in sectors that have strong non-regulatory reasons to adopt (liability, brand protection, customer trust), because in the absence of an active mandate, those reasons compete with every other competing priority in IT budget discussions. Mandates win those arguments. Recommendations lose them.
What it means: The Canadian case is the counterfactual for everyone else. The question to ask in any jurisdiction is: in the absence of a direct mandate or equivalent regulatory mechanism, what mechanism would compel an organization to prioritize DMARC over the other 47 things demanding their IT budget? Most often, the answer is ‘nothing’, and the compliance numbers reflect that. This is the argument for why jurisdictions considering voluntary-only approaches should either add enforcement mechanisms or commit to government-provided tooling substantial enough to overcome the opportunity-cost friction.
8. The critical infrastructure gap, where mandates stop working
Here is where the five-jurisdiction analysis gets uncomfortable. Government mandates work well for government domains. They have been substantially less effective for the private-sector critical infrastructure that governments depend on. The gap is measurable and growing.
Red Sift’s November 2025 analysis of 840 US critical-infrastructure organizations, the most current sector-specific dataset available, found that 42% lack robust email authentication. The sector-by-sector breakdown is revealing:
- Energy: 44.5% at DMARC enforcement. The best-performing critical-infrastructure sector, reflecting heightened awareness following high-profile attacks on pipelines and grid operators. Named companies in the analysis include Chevron.
- Chemical: 35.7% at enforcement. Particularly concerning given the sector’s reliance on hazardous materials and complex supply chains, where a single spoofed email to the wrong operator could have catastrophic physical consequences. Named companies include Dow.
- Water and waste: 52% of organizations unprotected. The worst-performing critical-infrastructure sector by a significant margin. Named entities include American Water and the Boston Water and Sewer Commission. Water and waste utilities rely heavily on public-facing email for customer communication, emergency notifications, and inter-utility coordination, and more than half have no effective authentication in place (WaterWorld analysis).
“For critical infrastructure industries in the United States, DMARC is not optional, it is a cornerstone of operational security, particularly as AI continues to be weaponized by bad actors.”
, Red Sift analysis of US critical-infrastructure email security
The gap compounds. Research analysis of municipal and government domain security found that 93.3% of government domains that suffered email spoofing attacks had not enabled email authentication even in monitoring mode, despite these protocols being free to implement and requiring only DNS configuration changes. The overwhelming majority of successful government-domain spoofing attacks would have been mitigated by controls that cost nothing and take hours to deploy. The authentication gap is not a resource problem. It is an attention problem.
The regulatory response is emerging unevenly. CISA has issued guidance specifically for the water and wastewater sector through joint publications, but without a directive mandate equivalent to BOD 18-01. The EU’s NIS2 Directive covers critical infrastructure explicitly but cascades through risk-management requirements rather than naming DMARC. Australia’s ISM applies to federal agencies but not to private critical-infrastructure operators. The UK retired Mail Check in part because the public-sector saturation was complete and the remaining gap was in private critical infrastructure that the government program was not sized to serve.
What it means: If you operate in water, energy, chemical, or any other critical-infrastructure sector, regardless of jurisdiction, your peer organizations are less protected than you might assume. The compliance story you hear from vendors is about government mandates and enterprise adoption trends. The operational reality is that 42% of your peers are not authenticated at enforcement. This is both a risk to share with your board (sector-wide weakness increases your own risk via supply-chain and lookalike-domain attacks) and a concrete advantage for any operator who gets ahead. The next wave of regulation, which industry analysts forecast will specifically target critical infrastructure in 2026 and 2027, will arrive faster if you can demonstrate sector leadership now.
9. What to do now, regardless of jurisdiction
The global data makes three things clear. First, the protocols are mature and free. Second, the mandates are expanding. Third, the critical-infrastructure gap is the next regulatory frontier. For any government agency, critical-infrastructure operator, or regulated-industry IT leader, the path forward is structurally the same regardless of jurisdiction, with small adaptations for the specific regulatory mechanism that applies to you.
Step 1, Know your regulatory posture
- Identify your applicable mandate. US federal civilian agency? CISA BOD 18-01 applies. UK public sector? NCSC guidance (and the March 31, 2026 Mail Check retirement deadline). Australia federal agency? ISM-1799 and Essential Eight at Maturity Level 3. EU NIS2-covered entity? Commission Implementing Regulation 2024/2690 applies. PCI DSS 4.0 applies if you handle card data in any jurisdiction.
- Document your compliance gap. Not in aspirational terms but in measurable terms. What percentage of your active sending domains are at p=none? At p=quarantine? At p=reject? Without rua= reporting configured? This is your baseline.
- For critical infrastructure operators: benchmark against your sector. If you are a water utility and your DMARC posture is stronger than 52% of peers, that is a talking point for your board. If it is weaker, that is a risk register item.
Step 2, Fix the plumbing
- Audit SPF lookup counts across every sending domain. Use a tool that counts nested DNS lookups. If any active domain is at 8 or higher, you are one SaaS addition away from silent PermError. SPF flattening to stay under the 10-lookup RFC 7208 ceiling is the single most common bottleneck in government-scale deployments.
- Publish DMARC records on every active domain, including parked and legacy domains. Attackers specifically target unmonitored domains for lookalike spoofing. Parked-domain authentication is free and immediately closes a major attack vector.
- Wire aggregate DMARC reports (rua=) to a parser you actually read. Raw XML is unusable at government scale. Commercial DMARC analysis platforms, especially for UK organizations transitioning off Mail Check before March 31, 2026, are now table stakes, not optional.
- Enable DKIM signing on every sending source with YOUR domain in the d= parameter. Vendor-signed mail that uses the vendor’s domain as d= will fail DMARC alignment even when DKIM itself passes. This is the step most government deployments skipped in their first compliance push and the one causing most of the current alignment failures.
Step 3, Progress to enforcement on a measurable schedule
- Publish a timeline that mirrors CISA BOD 18-01’s four-step ladder: 30 days to initial plan, 90 days to p=none with reporting, 120 days to infrastructure hygiene (TLS, cipher disablement, PTR records), 12 months to p=reject across all second-level domains. This is the most-proven deployment ramp in government DMARC; copy it.
- Move progressively: p=none → p=quarantine pct=10 → 25 → 50 → 75 → 100 → p=reject. Each step should run for 2-3 weeks with no legitimate-mail failures before advancing. Complex government environments take 12-18 months. Critical-infrastructure environments with extensive OT-adjacent systems may take longer.
- Instrument the progression with metrics the board can see. NCSC’s ’80 million blocked spoofs in 30 days’ framing works at the board level because it translates technical controls into operational impact. Report blocked attempts, not just records published.
Step 4, Extend beyond your organization
- If you are a government agency: help your critical-infrastructure partners. The gap between government-domain DMARC (US 81.6% at reject, UK 100% strict) and critical-infrastructure DMARC (52% of water utilities unprotected) is where the next attacks will land. Joint advisories, shared tooling, and sector-specific guidance are cheaper than incident response.
- If you are a critical-infrastructure operator: coordinate within your sector. Water utility associations, chemical sector councils, and energy ISACs all have DMARC-specific programs now forming. Participate. Sector-level peer pressure has proven more effective than voluntary individual effort.
- For UK public-sector organizations specifically: plan the Mail Check transition now. The March 31, 2026 retirement deadline is short. The commercial DMARC tooling market has matured, but a rushed migration in Q1 2026 will produce more gaps than a planned migration started in Q2 2025.
10. The bottom line: government mandates are the floor, not the ceiling
The five-jurisdiction comparison makes something clear that gets lost in most DMARC coverage. Government email authentication is no longer a frontier; it is a solved problem in the jurisdictions that chose to solve it. The US federal .gov space at 81.6% p=reject. The UK central government at 100% strict DMARC. Australia’s federal agencies bound by ISM-1799. These are done deals. The remaining work in those sectors is maintenance, not deployment.
But the work beyond government, in the critical infrastructure, regulated industries, and private-sector services that citizens depend on just as much, is where the next decade of regulation will focus. The 42% of US critical-infrastructure organizations lacking robust authentication, the 52% of water utilities exposed, the 5% of Canadian telecom at enforcement, these are the gaps that the next mandate wave will close, whether by direct regulation (NIS2’s expansion, sector-specific CISA directives) or by market pressure (Google, Yahoo, Microsoft’s bulk-sender requirements already forcing private-sector adoption).
The organizations that get ahead of this wave will have two advantages when the mandate arrives: their deployment will be complete, and their operational lessons will make them the obvious peer-group leaders. The organizations that wait will face the same compliance ramp everyone else faces, with less runway, fewer government-provided resources, and an AI-enabled threat landscape that has already made more than 80% of social engineering attacks AI-supported. Waiting is the expensive option.
The single number to remember: 93.3% of government domains that suffered email spoofing attacks had not enabled email authentication, even in monitoring mode. The protocols are free. The tooling is mature. The mandates are expanding. The only remaining question is whether your organization is in the prepared third, the catching-up half, or the exposed rest. The data above tells you which one.
References
Every statistic in this article is sourced from a publicly accessible government document or the peer-reviewed research built on it. Primary sources include CISA Binding Operational Directive 18-01 (the foundational US federal DMARC mandate), the GAO’s 2020 audit of its effectiveness, NCSC’s Active Cyber Defence Year 6 full report (the canonical UK government DMARC dataset), ENISA’s Threat Landscape reports and public administration sectorial analysis, Australia’s ACSC Information Security Manual, the EU’s NIS2 implementing regulation with ENISA technical guidance, Red Sift’s November 2025 analysis of 840 US critical-infrastructure organizations, and Validity’s analysis of .gov domain enforcement. All URLs are written out in full so attribution survives format conversion.
- CISA BOD 18-01: Enhance Email and Web Security. https://cyber.dhs.gov/assets/report/bod-18-01.pdf
- CISA BOD 18-01 overview page. https://www.cisa.gov/news-events/directives/bod-18-01-enhance-email-and-web-security
- GAO-20-133: DHS Directives Have Strengthened Federal Cybersecurity. https://www.gao.gov/assets/gao-20-133.pdf
- SecurityWeek, DMARC Fully Implemented on Two Thirds of U.S. Government Domains. https://www.securityweek.com/dmarc-fully-implemented-two-thirds-us-government-domains/
- Validity, The Government Mandated a Strict DMARC Policy for .gov Domains. https://www.validity.com/blog/the-government-mandated-a-strict-dmarc-policy-for-gov-domains-how-did-they-do/
- NCSC Active Cyber Defence, The Sixth Year (Summary). https://www.ncsc.gov.uk/files/acd6-summary.pdf
- NCSC Active Cyber Defence, The Sixth Year (Full Report). https://www.ncsc.gov.uk/files/ACD6-full-report.pdf
- Lawfare, Evaluating the U.K.’s Active Cyber Defence Program. https://www.lawfaremedia.org/article/evaluating-uks-active-cyber-defence-program
- dmarcian, NCSC DMARC Changes and Mail Check Alternatives. https://dmarcian.com/ncsc-dmarc-changes-mail-check-alternatives/
- ACSC, Guidelines for Email (Information Security Manual). https://www.cyber.gov.au/resources-business-and-government/essential-cyber-security/ism/cyber-security-guidelines/guidelines-email
- ACSC, Strategies to Mitigate Cyber Security Incidents. https://www.cyber.gov.au/sites/default/files/2023-03/PROTECT%20-%20Strategies%20to%20Mitigate%20Cyber%20Security%20Incidents%20(February%202017).pdf
- Australian Government PSPF 10, Safeguarding Information from Cyber Threats. https://www.protectivesecurity.gov.au/sites/default/files/2019-11/pspf-infosec-10-safeguarding-information-cyber-threats.pdf
- ENISA Threat Landscape 2024. https://securitydelta.nl/media/com_hsd/report/690/document/ENISA-Threat-Landscape-2024.pdf
- ENISA Threat Landscape 2025. https://www.enisa.europa.eu/sites/default/files/2025-11/ENISA%20Threat%20Landscape%202025.pdf
- ENISA Sectorial Threat Landscape: Public Administration 2024. https://www.enisa.europa.eu/sites/default/files/2025-12/ENISA%20Public%20Administration%20TL%202024%20-%20v1.1.pdf
- ENISA Technical Implementation Guidance on NIS2 Cybersecurity Risk Management. https://www.enisa.europa.eu/sites/default/files/2025-06/ENISA_Technical_implementation_guidance_on_cybersecurity_risk_management_measures_version_1.0.pdf
- PowerDMARC, DMARC Canada Adoption Report. https://powerdmarc.com/canada-dmarc-adoption-2021/
- Red Sift, Global DMARC Adoption Guide. https://redsift.com/guides/red-sifts-guide-to-global-dmarc-adoption
- Red Sift / Hydrocarbon Processing, 42% of U.S. Critical Infrastructure Exposed. https://hydrocarbonprocessing.com/news/2025/11/42-of-us-energycritical-infrastructure-providers-exposed-to-weaponized-ai-and-email-attacks/
- WaterWorld, Water and waste utilities most exposed to email security threats. https://www.waterworld.com/water-utility-management/news/55331378/new-report-finds-water-and-waste-utilities-most-exposed-to-email-security-threats
- McGuire, SPF, DKIM, DMARC: The Email Authentication Trinity (Municipal Analysis). https://www.clintmcguire.com/blog/spf-dkim-dmarc-the-email-authentication-trinity/
- PowerDMARC, Email Security Predictions 2026. https://powerdmarc.com/email-security-predictions-2026/
Topics

General Manager
Founder and General Manager of DuoCircle. Product strategy and commercial lead for AutoSPF's 2,000+ customer base.
LinkedIn Profile →