The State of Email Spoofing and Phishing in 2026 What the Data Really Shows, and What to Do About It

Quick Answer
For most of the last decade, annual cybercrime reports read like incremental trendlines. That framing no longer fits. In April 2026, the FBI’s Internet Crime Complaint Center released its 2025 Internet Crime Report, and the numbers are a discontinuity, not a trend.

TL;DR
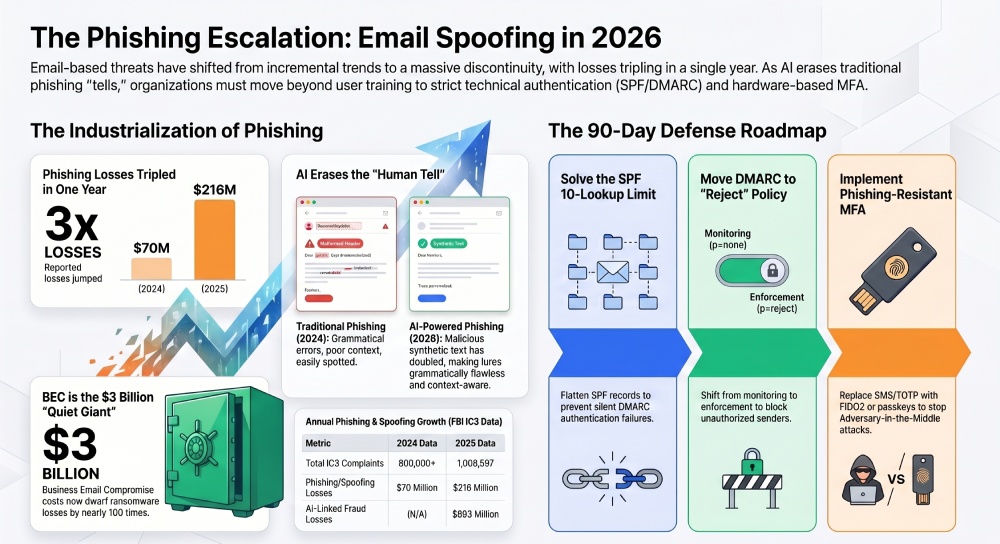
- Phishing and spoofing are growing, not shrinking. The FBI logged 191,561 phishing/spoofing complaints in 2025, more than twice the next crime type, and losses from that single category tripled in one year, from $70M to $216M (IC3 2025).
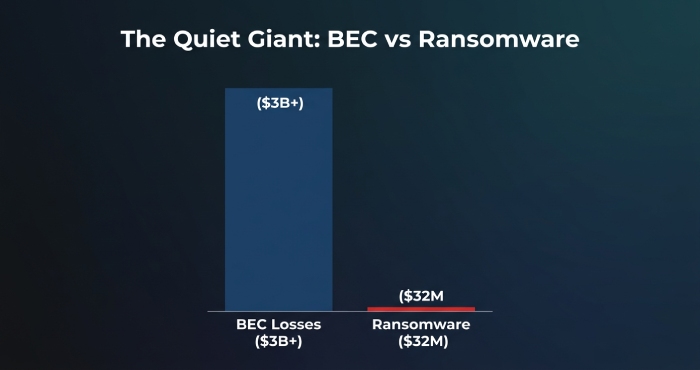
- BEC is still the big-dollar attack. Business Email Compromise alone cost US victims $3.05 billion in 2025 across 24,768 complaints, and the ten-year global total has now crossed $50 billion (IC3; Travelers).
- AI is industrializing phishing. Synthetically generated text in malicious emails doubled in two years (Verizon DBIR 2025), and the FBI logged $893M in AI-linked fraud losses in a single year (IC3 2025).
- The human element is still the weak point. Around 60% of breaches involve a human element (DBIR), and 85% of UK businesses hit by a cyber attack identify phishing as the vector (UK Cyber Security Breaches Survey 2025).
- Technical hygiene remains uneven. Academic measurement across the top million email-hosting domains found only ~54% publish a valid SPF record and far fewer enforce DMARC (University of Illinois research). This is the gap SPF flattening exists to close.
- What to do now. Move DMARC from p=none to enforcement, flatten SPF to stay under the 10-lookup limit, roll out phishing-resistant MFA, and train for the AI-era threats your filters still let through. Specifics are in the “What to do next” section below.
1. The scale has shifted from “big” to “unignorable”
For most of the last decade, annual cybercrime reports read like incremental trendlines. That framing no longer fits. In April 2026, the FBI’s Internet Crime Complaint Center released its 2025 Internet Crime Report, and the numbers are a discontinuity, not a trend. In a single year the IC3 received 1,008,597 complaints totaling $20.877 billion in losses, a 26% year-over-year increase in reported losses, on top of a 33% increase the year before (IC3 2024). Annual losses have now quintupled in five years.
Phishing and spoofing led every other crime category by a wide margin. The IC3 counted 191,561 phishing/spoofing complaints in 2025, more than twice the second-place category. Even more telling for defenders: reported losses from phishing/spoofing complaints alone tripled year-over-year, from $70,013,036 in 2024 to $215,843,126 in 2025 (IC3 2025). When a category both dominates volume and triples in dollar losses, it means attackers are not just running more campaigns, they are extracting more value per campaign.
“When a crime category both dominates volume and triples in dollar losses, attackers are not just running more campaigns, they are extracting more value per campaign.”
This is not a US-only story. The ENISA Threat Landscape 2025 analyzed roughly 4,900 curated incidents across the EU and found that social engineering, primarily phishing, vishing, malspam, and malvertising, accounted for approximately 60% of all observed cases. The UK government’s Cyber Security Breaches Survey 2025 found that 85% of UK businesses and 86% of UK charities identified phishing as the most disruptive attack type they faced. In Australia, the ACSC’s 2024-25 Annual Cyber Threat Report logged over 84,700 cybercrime reports, one every six minutes, with average self-reported business costs up 50% overall and 219% for large businesses.
What it means: Every major Western government’s 2025 reporting cycle tells the same story in different languages. Phishing and spoofing are not a tail-end risk. They are the dominant mode of financially motivated attack, they are getting more expensive per incident, and the growth is global. If your security narrative still frames phishing as “one of several” threats, that framing is out of date by roughly two annual reporting cycles.
2. BEC is the quiet giant, and it’s mostly a spoofing problem
Ransomware gets the headlines. Business Email Compromise gets the money. The IC3’s 2025 report recorded 24,768 BEC complaints totaling $3,046,598,558 in adjusted losses, nearly 100 times the $32.3M attributed to ransomware in the same year (IC3 2025). Travelers, a cyber-insurance carrier with visibility into actual claim patterns, notes in its Q2 2025 Cyber Threat Report that global reported BEC losses over the past decade have now crossed $50 billion, and that BEC or social-engineering fraud represented nearly half of all cyber claims in the past five years.
The anatomy of a BEC attack is where the technical connection to SPF, DKIM, and DMARC becomes inescapable. Attackers do not “hack” wire transfers. They send an email that looks like it came from the CFO, the title company, or a trusted vendor, and they rely on the recipient’s mail server to deliver that email to the inbox. When receiving servers cannot verify the sender through SPF, DKIM, and DMARC, the attack works. When they can verify, and the domain owner has set an enforcement policy, the attack fails silently at the perimeter.
The APWG’s Q1 2025 Phishing Activity Trends Report put hard numbers on the infrastructure side of BEC. Gmail was used for 73.5% of the free-webmail accounts scammers set up for BEC in the quarter, with Microsoft’s webmail a distant second at 13.8%. That asymmetry matters operationally: if you are a receiving organization, the vast majority of BEC lures will arrive from a gmail.com address masquerading as someone you trust, which is exactly the case DMARC alignment checks are designed to catch.
Attack economics are also shifting. The APWG Q3 2025 report documented that the average amount requested in a wire-transfer BEC attack dropped from $128,980 in Q4 2024 to $48,115 by Q3 2025, while attack volumes rose 57% in a single quarter. The APWG attributes the volume surge partly to a group it has dubbed “Scripted Sparrow,” which uses automation to generate per-victim PDF attachments and reply-chain lures. The read: BEC is industrializing. Lower-per-hit dollar asks combined with higher volume is the signature of an automated attacker lowering the bar for “good enough” targeting.
What it means: If BEC is industrializing and more than 70% of the lures are arriving from free webmail accounts, an organization’s most leveraged single defense is email authentication that actually enforces policy, not just publishes it. This is the specific failure mode SPF flattening and DMARC alignment exist to fix: the moment your SPF record exceeds 10 DNS lookups, DMARC authentication silently fails, and the receiver is left to guess whether a lookalike email is genuine. That guess is where BEC losses come from.
3. AI did not invent phishing. It made it cheaper, cleaner, and faster.
Three independent data sources agree on the same point from different angles. First, the Verizon 2025 DBIR reports that synthetically generated text in malicious emails has doubled over the past two years. Second, the IC3 logged 22,364 AI-related fraud complaints with $893,346,472 in losses in 2025, including $30M+ in AI-enabled BEC losses specifically (IC3 2025). Third, IBM’s Cost of a Data Breach Report 2025 found that 97% of AI-related security breaches involved AI systems lacking proper access controls, meaning the exposure is not just AI-generated attacks but AI deployments that are themselves misconfigured.
The practical translation: the three traditional tells of a phishing email, awkward grammar, odd phrasing, cultural mismatch, are being erased. A single well-prompted language model can produce a morning’s worth of grammatically flawless, context-aware lures that pass the human sniff test. The Microsoft Digital Defense Report 2025 notes that Microsoft now screens roughly 5 billion emails per day for malware and phishing and analyzes 15,000+ identity risk detections daily. At that scale, attacker-side tooling and defender-side tooling are both running at machine speed, and the defender’s only reliable advantage is cryptographic identity verification, not human judgment.
“The three traditional tells of a phishing email, awkward grammar, odd phrasing, cultural mismatch, are being erased. The defender’s only reliable advantage is cryptographic identity verification, not human judgment.”
The Microsoft CISO Executive Summary reinforces the point with a clean breakdown: of observed breaches investigated by Microsoft’s Detection and Response Team, 28% were initiated through phishing or social engineering, the single largest initiation category, ahead of unpatched web assets (18%) and exposed remote services (12%). Phishing is not winning because it is exotic. It is winning because it is the cheapest reliable way into a network, and the attacker’s cost curve just dropped.
What it means: Security awareness training is necessary but no longer sufficient. You cannot out-train an LLM that produces unlimited, grammatically perfect, context-specific bait. The durable countermeasures are technical: enforce DMARC, eliminate SPF PermErrors, adopt phishing-resistant MFA (FIDO2/passkeys), and invest in inbox-side signals that tell recipients whether a sender is cryptographically verified, BIMI, verified sender indicators, and the like.
4. The quiet deliverability killer: the SPF 10-lookup limit
There is a failure mode specific to email authentication that most non-email-engineers never hear about, and that almost guarantees inconsistent DMARC outcomes in enterprises: the RFC 7208 limit of 10 DNS lookups per SPF evaluation. Every include, a, mx, and redirect mechanism in your SPF record counts as one lookup. Cross 10 and your SPF returns a PermError. At PermError, SPF authentication fails, and because DMARC relies on SPF (or DKIM) passing with alignment, your DMARC enforcement fails silently as well. Legitimate mail starts getting quarantined or rejected, and spoofed mail that should have been caught slips through.
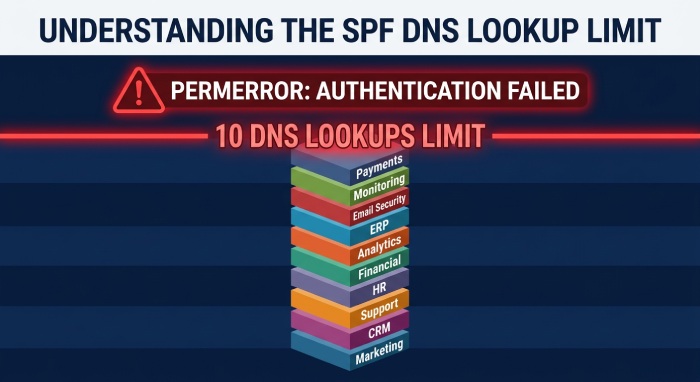
Why does this matter now more than ever? Because the average enterprise has never relied on more third-party senders than it does today. Marketing automation, transactional mail, HR platforms, CRM, helpdesk, ERP, security vendors, CDN mail relays, each typically wants its own SPF include. Academic measurement by researchers at the University of Illinois across the Alexa top million email-hosting domains found that only about 54% publish a valid SPF record, and far fewer configure DMARC with an enforcing policy (Wang et al., University of Illinois). In other words: nearly half of the internet’s most-used domains are not cleanly authenticated at all, and of the half that are, many are one vendor addition away from tipping past 10 lookups.
This is not a theoretical risk. USENIX Security 2025 research on SMTP smuggling, a technique that exploits differences in how email servers parse message boundaries to deliver spoofed messages past SPF, DKIM, and DMARC, found that 19 public email services, 1,577 private email services, five open-source mail packages, and one commercial email gateway remained vulnerable nearly two years after the original vulnerability was publicly disclosed (Wang et al., USENIX Security 2025). Even when the building blocks exist, implementation gaps keep spoofing viable.
What it means: If you have not recently audited your SPF record for DNS-lookup count, and if your DMARC policy is still p=none, you are running the same defense posture as the majority of organizations that will show up in next year’s breach reports. Fixing this is one of the highest-leverage email-security changes available, and it does not require buying a larger stack. It requires flattening the record and moving DMARC to enforcement.
5. What a successful attack actually costs
IBM’s Cost of a Data Breach Report 2025, the 20th annual edition of the study and based on research from Ponemon Institute, puts the US average cost of a data breach at an all-time record of $10.22 million, while the global average declined 9% to $4.44 million. The US surge is attributed in part to AI-driven phishing and deepfake attacks. Australia’s ACSC 2024-25 fact sheet reports average self-reported business cost per cybercrime report at A$80,850, up 50% year-over-year, with large businesses seeing a 219% jump.
For a single incident at the pointy end, consider the case from the IC3’s 2025 report: in April 2025, the FBI Portland office was notified that a city government office in Oregon had lost over $6 million in a single BEC incident. The funds were recovered in full, but only because the IC3 Recovery Asset Team had already flagged the fraudulent recipient account from a prior March 2025 incident. In 2025 overall, the RAT initiated 3,900 Financial Fraud Kill Chain actions covering $1.16 billion in attempted theft and froze $679 million, a 58% recovery rate (IC3 2025). That 58% is the ceiling of post-incident recovery, not a floor. Prevention at the email layer costs a fraction of a percent of that.
The WEF Global Cybersecurity Outlook 2025 captures the leadership view of this shift cleanly: 72% of respondents say cyber risks have risen in the past year, and phishing, social engineering, and identity theft climbed to the top of personal cyber-risk rankings. When 72% of global business leaders agree on a risk trajectory, the budget conversation is no longer whether to invest but where the marginal dollar goes.
6. What to do next: a practical 30/60/90-day plan
The remainder of this article translates the data above into a concrete sequence. This plan is ordered by leverage per hour of work, not by theoretical completeness. Each step is a change that, based on the evidence above, measurably reduces the probability that a phishing or spoofing attack succeeds against your organization.

Days 1-30: Stop the silent failures
- Audit your SPF record for the 10-lookup limit. Run every sending domain and every subdomain through an SPF checker that counts nested includes, not just the ones visible in your TXT record. If you are at 8 or more, you are one vendor away from PermError.
- Flatten SPF if you are at or near the limit. SPF flattening resolves nested includes into a compact, IP-based record that stays under the DNS-lookup ceiling while continuing to authorize every sender you care about. Automate the refresh, vendor IP pools change constantly, so static flattening breaks within weeks.
- Publish a DMARC record, even at p=none, on every active domain, including parked and legacy domains. Parked domains are attacker-preferred for lookalike spoofing precisely because they usually lack DMARC. Publishing even a p=none record with an rua reporting address is a prerequisite for every later step.
- Turn on DMARC aggregate reporting and actually read the reports. The reports tell you which third-party senders are failing SPF or DKIM alignment. You cannot move to enforcement safely without this visibility.
Days 31-60: Move to enforcement
- Fix every legitimate sender that is failing alignment. For each vendor in the aggregate reports, either align their SPF by including your domain in their authorized senders, enable DKIM signing with your domain as the signing domain, or move the sender to a dedicated subdomain with its own policy.
- Move DMARC from p=none to p=quarantine on a subdomain first. Test enforcement against a lower-risk subdomain (like a transactional-mail subdomain) for two weeks before applying to the organization’s primary domain.
- Progress to p=quarantine and then p=reject on the primary domain. By this point aggregate reports should show 99%+ alignment on legitimate mail. Anything failing at this point is almost certainly an attacker, which is exactly the outcome DMARC enforcement is designed to produce.
- Roll out phishing-resistant MFA for all privileged accounts. The 2025 DBIR found that prompt-bombing shows up in 14% of incidents and that Adversary-in-the-Middle techniques are growing. SMS and TOTP MFA are bypassed routinely. FIDO2, passkeys, and hardware security keys are not.
Days 61-90: Close the human-layer gap
- Run phishing simulations calibrated to the AI-era threat. Simulations that still test for misspelled subject lines are training users for 2018. Use lures that mirror what the APWG Q2 2025 report documents: reply-chain hijacks, convincing vendor invoices, and QR-code payloads.
- Teach verification, not detection. A rule like “all wire-transfer changes require a callback to a pre-registered phone number” is more durable than “look for grammar mistakes.” It is also specifically designed to catch the BEC pattern documented in the IC3 2025 report.
- Add BIMI if you have reached DMARC enforcement. BIMI displays a verified brand logo next to authenticated emails in supporting inboxes, giving recipients a positive indicator of legitimacy rather than asking them to spot fakes. It is only available to domains at p=quarantine or p=reject, an additional incentive to complete Days 31-60.
- Set up quarterly authentication health reviews. Vendors change. New subdomains appear. New marketing platforms get adopted. DMARC and SPF posture decays unless someone owns it. A 30-minute quarterly review of aggregate reports catches drift before it becomes a breach.
7. The bottom line
Three data points sum up the 2025 landscape. First, phishing and spoofing are now the dominant cyber-fraud vector by both complaint volume and dollar growth, losses tripled in a single year (IC3 2025). Second, attackers are automating and the human layer’s marginal advantage is evaporating (Verizon DBIR 2025; Microsoft 2025). Third, only about half of internet-facing email domains are even cleanly authenticated, and a meaningful fraction of those have quietly exceeded the 10-DNS-lookup limit that makes their DMARC enforcement a fiction (UIUC research).
The good news inside those three points is that the fix is well-understood and does not depend on a new product category. It depends on cleanly configured SPF within the lookup limit, cleanly signed DKIM, DMARC at enforcement rather than p=none, and MFA that survives an Adversary-in-the-Middle attack. Organizations that do those four things consistently show up in breach reports dramatically less often. Those that treat email authentication as “something the mail team handled years ago” keep showing up in the loss columns of the reports this article is built on.
If you read only one number from this article, read this one: in 2025, phishing/spoofing losses tripled while total cybercrime losses grew 26%. Every defense posture built on the assumption that phishing is “one of several threats” is now calibrated to a world that no longer exists.
References
Every statistic in this article is sourced from a publicly accessible primary-source document, government reports, academic research, NGO consortium reports, and major institutional research departments. All URLs are written out in full so the attribution survives format conversion.
- FBI IC3 2025 Internet Crime Report. https://www.ic3.gov/AnnualReport/Reports/2025_IC3Report.pdf
- FBI IC3 2024 Internet Crime Report. https://www.ic3.gov/AnnualReport/Reports/2024_IC3Report.pdf
- Verizon 2025 Data Breach Investigations Report, Executive Summary. https://www.verizon.com/business/resources/reports/2025-dbir-executive-summary.pdf
- APWG Phishing Activity Trends Report, Q1 2025. https://docs.apwg.org/reports/apwg_trends_report_q1_2025.pdf
- APWG Phishing Activity Trends Report, Q2 2025. https://docs.apwg.org/reports/apwg_trends_report_q2_2025.pdf
- APWG Phishing Activity Trends Report, Q3 2025. https://docs.apwg.org/reports/apwg_trends_report_q3_2025.pdf
- ENISA Threat Landscape 2025. https://www.enisa.europa.eu/sites/default/files/2026-01/ENISA%20Threat%20Landscape%202025_v1.2.pdf
- UK Cyber Security Breaches Survey 2025. https://doc.ukdataservice.ac.uk/doc/9404/mrdoc/pdf/9404_cyber_security_breaches_survey_2025_gov.uk.pdf
- IBM Cost of a Data Breach Report 2025. https://www.bakerdonelson.com/webfiles/Publications/20250822_Cost-of-a-Data-Breach-Report-2025.pdf
- Microsoft Digital Defense Report 2025. https://cdn-dynmedia-1.microsoft.com/is/content/microsoftcorp/microsoft/msc/documents/presentations/CSR/Microsoft-Digital-Defense-Report-2025.pdf
- Microsoft Digital Defense Report 2025, CISO Executive Summary. https://cdn-dynmedia-1.microsoft.com/is/content/microsoftcorp/microsoft/bade/documents/products-and-services/en-us/security/CISO-Executive-Summary-MDDR-2025.pdf
- ACSC Annual Cyber Threat Report 2024-25. https://www.cyber.gov.au/sites/default/files/2025-10/Annual%20Cyber%20Threat%20Report%202024-25.pdf
- ACSC 2024-25 Fact Sheet for Businesses. https://www.cyber.gov.au/sites/default/files/2025-10/Annual%20Cyber%20Threat%20Report%202024-25%20factsheet%20for%20businesses%20and%20organisations.pdf
- WEF Global Cybersecurity Outlook 2025. https://reports.weforum.org/docs/WEF_Global_Cybersecurity_Outlook_2025.pdf
- Travelers Q2 2025 Cyber Threat Report. https://www.corvusinsurance.com/hubfs/Ransomware_Reports/Q2_25_Travelers_Cyber_Threat_Report.pdf
- Wang et al., ‘Towards Understanding the Adoption of Anti-Spoofing Protocols in Email Systems’ (University of Illinois). https://gangw.web.illinois.edu/survey.pdf
Wang et al., ‘Email Spoofing with SMTP Smuggling’ (USENIX Security 2025). https://gangw.cs.illinois.edu/smtp-usenix25.pdf
Topics

General Manager
Founder and General Manager of DuoCircle. Product strategy and commercial lead for AutoSPF's 2,000+ customer base.
LinkedIn Profile →