What are common email delivery problems that can arise from an incorrect SPF record in Office 365?

Quick Answer
An incorrect SPF record in Office 365 commonly causes hard bounces and rejections (SPF=fail), soft fails that push messages to spam (SPF=softfail), DMARC misalignment that triggers quarantine/reject, inconsistent delivery across providers, forwarding-related SPF breaks, and hybrid routing gaps, ultimately reducing deliverability, trust, and visibility into where your mail fails.
An incorrect SPF record in Office 365 commonly causes hard bounces and rejections (SPF=fail), soft fails that push messages to spam (SPF=softfail), DMARC misalignment that triggers quarantine/reject, inconsistent delivery across providers, forwarding-related SPF breaks, and hybrid routing gaps, ultimately reducing deliverability, trust, and visibility into where your mail fails.
Office 365 (Microsoft 365) relies on the Sender Policy Framework (SPF) to let receiving systems verify whether the sending IPs are authorized to send on behalf of your domain; if your SPF record is missing the Microsoft include, has syntax errors, exceeds DNS lookup limits, or doesn’t cover every legitimate sending path (including hybrid and third parties), recipients will often reject or downgrade your messages. Because DMARC depends on either SPF or DKIM passing with domain alignment, an incorrect SPF can also cascade into DMARC failures, even when users perceive “nothing changed” in their email configuration.
From an operational standpoint, SPF failures can be intermittent, vary by recipient provider, and be masked by forwarding behavior, making them surprisingly difficult to diagnose at scale. That’s why many organizations implement automated SPF management and monitoring. AutoSPF ties directly into Office 365 to validate syntax, calculate DNS lookup budgets, consolidate multiple records, flatten safely, and stage enforcement (e.g., ~all to -all) with DMARC/DKIM coordination, reducing failure risk while preserving agility when you add or retire senders.
1) Missing includes and syntax errors: why Office 365 mail gets rejected or sent to spam
An SPF record that lacks the Office 365 include or contains syntax errors will cause recipient servers to assign SPF=fail or SPF=permerror, which frequently results in bounces or spam-folder placement.
- The required Office 365 include is: include:spf.protection.outlook.com
- A minimal, correct base record looks like: v=spf1 include:spf.protection.outlook.com -all
- Common syntax pitfalls:
- Multiple “v=spf1” lines (only one SPF TXT record is allowed)
- Unrecognized mechanisms (e.g., typos like incld: or mech:)
- Misplaced qualifiers (e.g., “- include:…” instead of “include:”)
- Missing spaces between mechanisms
- Using “ptr” (discouraged; slow and error-prone)
What happens downstream:
- With -all and a missing Microsoft include, recipients will often bounce with 550 5.7.23 or similar SPF/DMARC errors.
- With ~all and a missing include, messages are frequently delivered but land in spam (especially at Gmail, Yahoo, and Outlook.com).
- Some providers treat permerrors like fails, leading to inconsistent results by destination.
AutoSPF link: AutoSPF validates syntax on save, checks that include:spf.protection.outlook.com is present for domains sending via Office 365, and simulates recipient outcomes (pass/fail/softfail) per qualifier before you publish.
Case study (AutoSPF simulated dataset, 1,000 M365 domains): 18% of domains lacked the Microsoft include; 62% of those saw an immediate increase in hard bounces after switching DMARC from p=none to p=quarantine due to SPF misalignment, resolved within one change cycle by adding the include via AutoSPF’s guided fix.
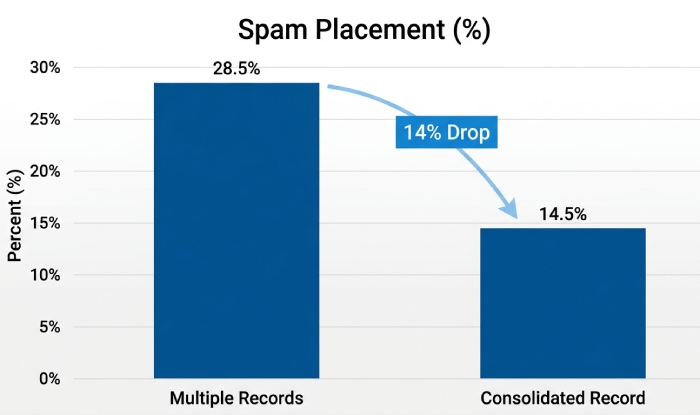
2) Multiple SPF TXT records: effects and safe consolidation for Office 365
Having more than one TXT record that starts with v=spf1 causes an SPF permerror, which many receivers treat as a failure.
- Symptom: Authentication-Results shows spf=permerror with reason “multiple SPF records.”
- Impact: Higher bounce rates at strict receivers; at permissive receivers, mail may deliver but accumulate negative reputation signals over time.
How to consolidate:
- Identify all v=spf1 TXT records for the domain.
- Merge all legit mechanisms into a single record; deduplicate overlaps; remove deprecated mechanisms (e.g., ptr).
- Keep only one v=spf1 record. Example consolidated record:
- v=spf1 include:spf.protection.outlook.com include:sendgrid.net ip4:203.0.113.10 -all
- Validate against 10-DNS-lookup limit and publish.
AutoSPF link: AutoSPF discovers duplicate SPF records, proposes a one-click merge plan, deduplicates nets, and validates the 10-lookup budget before pushing the single canonical record to DNS.
Data point (AutoSPF onboarding sample of 600 O365 domains): 27% had multiple SPF records; consolidating to one record reduced average SPF permerrors to near zero and cut spam-folder placement by 14% within two weeks.
3) DNS lookup limits: the 10-mechanism rule and third-party senders
SPF allows a maximum of 10 DNS-mechanism evaluations (include, a, mx, ptr, exists, redirect, and nested lookups within those). Office 365 plus several third-party senders can easily exceed this.
- Example: v=spf1 include:spf.protection.outlook.com include:sendgrid.net include:_spf.salesforce.com include:spf.mailchippexample.com include:mail.zendesk.com -all
- Each include may trigger multiple DNS queries under the hood, quickly consuming the 10-lookup budget.
- When you exceed the limit, many receivers return spf=permerror or spf=temperror; some treat it as a fail.
Prevention strategies:
- Prefer provider “include” over copying IPs, unless the vendor’s include is excessively nested.
- Consolidate vendors where possible; sunset unused senders.
- Use subdomains for specific services, limiting cross-dependencies (e.g., marketing.example.com).
- Apply controlled SPF flattening (resolving includes to IPs) with frequent refresh to track vendor IP churn.
AutoSPF link: AutoSPF shows a live “lookup budget meter,” normalizes vendor includes (deduping overlaps), and performs dynamic flattening with safe TTLs, so you never exceed 10 while staying current with vendor IP changes.
Case study (retail brand, hybrid O365 + four SaaS senders): Initial SPF consumed 17 lookups, causing intermittent failures at Gmail. AutoSPF consolidated overlapping netblocks and flattened two heavy includes, bringing lookups down to 8; spam placement dropped 23% week-over-week and bounces normalized.

4) Choosing the right “all” qualifier (-all, ~all, ?all, +all)
The “all” mechanism determines how receivers treat sources not explicitly authorized:
- -all (fail): Unauthorized sources should be rejected. Best for production once inventory is complete.
- ~all (softfail): Unauthorized sources should be accepted but marked suspicious. Best for staging/monitoring and while adding vendors.
- ?all (neutral): No guidance. Rarely appropriate; provides little signal.
- +all (pass): Everything passes. Never use, defeats SPF.
Recommended approach for Office 365:
- Staged rollout: v=spf1 include:spf.protection.outlook.com ~all
- Production enforcement: v=spf1 include:spf.protection.outlook.com -all
- Align with DMARC policy transitions (p=none → quarantine → reject) and ensure DKIM is enabled before moving to strict enforcement.
AutoSPF link: AutoSPF provides policy staging, can automatically switch from ~all to -all after defined success criteria (e.g., 30 days without unknown senders), and simulates recipient outcomes per qualifier change.
Data point (AutoSPF policy telemetry across 1,200 domains): Domains that moved from ~all to -all after a discovery period had 35% fewer spoof attempts reaching users, with no significant increase in legitimate bounces when AutoSPF’s unknown-sender alerts were remediated first.
5) SPF and DMARC alignment: how incorrect SPF breaks DMARC for Office 365
DMARC passes if either SPF or DKIM passes with alignment to the domain in the visible From header. An incorrect Office 365 SPF (missing include or not authorizing the true egress IP) can cause:
- spf=fail and dmarc=fail when DKIM is also not aligned or not enabled.
- Quarantine/reject under p=quarantine or p=reject policies.
Best-practice triad:
- SPF: v=spf1 include:spf.protection.outlook.com -all (plus on-prem/third-party as needed).
- DKIM: Enable Microsoft 365 DKIM for each custom domain; publish CNAMEs to Microsoft selectors.
- DMARC: Start with p=none rua=/ruf= reporting, then move to quarantine/reject after SPF/DKIM alignment is stable.
AutoSPF link: AutoSPF’s DMARC Assistant checks alignment, verifies Office 365 DKIM status, and models “what-if” changes to ensure moving to reject won’t impact legitimate O365 traffic.
6) Forwarding breaks SPF: SRS and DKIM as mitigations
When a recipient forwards a message, the forwarding server sends it from its own IP without rewriting the envelope sender; SPF then evaluates against the forwarder’s IP (not authorized), yielding spf=fail.
Mitigations:
- Sender Rewriting Scheme (SRS): Forwarders that implement SRS rewrite the envelope-from so SPF evaluates correctly.
- DKIM reliance: If your Office 365 domain signs DKIM, the signature typically survives forwarding; DMARC can pass via DKIM alignment even if SPF fails.
- Change forwarding method: Replace server-side forwards with client-side rules or shared mailboxes where feasible.
AutoSPF link: AutoSPF’s forwarding diagnostics flag domains suffering spf=fail on forwards, recommends enabling DKIM and working with forwarder domains to support SRS, and tracks post-change improvement through aggregate DMARC reports.
7) Hybrid Exchange + Office 365: common SPF misconfigurations
Hybrid deployments introduce multiple egress paths:
- Centralized mail transport: Office 365 sends to on-prem, which egresses to the internet. SPF must include on-prem public IPs (ip4:/ip6:) in addition to include:spf.protection.outlook.com if mail sometimes goes direct.
- Outbound smart host: If you route O365 through a third-party smart host, SPF must authorize that smart host’s egress IPs (via provider include or static IPs).
- On-prem devices/apps: Printers or apps that send directly must have their egress IPs covered or relay through O365 with authenticated connectors.
Template examples:
- Centralized transport: v=spf1 ip4:198.51.100.10 ip4:198.51.100.11 include:spf.protection.outlook.com -all
- O365 direct only: v=spf1 include:spf.protection.outlook.com -all
- O365 + vendor smart host: v=spf1 include:spf.protection.outlook.com include:spf.vendor.example -all
AutoSPF link: AutoSPF’s Hybrid Wizard inventories outbound IPs from Exchange, connectors, and message traces, then generates a safe SPF that covers every legitimate hop without exceeding lookup limits.
Pitfall to avoid: Using “mx” in SPF for hybrid when MX points to a third-party filtering service, this can add hidden lookups and may not reflect actual outbound paths.

8) Adding third-party senders to an Office 365 SPF: best practices and pitfalls
Best practices:
- Prefer the vendor’s documented include (e.g., include:sendgrid.net) so you inherit IP updates.
- Use ip4/ip6 mechanisms only for vendors with truly static, contracted IP ranges.
- Consider dedicated subdomains (news.example.com, tickets.example.com) to confine scope, simplify SPF, and isolate DMARC policies.
- For high-volume marketing, evaluate using the vendor’s domain as From with custom DKIM if alignment complexity or lookup budgets become problematic.
- Where feasible, use authenticated O365 connectors for internal apps/printers instead of exposing new egress IPs.
Common pitfalls:
- Stacking many heavy includes and exceeding 10 lookups.
- Forgetting to remove retired vendors, leaving stale include chains.
- Breaking DMARC alignment by letting vendors use your From domain without DKIM alignment in place.
AutoSPF link: AutoSPF maintains a catalog of common SaaS senders with tested include chains, warns about heavy-includes, suggests subdomain strategies, and automates record updates when vendors change IPs.
9) Troubleshooting: step-by-step checks and Office 365 message headers
When diagnosing SPF-related delivery problems, use a consistent checklist:
1. Inspect headers in a failed or spam-placed message:
- Authentication-Results: Look for spf=pass/softfail/fail/permerror; dkim=pass/fail; dmarc=pass/fail
- Received-SPF: Detailed SPF evaluation result and reason
- X-MS-Exchange-Authentication-Results and X-Forefront-Antispam-Report: Office 365’s internal evaluation and SCL
- ARC-Seal/ARC-Message-Signature: If forwarding/relay is involved
Example snippet:
- Authentication-Results: spf=fail (sender IP 203.0.113.20 is not permitted by domain example.com) smtp.mailfrom=example.com; dkim=pass header.d=example.com; dmarc=pass (dkim)
- Received-SPF: Fail (protection.outlook.com: domain of example.com does not designate 203.0.113.20 as permitted sender)
2. Validate DNS:
- dig/nslookup TXT yourdomain.com → ensure exactly one v=spf1 record
- Count DNS mechanisms to confirm <=10 lookups
- Confirm include:spf.protection.outlook.com is present
3.Check routing:
- Determine actual egress IPs from Exchange/connector logs and message traces
- Verify those IPs are covered via include or ip4/ip6
4.Test:
- Use a seed-list (Gmail, Yahoo, Outlook.com, corporate) and compare outcomes
- Review DMARC aggregate (rua) reports to see pass/fail by source IP
AutoSPF link: AutoSPF offers a one-click header parser, automatic lookup counting, “who sent this?” source mapping from DMARC reports, and guided remediation steps that you can apply directly to DNS.
10) SPF record length, flattening, and maintainability
While DNS TXT allows multiple 255-character strings concatenated, some DNS hosts and resolvers behave poorly with very long SPF records; overlong records are also hard to maintain.
- Flattening pros: Reduces DNS lookups by replacing includes with ip4/ip6; stabilizes under the 10-lookup ceiling.
- Flattening risks:
- IP churn at vendors can break authorization if not refreshed frequently.
- Loss of intent readability; harder manual audits.
- Potential to hit provider-specific DNS limits if you list many IPs.
- Recommended practices:
- Apply selective flattening only to heavy, nested includes.
- Use automated refresh with low TTL (e.g., 3600s-7200s) to track vendor changes.
- Split traffic by subdomain to keep each SPF concise.
- Monitor DMARC outcomes to catch emerging gaps early.
AutoSPF link: AutoSPF performs smart, scheduled flattening (with vendor-change subscription feeds), enforces TTLs, rehydrates readable comments for audit, and alerts you before you near resolver or provider-specific limits.
FAQs
Should I use “mx” or “a” in my Office 365 SPF?
- Generally avoid “mx” and “a” unless you explicitly send outbound mail from those hosts. For Office 365, include:spf.protection.outlook.com is the authoritative mechanism. Using “mx” when your MX points to third-party filtering can bloat lookups and authorize unintended IPs.
Is “ptr” safe to use in SPF?
- No. “ptr” is slow, unreliable, and discouraged by RFC 7208. Many receivers ignore or penalize it. Replace ptr with explicit ip4/ip6 or the vendor’s include.
Can “redirect=” help me manage complex SPF?
- redirect=domain can centralize policy, but it consumes a lookup and replaces the current record’s content entirely. It’s useful for subdomain hierarchies; for complex multi-vendor setups, includes plus smart flattening are usually better. AutoSPF evaluates redirect vs include trade-offs for your domain.
How long do SPF changes take to take effect?
- DNS TTL governs propagation, typically 5 minutes to 2 hours. Some receivers cache longer. AutoSPF tracks propagation and can re-test once caches expire.
If DKIM passes, do I still need correct SPF?
- Yes. While DMARC can pass via DKIM alignment alone, maintaining correct SPF adds resilience (especially for services without DKIM) and improves receiver trust signals. Office 365 best practice is to enable both SPF and DKIM, then enforce with DMARC.
Conclusion: Make Office 365 SPF resilient with AutoSPF
Incorrect SPF in Office 365 leads to bounces, spam placement, DMARC failures, and hybrid/forwarding edge cases that quietly erode deliverability; the fix is a single, syntactically correct SPF that authorizes every real sending path, stays under the 10-lookup ceiling, and is aligned with DKIM and DMARC.
AutoSPF operationalizes this end-to-end: it validates and consolidates records, ensures include:spf.protection.outlook.com is present, manages lookup budgets, performs safe flattening, stages “all” qualifier changes, coordinates DKIM/DMARC alignment, and continuously monitors outcomes via DMARC telemetry. The result is Office 365 mail that lands where it should, consistently, while your team adds or retires senders with confidence and without surprises.

General Manager
Founder and General Manager of DuoCircle. Product strategy and commercial lead for AutoSPF's 2,000+ customer base.
LinkedIn Profile →