How RFC 7208 Powers SPF: A Simple Guide for Domain Owners
Quick Answer
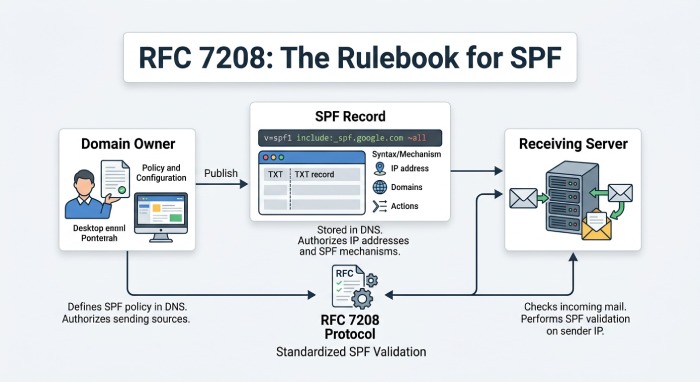
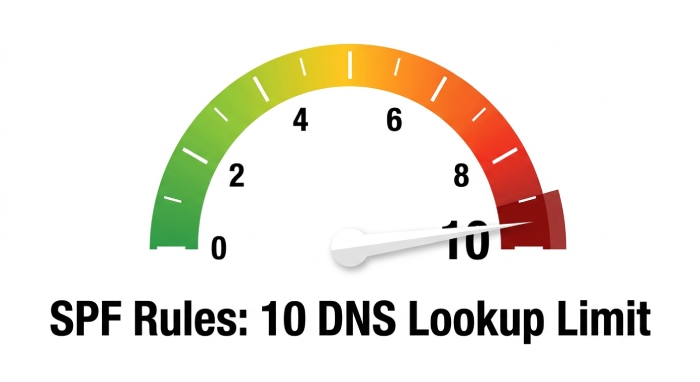
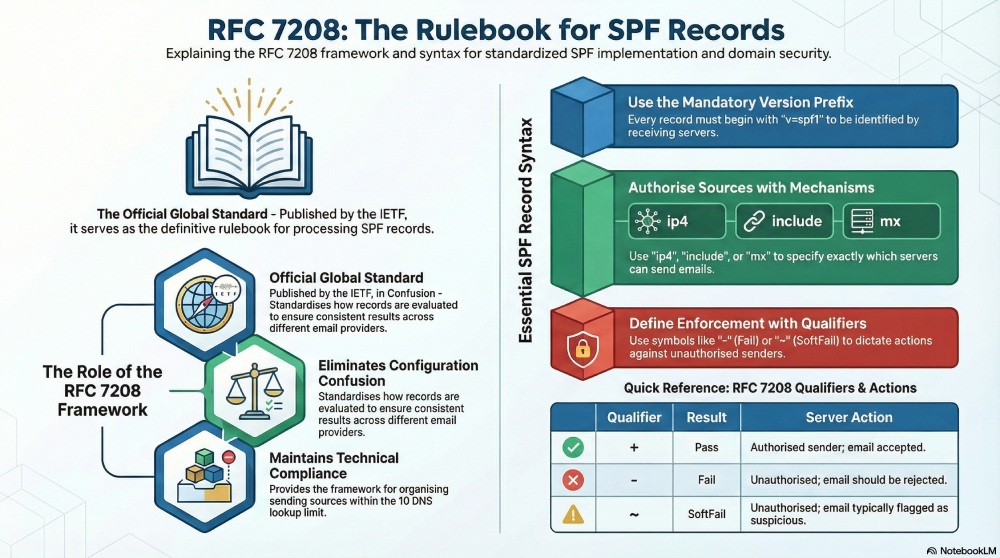
RFC 7208 is the official Internet Engineering Task Force (IETF) standard that defines how Sender Policy Framework (SPF) works. Published to replace the earlier experimental RFC 4408, it standardizes SPF record syntax, mechanism evaluation order, DNS lookup limits (maximum 10), qualifier semantics, and error handling — giving both domain owners and receiving mail servers a single authoritative rulebook for email authentication.
How RFC 7208 Powers SPF: A Simple Guide for Domain Owners
Related: How to Create an SPF Record ·SPF Record Format

RFC 7208 is the official Internet Engineering Task Force (IETF) standard that defines how Sender Policy Framework (SPF) works. Published to replace the earlier experimental RFC 4408, it standardizes SPF record syntax, mechanism evaluation order, DNS lookup limits (maximum 10), qualifier semantics, and error handling — giving both domain owners and receiving mail servers a single authoritative rulebook for email authentication.
According to the Anti-Phishing Working Group (APWG), more than 1 million phishing attacks were recorded in a single quarter of 2025, underscoring why standards like RFC 7208 matter for every domain owner sending email today.
“SPF alone won’t stop spoofing, but a correctly implemented SPF record — built to RFC 7208 specifications — is the foundation that DKIM and DMARC build on,” says Brad Slavin, CEO of AutoSPF. “Most authentication failures we see trace back to records that violate the standard’s lookup limits or mechanism ordering rules.”
As a domain owner, you’ve likely already implemented SPF for your email-sending domain. This authentication protocol allows you to specify which domains and addresses are authorized to send emails on your behalf. When a receiving server gets an email, it checks the SPF record to verify whether the sending source is authorized. If the sender is listed, the email passes authentication — if not, it may fail or be flagged as suspicious.
That’s the surface-level understanding. Behind the scenes, RFC 7208 tells receiving servers exactly how to read your SPF record, how to process each mechanism, when to stop evaluation, and what result to return if something goes wrong.
What is RFC 7208?
When SPF was officially introduced in 2006 via RFC 4408, it was more of a community-led initiative against email spoofing. While organizations were adopting it, there was still confusion around how to create records, how those records should be evaluated, and what should happen when an SPF check failed or returned an error.
RFC 7208 was introduced to address this confusion. Published by the Internet Engineering Task Force in April 2014, it became the official standard defining how SPF should work. This framework standardized SPF implementation for both domain owners and receiving servers.
As a domain owner, you can refer to RFC 7208 to understand how to build your SPF record correctly, which mechanisms you can use, how many DNS lookups are allowed, and how different SPF results are interpreted by receiving servers.
According to RFC 7208 Section 4.6.4, SPF evaluation must not result in more than 10 DNS-querying mechanisms — exceeding this limit produces a PermError, causing legitimate emails to fail authentication regardless of whether the sender is authorized.
Since your SPF implementation is primarily contingent on how you create your SPF record, following RFC 7208 ensures that your record is structured properly right from the beginning and you don’t make common mistakes that can cause SPF to fail. For instance, if you have too many sending sources configured in your SPF record, RFC 7208 helps you understand how to organize them properly without exceeding the 10 DNS lookup limit. Similarly, if you use multiple third-party email providers, it helps you understand when to use mechanisms like include, ip4, ip6, a, or mx. Moreover, it helps you understand the structure of your record and why the order of mechanisms matters.
All of this helps you create an SPF record that is easier for receiving servers to process and less likely to return errors.
How does RFC 7208 define SPF record syntax?
The SPF record published in your DNS is not a random string of text. Each mechanism, qualifier, and modifier in the record has a purpose and must be aligned in a specific order so that the receiving server can process it correctly. RFC 7208 defines exactly how an SPF record should be structured.
Start your SPF record with v=spf1
According to RFC 7208, every record must begin with v=spf1. This tells the receiving server that the TXT record is an SPF version 1 record, and the rest of the record should be read as an SPF policy. If you don’t start your record with v=spf1, the receiving server will not be able to identify the record as an SPF record, let alone its mechanisms.
Use mechanisms to authorize sending sources
Once you add v=spf1 to specify your TXT record as an SPF record, the next step is to define which sending sources are authorized to send emails on your behalf.
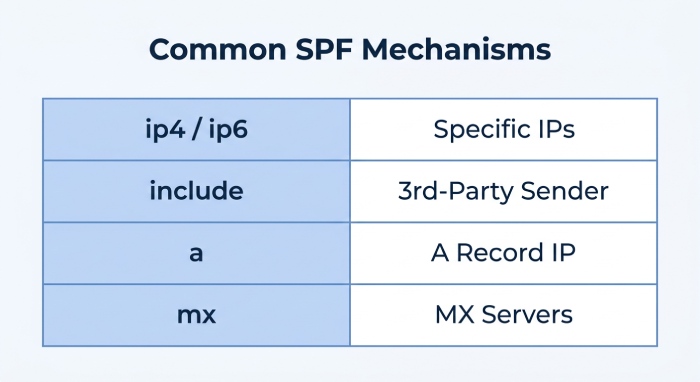
There are several mechanisms defined by RFC 7208 that allow you to authorize different types of sending sources depending on your email setup. Some of the most common ones include:
- ip4 to authorize a specific IPv4 address or IP range
- ip6 to authorize a specific IPv6 address or IP range
- include to authorize a third-party sender
- a to authorize the IP address in your domain’s A record
- mx to authorize the servers listed in your MX record
For instance, in the following SPF record:
v=spf1 ip4:192.0.2.10 include:_spf.yourcompany.com -allHere:
- ip4:192.0.2.10 authorizes that specific IPv4 address to send emails on behalf of your domain
- include:_spf.yourcompany.com authorizes your company’s sending servers
RFC 7208 defines the syntax of SPF records, while AutoSPF simplifies creating and managing them automatically — flattening nested includes, resolving IP addresses, and keeping your record within the 10-lookup limit without manual DNS edits.
Use qualifiers to define SPF results
SPF implementation isn’t just about listing the authorized sending sources in your record — it’s also about taking action against those that aren’t authorized by you and yet try to send emails on behalf of your domain.
This is where SPF qualifiers come in. RFC 7208 defines qualifiers that tell the receiving server what result should be returned when a sender matches or does not match your SPF policy.
The most common qualifiers are:
-
- for Pass
-
- for Fail
- ~ for SoftFail
- ? for Neutral
When you use these qualifiers with the all mechanism, they instruct the receiving server on how to handle unauthorized senders.
For instance:
- -all means that any sender not listed earlier in the record should fail SPF
- ~all tells the receiving servers to return a SoftFail result for the unauthorized sender
- ?all means the result should be Neutral
Out of these, -all is the strictest one, as it tells receiving servers that any sender not included in your SPF record is not authorized to send emails on behalf of your domain and should be rejected outright.
According to a 2025 Valimail report, fewer than 30% of domains worldwide have progressed beyond p=none in their DMARC policies — meaning most organizations still lack the strict SPF enforcement (-all) recommended by RFC 7208 for full protection against spoofing.
Still not sure how to configure SPF for your email-sending domain? Our team can help you with it. Reach out to us!
Topics
CEO
Founder and CEO of DuoCircle. Product strategy and commercial lead for AutoSPF's 2,000+ customer base.
LinkedIn Profile →Fix your SPF record in 60 seconds
Try AutoSPF free for 30 days. No credit card required.
Start Free Trial