What Is SPF Email? A Guide to Sender Validation Technology

Quick Answer
In our increasingly connected digital world, ensuring that your emails are genuine and trustworthy is more important than ever. Every day, countless people sift through their inboxes, wary of messages that might be hiding scams or phishing attempts. So how can you make sure your communications stand out as legitimate? This is where SPF email comes in.
Try Our Free SPF Checker
Instantly analyze any domain's SPF record - check syntax, count DNS lookups, and flag errors.
Check SPF Record →
In our increasingly connected digital world, ensuring that your emails are genuine and trustworthy is more important than ever. Every day, countless people sift through their inboxes, wary of messages that might be hiding scams or phishing attempts. So how can you make sure your communications stand out as legitimate? This is where SPF email comes in.
Sender Policy Framework (SPF) is a vital tool that helps domain owners specify which servers are allowed to send those important emails. By using SPF, you not only protect your brand from impersonation but also enhance the trust between you and your recipients. Let’s dive into what SPF email is all about, how it works, and why it’s an essential guardrail for your online interactions.
SPF, or Sender Policy Framework, is an email authentication protocol designed to prevent spam and phishing by verifying that an incoming email message comes from an authorized mail server. By publishing a specific SPF record in the domain’s DNS settings, domain owners can define which servers are permitted to send emails on their behalf, enhancing email security and protecting brand reputation.
What Is SPF Email?
SPF, or Sender Policy Framework, serves as a critical line of defense against email spoofing, one of the most common tactics used in phishing attacks. Spoofing involves someone pretending to be someone else to send fraudulent emails from a domain, tricking users into engaging with malicious content. The shield provided by SPF is essential for maintaining the integrity of email communication across both personal and organizational environments.
At its core, SPF allows domain owners to define which mail servers are permitted to send emails on their behalf. This information is stored in the Domain Name System (DNS) as a TXT record, detailing a list of authorized IP addresses or domain names. When an email is dispatched from a server, the receiving server refers back to this SPF record to verify whether the sending server is granted permission to send mails for that specific domain.
In simpler terms, think of SPF as your digital security guard, tasked with upholding the rules of who gets to communicate on behalf of your brand.
Consider this analogy: Imagine a nightclub where only certain guests are allowed entry based on an exclusive guest list held by a bouncer at the door. When someone attempts to enter, the bouncer checks their name against the list; if it’s not there, entry is denied. Your domain is like that nightclub, and SPF acts as the bouncer making sure that only legitimate traffic gets through.
As the prevalence of phishing attempts continues to climb - with nearly 90% of organizations implementing some form of SPF - its significance cannot be overstated. A well-configured SPF record can bolster your email’s deliverability while drastically reducing the risk of falling victim to phishing attacks. By specifying which mail servers are authorized to represent your domain, you protect yourself and strengthen the trust your recipients place in your communications.
However, it’s crucial to remember that implementing SPF correctly requires diligence and foresight. Users must be mindful of limitations such as the maximum of ten DNS lookups mentioned in the specifications. Exceeding this limit can hinder appropriate sender validation, adversely affecting email delivery.

Whether you manage a single domain or multiple ones, being proactive in establishing a solid SPF framework will help maintain your organization’s email presence while safeguarding against unauthorized access attempts. As we transition from understanding SPF’s purpose and function, it’s important to explore how it carries out its role in validating senders effectively.
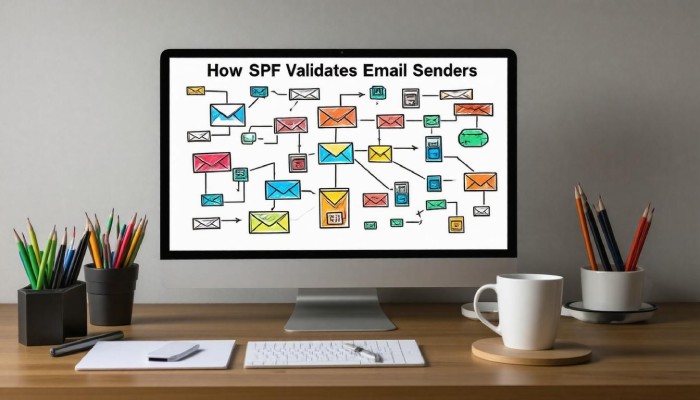
How SPF Validates Senders
Validation through SPF is a seamless yet crucial process that begins the moment an email is sent from an authorized server. Essentially, when an email transitions into the digital ether, the receiving email server must take immediate action to ensure its legitimacy. The first step in this journey involves querying the Domain Name System (DNS) to retrieve the SPF record associated with the sender’s domain. This is where the magic truly happens.
Upon receiving the message, the server examines the originating IP address - this is akin to checking an ID before granting entry to a secure area. It compares this address against a list contained within the SPF record. If there’s a match, akin to saying “Welcome, you’re on the guest list,” the email is deemed validated and allowed through. Conversely, if there’s no correspondence between the IP address and the authorized addresses in the record, it raises a red flag; thus, the email is marked as potentially suspicious, much like a visitor trying to enter without an invitation.
Through this method of validation, SPF not only helps prevent unauthorized emails from infiltrating inboxes but also plays a larger role in securing online communication.
SPF Record Syntax
To understand how this authentication works, let’s take a closer look at what an SPF record looks like. For example:
v=spf1 ip4:192.168.0.1 -all
This seemingly simple string holds a wealth of information that governs sending permissions for that domain.
Breaking it down:
-
The v=spf1 part indicates the version of SPF being used, ensuring compliance with current standards.
-
Following that is ip4:192.168.0.1, which specifies an allowed IPv4 address authorized to send emails on behalf of the domain - essentially giving a particular IP its stamp of approval.
-
Lastly, -all directs servers to treat all other IPs not explicitly mentioned as unauthorized. This is a crucial step because it prevents other servers from impersonating the domain.
Maintaining accurate and updated SPF records is paramount, especially for organizations that use multiple servers or change their mailing infrastructure frequently. Regular audits of these records can safeguard against misconfigurations and help uphold a positive domain reputation.
By understanding how these records function and their syntax, you set the stage for enhancing your email security and improving sender verification processes ahead. Next, we will explore how to properly create and manage these vital records effectively.
Steps to Configure SPF Records
The process of configuring SPF records might seem daunting at first, but it can be broken down into simple, manageable steps. It all begins with identifying the authorized mail servers you’d like to include in your SPF record. This means compiling a comprehensive list of IP addresses for every server that is authorized to send emails on behalf of your domain. Think about not only your own organization’s mail server but any third-party services you may use - this could involve marketing platforms, CRM systems, or customer support tools.

As you gather this information, take care to ensure you have the correct IP addresses and service details. It helps to consult with your IT team or check the documentation provided by those third-party services. Accurate information is crucial because including incorrect details can lead to unnecessary delivery failures or security breaches.
Step I, Identify Authorized Mail Servers
Once you’ve compiled this list of IPs and authorized services, you’re ready to create the actual SPF record. The SPF record itself is a line of text that follows a specific format. For example, if you only have one server, your record would look something like v=spf1 ip4:192.168.0.1 -all. If you have two servers, you can combine their IPs within the same SPF entry by separating them with spaces: v=spf1 ip4:192.168.0.1 ip4:192.168.0.2 -all.
Now that you’ve got a handle on creating the SPF record text, we need to add it to your DNS settings so that it’s properly recognized by email servers around the world.
Step II, Create the SPF Record
To proceed with adding your newly-created SPF record, you’ll need access to your domain registrar’s control panel. When you log in, navigate straight to the section for DNS settings - typically labeled as “DNS Management” or “Zone Editor.” Here, locate an option for adding a new TXT record.
When creating this TXT entry, paste in your SPF record carefully as you’ve written it - the format v=spf1 [authorized IPs] -all should remain intact without any alterations. After saving these changes, don’t be alarmed if they don’t take effect immediately; DNS updates can sometimes take up to 48 hours due to propagation delays across various servers.
Step III, Update DNS with SPF Record
Verifying the update once some time has passed is also critical in ensuring everything works smoothly. Utilizing online SPF validation tools can help you double-check that your configuration functions correctly; these tools simulate an email header check and reassure you that incoming mail servers will trust emails sent from your domain.
Properly configured SPF records serve as a frontline defense against spoofing attacks and enhance your email deliverability while safeguarding your brand’s reputation.

As you complete this setup, remember that configuring SPF is just a part of a larger strategy for securing your emails - integrating it with other technologies can significantly bolster protection against malicious threats.
Comparing SPF, DKIM, and DMARC
While SPF focuses on verifying the sender’s IP address, DKIM (DomainKeys Identified Mail) adds another layer by using cryptographic signatures to authenticate the message’s origin.
Essentially, while SPF can tell you who is allowed to send an email on behalf of your domain, DKIM ensures that the email content has not been tampered with during transit. Think of it as locking a letter in a secure envelope and then sending it; even if someone sees the address on the outside, they can’t change what’s inside without breaking the seal.
Therefore, both SPF and DKIM serve distinct purposes but integrating them elevates security substantially.
DMARC: Combining SPF and DKIM
Enter DMARC (Domain-based Message Authentication, Reporting & Conformance), which ties the results from both SPF and DKIM to determine an email’s authenticity comprehensively.
This means that DMARC acts as a policy framework for domain owners to instruct receiving servers on how to handle emails that fail either SPF or DKIM checks. For instance, when a message doesn’t pass authentication, DMARC allows you to specify whether those emails should be rejected outright or sent to quarantine, providing greater control over your domain’s security.
To better understand their unique values - and limitations - let’s break down some key pros and cons.
Pros and Cons
Below is a detailed look at the strengths and weaknesses of each protocol in table format:
| Protocol | Strengths | Weaknesses |
|---|---|---|
| SPF | Simple to implement; effective against spoofing | Doesn’t handle forwarded emails well |
| DKIM | Adds cryptographic assurance; verifies message integrity | More complex setup than SPF |
| DMARC | Comprehensive reporting and guidance on handling failures | Requires both SPF and DKIM setups to be effective |
It’s essential to note that while implementing SPF is quite straightforward, it can only check for authorized senders. This means if an email is forwarded - common in many communication chains - those checks may fail since the forwarding server isn’t listed in the sender’s SPF record. Conversely, while DKIM enhances security through encryption, its complexity can be daunting; however, it becomes immensely valuable when paired with DMARC for governance over failed authentications.
Understanding these protocols equips you with the tools needed to effectively manage email security. To further explore how leveraging these frameworks can enhance email communications, we will now look at the benefits associated with their implementation.
Advantages of Implementing SPF
First and foremost, adding SPF records improves your domain’s brand reputation. When your emails are authenticated through SPF, Internet Service Providers (ISPs) can clearly see that you have taken the necessary precautions to ensure these messages are genuine. This not only builds trust with ISPs but also enhances the confidence of your recipients. Consequently, as spam filters recognize your emails as legitimate, they are less likely to end up in the dreaded spam folder.
In fact, research shows that domains using SPF see a notable increase in email deliverability; reports indicate improvements can range from 10-20%.
The benefits of ramping up security through SPF don’t end with brand reputation alone. An SPF record acts as an effective deterrent against unauthorized senders trying to impersonate your domain. This added layer of security limits the risk of your brand being associated with spam or phishing campaigns - something that could severely damage customer trust. Research has shown that organizations deploying SPF experienced up to 80% fewer instances of email spoofing, showcasing the effectiveness of this easy-to-implement technology in creating a safer email environment.
Furthermore, it’s crucial to recognize how these advantages translate into tangible savings for businesses.
By preventing phishing attacks and email fraud, companies can save significant amounts - averaging around $1.5 million annually due to reduced operational costs linked to these issues. The combination of improved security and higher deliverability means not only are you protecting your brand, but you’re also enhancing your bottom line.
Moreover, statistics reveal that customers express greater trust in communications from domains using SPF; about 65% of users feel more confident engaging with emails that come from verified sources. This trust translates directly into increased engagement rates and potentially higher conversion rates for businesses committed to email best practices.
Adopting SPF not only fortifies your defenses against malicious attacks but also fosters valuable relationships with customers and partners alike.
Integrating SPF into your email strategy aligns with compliance standards increasingly being mandated by regulatory bodies. As organizations strive for a comprehensive approach to protect both data and customer information, implementing SPF alongside frameworks like DKIM and DMARC serves as a powerful testament to your commitment to security in digital communication.
With these advantages laid out, it’s essential to examine some common hurdles organizations face when implementing this vital email authentication technology.
Common SPF Challenges
Implementing SPF is not without its pitfalls. One significant hurdle arises when dealing with email forwarding scenarios. When an email is forwarded, the original sender’s IP address - the very element that SPF relies on for verification - may no longer match the authorized servers listed in the SPF record. This mismatch can confuse receiving servers, leading to legitimate emails being marked as spam or, worse, completely rejected.
Picture it as a well-written invitation that gets tossed aside because it lacks a recognizable return address; that’s how SPF treats forwarded emails.
Another challenge is the frequent misconfiguration of SPF records by organizations. Often, they may inadvertently exceed the established limit of 10 DNS lookups set forth in the RFC (Request for Comments). This means that when an incoming email is verified, it may generate unnecessary queries which complicate validation and could result in abandonment of the SPF check altogether.
Visualize trying to navigate through a complex maze only to find dead ends along the way - that’s what happens when your SPF setup is overloaded with excessive lookups.
To mitigate these pitfalls, it’s essential to streamline your SPF record effectively. This means including only the most necessary IP addresses and utilizing mechanisms like include, a, and mx strategically within your SPF record.
For instance, using the include mechanism allows you to reference another domain’s SPF record instead of listing all possible sending IPs directly in your own. This consolidation simplifies management and helps keep you within that critical 10-lookup limit.
Remember that less can be more when it comes to SPF records - focusing on essential entries can help maintain effective validation while promoting better email deliverability.
While these challenges may seem daunting, understanding them opens the door to implementing more robust solutions that ensure effective email authentication remains a priority moving forward.
Tools for Managing SPF Records
When it comes to managing your Sender Policy Framework (SPF) records effectively, you’ll find a variety of tools designed to ease the process - breaking down complexities into user-friendly experiences. These tools simplify the task of creating SPF records and ensure those records are accurate and compliant with email authentication standards, which is essential in today’s digital landscape where email spoofing and phishing are rampant.
SPF Record Generators
One of the primary steps in setting up your SPF record is its creation, and this is where SPF record generators come into play. Tools like MXToolbox and Dmarcian offer intuitive interfaces that allow you to input specific parameters relevant to your domain. By following simple guides, anyone, regardless of technical skill level, can generate SPF records that correctly reflect their email sending practices.
Imagine being able to type in details about your mail servers and receive a perfectly formatted SPF record in seconds. What might seem daunting becomes a breeze!
Furthermore, these generators often provide added features such as built-in suggestions for IP addresses or mechanisms to include, ensuring that you don’t miss any crucial components while crafting your SPF record.
SPF Validators
After generating an SPF record, it’s equally important to validate it; that’s where SPF validators come in.
Validators like Kitterman’s SPF Syntax Validator or DMARC Analyzer empower you to check your newly created records for potential issues. Think of them as your safety net - before deploying an SPF record live, these tools help identify syntax errors or misconfigurations that could otherwise lead to delivery problems.

Data Center Illustration concept. Flat illustration isolated on white background
For instance, if you’ve mistakenly included more DNS lookups than the allowed limit (which is 10), a validator will promptly alert you. This preventive measure means you won’t have to experience frustrating email delivery failures or discover that emails are landing in spam folders unexpectedly.
| Tool Name | Features |
|---|---|
| MXToolbox | Comprehensive SPF lookup services along with report generation. |
| DMARC Analyzer | Robust validation and troubleshooting for SPF, DKIM, and DMARC setups. |
| Kitterman’s SPF Validator | Quick syntax checks for compliance with established standards. |
These tools are critical for maintaining ongoing compliance with email authentication standards. Once you’ve implemented your SPF records, regular validation ensures everything remains functional as changes occur over time - such as updates to IP addresses or modifications in email service providers.
With these tools at hand, managing SPF records becomes less of a chore and more of a straightforward process - one that every domain owner should embrace to ensure secure and reliable email communication.
In conclusion, understanding and utilizing SPF management tools can significantly enhance your email’s security posture and improve deliverability while mitigating risks associated with phishing attacks. By properly creating and validating your SPF records, you contribute to a safer digital environment for all users.
How does SPF protocol contribute to email security?
The SPF (Sender Policy Framework) protocol enhances email security by allowing domain owners to specify which mail servers are authorized to send emails on their behalf. This helps prevent spam, phishing attacks, and email spoofing, as receiving mail servers can verify the sender’s IP address against the listed authorized servers. According to a 2021 report, implementing SPF can reduce email spoofing incidents by up to 80%, significantly increasing trust in email communications for both businesses and individuals.
How do SPF records interact with other email authentication protocols like DKIM and DMARC?
SPF (Sender Policy Framework) records work in conjunction with DKIM (DomainKeys Identified Mail) and DMARC (Domain-based Message Authentication, Reporting & Conformance) to enhance email security. While SPF verifies the sender’s IP address against a list of authorized senders for a domain, DKIM adds a digital signature to authenticate the message’s content. DMARC ties both mechanisms together by allowing domain owners to specify how emails failing these checks are handled, hence improving deliverability and protecting against spoofing. Studies show that using all three protocols can reduce phishing attacks by up to 90%, demonstrating their effectiveness when implemented together for robust email authentication.
What are common mistakes people make when configuring their SPF records?
Common mistakes when configuring SPF records include failing to include all sending IP addresses, using multiple SPF records instead of a single consolidated one, and exceeding the DNS lookup limit of 10. These errors can lead to email deliverability issues, with studies indicating that improperly configured SPF records can contribute to more than 30% of email being marked as spam. Ensuring accurate and thorough SPF configuration is crucial for effective sender validation and maintaining a positive sender reputation.
What steps are needed to set up an SPF record for my domain?
To set up an SPF record for your domain, first identify the mail servers authorized to send emails on behalf of your domain. Next, create a TXT record in your domain’s DNS settings following the format “v=spf1 [authorized_servers] ~all”. For instance, if you’re using Google Workspace, it would look like “v=spf1 include:_spf.google.com ~all”. After saving changes, use SPF validation tools to ensure correctness. A proper SPF setup can improve email deliverability by up to 70% and minimizes phishing risks, making it essential for safeguarding your domain’s reputation.

Can implementing SPF completely eliminate email spoofing?
Implementing SPF (Sender Policy Framework) can significantly reduce the risk of email spoofing but cannot completely eliminate it. SPF allows email servers to verify that incoming messages come from authorized sources, thus blocking spoofed emails that fail this check. However, it has limitations, such as being ineffective against phishing attacks using legitimate addresses or when malicious actors forge the “From” address without proper domain alignment. A report by the Anti-Phishing Working Group noted that in 2023, around 75% of phishing attacks still bypassed standard SPF implementations, highlighting the need for additional measures like DKIM and DMARC for comprehensive protection.
SPF History and Current State
SPF was first mentioned in 2000 but was overlooked. Later, in 2002, an SPF-like concept was published by Dana Valerie Reese, who was not aware of its earlier mention. An American computer scientist, Paul Vixie, posted his SPF-like concept on the same list as Dana. These posts gained attention overnight and led to the formation of the IETF Anti-Spam Research Group (ASRG). In the next six months, many developments were made in the protocol. Initially, SPF stood for Sender Permitted From, which was changed to Sender Policy Framework in February 2004.
In 2005, IESG approved the then-best version of SPF and invited the community to observe SPF during the two years following publication. On April 28, 2006, the SPF RFC was published as experimental RFC 4408. In April 2014, IETF announced and published its proposed standard (RFC 7208), which is the current state.
Topics

General Manager
Founder and General Manager of DuoCircle. Product strategy and commercial lead for AutoSPF's 2,000+ customer base.
LinkedIn Profile →