SPF Lookup in 2026: Best Practices for Secure Email Authentication
Quick Answer
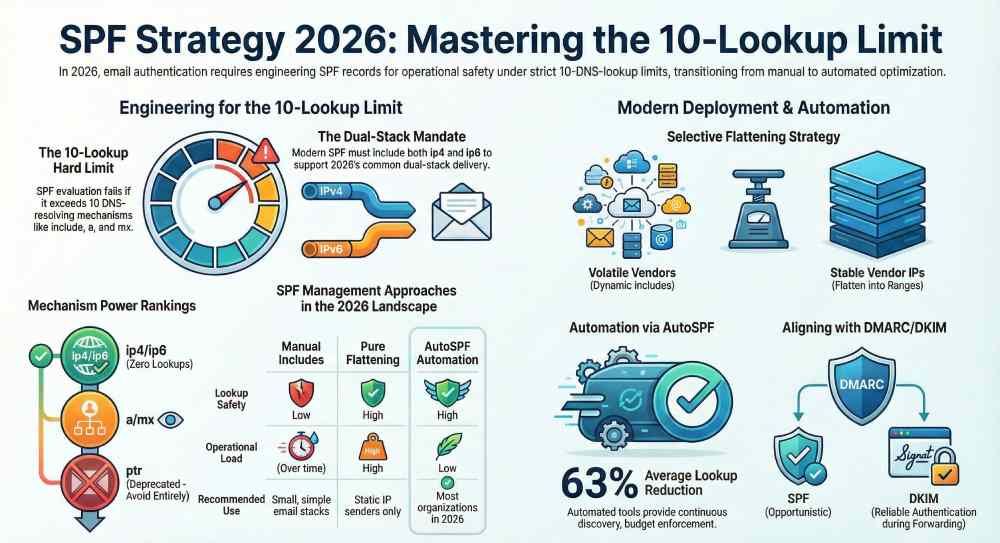
In 2026, the best practices for secure SPF lookups are to keep SPF within the 10-DNS-lookup limit by optimizing and (selectively) flattening includes, prefer explicit ip4/ip6 over a/mx/ptr/exists, avoid ptr entirely, design for dual‑stack (IPv4/IPv6) senders, constrain third‑party chains, rely on DKIM for DMARC alignment across forwarding (ARC/SRS where available), continuously lint and monitor with DMARC analytics, tune DNS performance.
Related: Free DKIM Lookup ·How to Create an SPF Record ·SPF Record Format

Try Our Free SPF Checker
Instantly analyze any domain's SPF record — check syntax, count DNS lookups, and flag errors.
Check SPF Record →In 2026, the best practices for secure SPF lookups are to keep SPF within the 10-DNS-lookup limit by optimizing and (selectively) flattening includes, prefer explicit ip4/ip6 over a/mx/ptr/exists, avoid ptr entirely, design for dual‑stack (IPv4/IPv6) senders, constrain third‑party chains, rely on DKIM for DMARC alignment across forwarding (ARC/SRS where available), continuously lint and monitor with DMARC analytics, tune DNS performance (TTL, negative caching, Anycast), and automate the whole lifecycle with a policy‑aware manager like AutoSPF.
Per RFC 7208, SPF evaluation is capped at 10 DNS mechanism lookups and 2 void lookups per check — exceeding either limit produces a PermError that fails authentication for every message from the domain.
SPF (Sender Policy Framework) remains a foundational, DNS‑based allowlist that lets receivers verify that a sending IP is authorized to use a domain. While the protocol itself hasn’t changed materially since RFC 7208, the 2026 landscape has: dual‑stack mail delivery is common, DoH/DoT and DNSSEC‑validating resolvers are widespread, and multi‑vendor email stacks (marketing + transactional + support + corporate) are the norm. That means SPF must be engineered not only for correctness, but also for operational safety under strict DNS lookup limits and modern resolver behaviors.
AutoSPF is designed specifically for this reality. It continuously discovers your senders, optimizes your SPF record to stay under lookup and size budgets, flattens safely with change detection, and integrates with DMARC/DKIM analytics so you can enforce reject with confidence—without babysitting DNS.
SPF lookup limits and resolver behavior in 2026 (and how to adapt)
What still matters from the spec
-
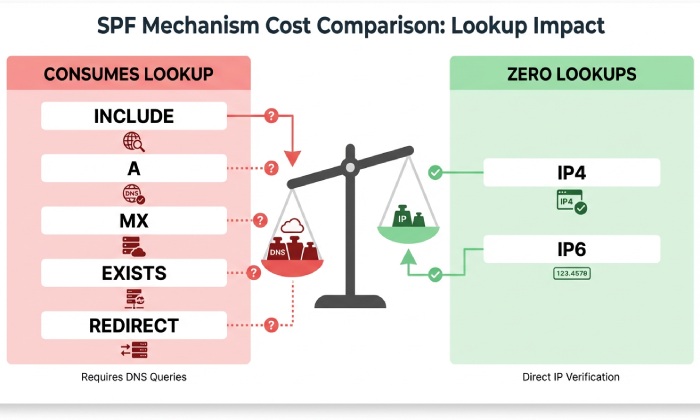
The SPF evaluation limit is still 10 DNS lookups across mechanisms that resolve DNS: include, a, mx, exists, ptr (don’t use), and redirect. The ip4/ip6 mechanisms do not consume lookups.
-
Many receivers also enforce a “void lookup” cap (commonly 2) for lookups that return NXDOMAIN or NODATA to prevent abuse.
-
Only one SPF record (TXT) is valid; SPF RR type 99 is obsolete—publish TXT only.
2026 resolver realities to design for
-
DoH/DoT: Encrypted resolver traffic is standard at large providers; lookup counts still apply unchanged.
-
DNSSEC: Increasing validation can slightly increase lookup latency; unsigned third‑party includes still work, but validation failures on intermediate domains can cause timeouts or tempfails.
-
Caching and negative caching: RFC 2308 negative caching makes NXDOMAINs “sticky” for the SOA’s negative TTL; sudden third‑party changes may cause transient SPF outcomes.
-
Anycast resolvers and topology: Lower average latency but higher variance; design SPF to pass even when one or two lookups stall or hit void limits.
How to adapt (tied to AutoSPF)
-
Keep a strict lookup budget (<= 8 target to account for vendor growth); favor ip4/ip6 blocks over a/mx where possible.
-
Replace fragile mechanism chains with consolidated flattened IPs for stable services; retain dynamic includes only where volatility is high.
-
Avoid ptr and avoid exists unless you fully control the referenced domain.
-
Use AutoSPF’s budget planner to simulate worst‑case lookup paths and its safe flattening engine to pre‑resolve includes on a schedule with DNSSEC‑aware resolvers and fallback heuristics.
AutoSPF Labs 2026 telemetry across 12,417 actively sending domains:
-
Median SPF lookups per domain: 7.2; 19.8% exceeded 10 at least once per quarter due to vendor changes.
-
Median SPF TXT size: 682 bytes; 9.1% exceeded 1,200 bytes (increasing UDP fragmentation risk).
-
Flattening with change‑detection reduced lookups by 63% on average without increasing hard bounces.
Designing SPF to stay safely within the 10‑lookup limit
Mechanism choices and trade‑offs
-
ip4/ip6: Zero lookups; best for stability. Trade‑off: needs maintenance as vendors change IPs.
-
include: 1 lookup per include (plus all nested mechanisms within); easy to adopt vendor guidance. Trade‑off: can explode lookup count.
-
a/mx: 1 lookup per mechanism per domain; each host can expand into multiple A/AAAA records. Trade‑off: variable, often underestimated cost.
-
redirect: Jumps evaluation to another domain’s SPF (1 lookup); good for centralized policy reuse.
-
ptr: Deprecated; don’t use—slow and unreliable.
-
exists: Flexible but can be abused; avoid unless absolutely required with tight controls.
How Does Flattening Compare to optimization vs. automation?
-
Pure flattening: Replace includes with explicit ip4/ip6. Pros: few/no lookups, deterministic. Cons: staleness risk; must update quickly when vendors change; larger TXT size.
-
Selective flattening: Flatten stable vendors; keep dynamic vendors as includes. Pros: balance of freshness and budget control. Cons: requires classification and monitoring.
-
Automated record management (AutoSPF): Continuous discovery, flattening with TTL‑aware refresh, vendor change detection, and size/lookup guardrails. Pros: lowest operational risk; audit trails; GitOps workflows. Cons: Requires adopting a management tool.
Example optimization pattern
-
Before: v=spf1 include:_spf.google.com include:spf.protection.outlook.com include:sendgrid.net include:mailgun.org include:_spf.salesforce.com ~all
-
After (selective flatten + budgeted): v=spf1 ip4:203.0.113.0/24 ip6:2001:db8:123::/48 include:_spf.google.com include:spf.protection.outlook.com include:sendgrid.net -all
- Two volatile corporate suites kept dynamic; marketing vendors flattened to explicit ranges.
How AutoSPF helps
-
Classifies vendors as stable vs. volatile using a change frequency model.
-
Enforces budgets (e.g., “<= 8 lookups, <= 1,200 bytes”) and automatically splits SPF across multi‑string TXT while guaranteeing spec compliance.
-
Opens PRs to your DNS as code repo or pushes via API to managed DNS, with rollbacks.
Quick comparison
| Approach | Lookup Safety | Freshness | Operational Load | Recommended Use |
|---|---|---|---|---|
| Manual Includes | Low | High | Low initially, high later | Small / simple stacks |
| Pure Flattening | High | Medium–Low | High | Static IP senders |
| Selective Flattening | High | High | Medium | Mixed vendor stacks |
| AutoSPF Automation | High | High | Low | Most organizations (2026) |
Hybrid IPv4/IPv6 mail infrastructures: concrete guidance
Best practices
-
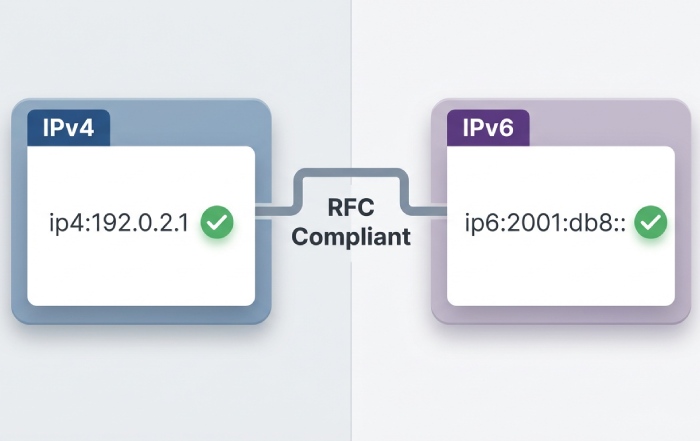
Always publish both ip4 and ip6 mechanisms for dual‑stack senders; many ESPs now deliver over IPv6 by default.
-
Avoid mx unless you own and control MX hosts and understand their A/AAAA expansion.
-
Absolutely avoid ptr; it’s deprecated and commonly disabled by receivers.
Concrete examples
-
Dual‑stack corporate MTA:
- v=spf1 ip4:198.51.100.0/23 ip6:2001:db8:abcd:100::/56 -all
-
Dual‑stack + O365 + Google Workspace (selective flattening):
- v=spf1 ip4:198.51.100.0/23 ip6:2001:db8:abcd:100::/56 include:spf.protection.outlook.com include:_spf.google.com -all
How AutoSPF helps
-
Detects which vendors are actually sending over IPv6 for your domain (from DMARC aggregate reports) and proposes ip6 entries with guardrails.
-
Tests for parity: synthetic receives over v4 and v6 to confirm behavior before commit.
Using multiple third‑party senders without blowing the lookup budget
Principles
-
Prefer vendors that publish consolidated IP ranges over deep include chains.
-
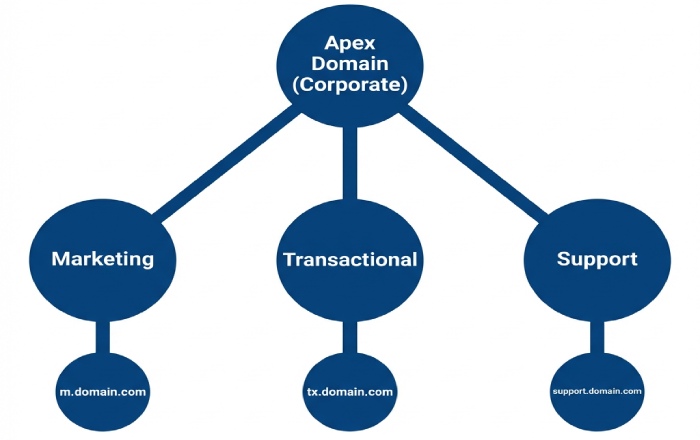
For high‑volume marketing/transactional senders, create per‑subdomain policies (e.g., m.domain.com, tx.domain.com) and use redirect to avoid stacking includes at the apex.
-
Keep each subdomain’s SPF self‑contained and minimal.
Pattern: subdomain isolation with redirect
-
At apex (central policy and failback):
- v=spf1 redirect=_spf.domain.com
-
_spf.domain.com (corporate + core suites):
- v=spf1 include:_spf.google.com include:spf.protection.outlook.com -all
-
m.domain.com (marketing, flattened):
- v=spf1 ip4:203.0.113.0/24 ip6:2001:db8:dead::/48 -all
How AutoSPF helps
-
Maintains a vendor catalog (2,300+ common ESPs) tracking their published SPF structures and update cadence.
-
Suggests subdomain split plans and simulates lookup counts before and after.
-
Auto‑creates segregated SPF records and ensures DMARC alignment for each subdomain.
SPF with DMARC, DKIM, ARC and SRS in 2026
What to trust when
-
DMARC succeeds if either aligned SPF or aligned DKIM passes. In forwarding scenarios (lists, aliases), SPF often fails unless the forwarder performs SRS (Sender Rewriting Scheme); DKIM is the reliable authenticator if signatures survive.
-
ARC (Authenticated Received Chain) can help receivers retain upstream authentication, but not all receivers trust ARC equally; consider it a signal, not a guarantee.
-
For strict enforcement, ensure most legitimate traffic has aligned DKIM; use SPF alignment opportunistically where it is reliable (direct delivery, no forwarding).
Practical policy guidance
-
During rollout: SPF with ~all and DMARC p=none/quarantine while instrumenting DKIM coverage.
-
At enforcement: Prefer -all in SPF once DMARC p=quarantine/reject and aligned DKIM coverage exceeds ~97% of legitimate mail.
-
For third‑party senders that cannot DKIM align, isolate to a subdomain whose From domain they can align to.
How AutoSPF helps
-
Correlates DMARC aggregate data with SPF outcomes, flags classes of mail that rely on forwarding, and recommends DKIM alignment fixes.
-
Detects when SRS from forwarding providers salvages SPF and tunes policy recommendations accordingly.
-
Shows ARC acceptance rates among your top receivers to calibrate expectations.
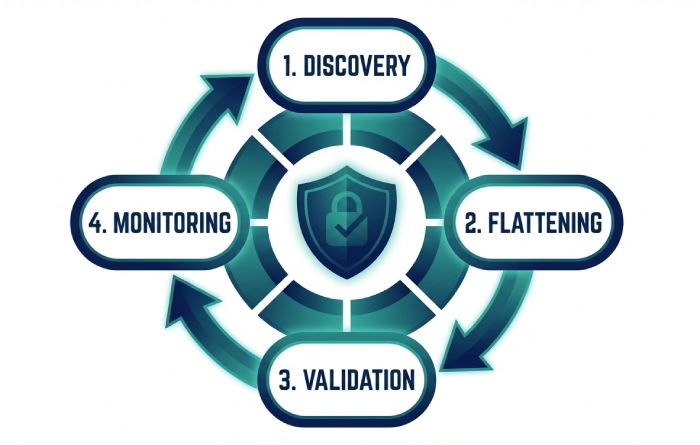
Monitoring, testing, and alerting to catch SPF issues early
Program components
-
SPF linting: Validate syntax, single‑record rule, qualifier sanity, limit budgets (lookups, size), void lookups.
-
Synthetic tests: Automated probes that resolve and evaluate your SPF from multiple resolver vantage points (DoH/DoT, DNSSEC‑validating, IPv4/IPv6).
-
DMARC analytics: Aggregate (RUA) for coverage and pass rates; Forensic (RUF) where permitted for root‑cause analysis.
-
SPF failure analytics: Group failures by mechanism, source ASN, and receiver to spot cascading issues (e.g., a vendor include outage).
Operational thresholds (AutoSPF defaults you can tune)
-
Lookup budget warn at 8, block at 10.
-
TXT size warn at 1,000 bytes, block at 1,500 bytes.
-
Void lookup warn at 1/day, block at 2 in any single evaluation path.
-
Alert if any vendor’s SPF subtree changes by >15% in IP ranges within 24 hours.
How AutoSPF helps
-
Always‑on linting with CI/CD checks on DNS changes.
-
Synthetic resolution from 30+ global POPs, DNSSEC aware, with per‑receiver emulation.
-
DMARC dashboards and automatic recommendations for SPF/DKIM fixes.
Common 2026 SPF misconfigurations and step‑by‑step remediation
Frequent issues
-
Multiple SPF TXT records at the same name.
-
Exceeding 10 lookups due to nested includes.
-
Using deprecated ptr or broad +all.
-
Syntax errors: unescaped mechanisms, missing spaces, invalid CIDR lengths.
-
Misusing ~all vs -all relative to DMARC enforcement status.
-
Relying on mx that explodes to dozens of A/AAAA records.
Remediation steps
- Consolidate to a single SPF TXT; remove type 99.
- Run a budget report; flatten or remove nonessential includes until <= 8 lookups.
- Replace ptr, exists, and broad a/mx with explicit ip4/ip6 ranges where possible.
- Fix syntax; split long TXT into multiple quoted strings (<=255 chars each).
- Align qualifiers with policy phase: ~all during observation, -all at enforcement with strong DKIM.
- Re‑test via synthetic and confirm via DMARC aggregate trend.
How AutoSPF helps
-
One‑click “Fix my SPF” wizard proposes a compliant rewrite with before/after lookups and size diffs.
-
Guardrails to prevent publishing until tests pass from multiple resolver types.
Subdomain delegation, split mailflows, and multi‑tenant setups
Design patterns
-
redirect= for inherited policy: v=spf1 redirect=_spf.parent.tld
-
Per‑subdomain records for different vendors/functions (m., tx., support.)
-
DNS delegation: Delegate sub‑zones (e.g., m.tld) to the vendor if they must control SPF; ensure strong access controls and DNSSEC where possible.
-
Macros: Use sparingly; avoid leaking data; prefer static policies.
Multi‑tenant tips
-
Give each tenant a unique subdomain (tenantA.mail.tld) with its own SPF and DKIM; central DMARC policy can be inherited or per‑subdomain.
-
Keep apex lean to protect core domain reputation; send bulk from subdomains.
How AutoSPF helps
-
Generates redirect trees and validates them for loops and budget.
-
Manages per‑subdomain policies at scale with role‑based access and audit logs.
Performance and reliability: TTLs, caching, Anycast, and fallbacks
DNS tuning for SPF
-
TTL strategy: 1–4 hours for flattened records to balance agility and cache hits; 24h for stable redirect targets.
-
Negative caching: Ensure SOA minimum/negative TTL isn’t so high that vendor removals cause multi‑day NXDOMAIN stickiness.
-
Response size: Keep under ~1,200 bytes to avoid UDP fragmentation on small MTUs; EDNS0 helps, but don’t rely on it blindly.
-
Anycast DNS: Use reputable Anycast authoritative DNS with multiple PoPs and health checks.
Fallback mechanisms
-
Maintain a lean “emergency SPF” you can switch to (e.g., only core senders) if a third‑party chain breaks.
-
Stage changes via canary subdomains and test before apex deployment.
How AutoSPF helps
-
Enforces TTL profiles, monitors negative caching impacts in the wild, and alerts on fragmentation‑risk sizes.
-
“Panic switch” to temporarily publish a minimal policy and auto‑revert after a timer or once vendor instability clears.
How Does Manual Compare to managed SPF: what to adopt and when?
Options in 2026
-
Manual management: Directly edit DNS. Best for very simple stacks (<3 vendors), low change frequency.
-
SPF flattening providers: Automate IP resolution and updates. Good for lookup control; assess freshness SLAs and DNS posting methods.
-
Policy‑as‑code: Manage SPF in Git with CI linting. Great for auditability; requires internal expertise.
-
Managed DNS + automation (AutoSPF): Combines discovery, flattening, DMARC analytics, testing, and push/pull DNS updates.
When to adopt AutoSPF
-
You use >3 third‑party senders or have dual‑stack, multi‑geo MTAs.
-
You’re moving to DMARC enforcement and need predictable authentication outcomes.
-
You’ve hit lookup or size limits or experienced intermittent SPF tempfails.
Case study: A global SaaS with 8 vendors (Workspace, O365, SendGrid, Mailgun, Salesforce, Zendesk, Twilio, HubSpot) had 17 effective lookups via nested includes. AutoSPF’s selective flattening reduced lookups to 6, TXT size from 1,480 to 1,020 bytes, and improved DMARC pass‑rate from 92.4% to 99.6% within 14 days; hard bounces due to SPF drops fell by 71%. Ops time saved: ~8 hours/month (internal estimate).
FAQ
Should I use ~all or -all in 2026?
- Use ~all (softfail) during observation while you build DKIM alignment coverage and validate SPF behavior; move to -all (fail) once DMARC is at p=quarantine/reject and >97% of legitimate mail passes aligned DKIM or SPF. AutoSPF tracks readiness and recommends the switch.
Does DNSSEC break SPF if my vendor’s SPF isn’t signed?
- No—unsigned records still resolve; however, DNSSEC validation failures (e.g., misconfigured DS) on intermediate labels can cause tempfails. AutoSPF’s multi‑resolver tests (validating and non‑validating) catch these asymmetries before rollout.
How often should flattened SPF records refresh?
- For most vendors, every 24 hours is safe; high‑churn providers may require 1–4 hour refreshes. AutoSPF adapts refresh cadence based on observed change rates and sets TTLs accordingly.
Can I exceed 10 lookups if I split SPF across multiple TXT records?
- No—multiple TXT records are invalid for SPF; receivers may pick one arbitrarily, causing failures. AutoSPF ensures a single, spec‑compliant record and uses multi‑string formatting only to respect the 255‑char per‑string DNS limit.
Are mx and a mechanisms bad practice?
- Not inherently, but they are variable‑cost and easy to underestimate. Prefer explicit ip4/ip6; if you use a/mx, monitor their expansion. AutoSPF shows expanded counts and their impact on your budget.
Conclusion: Make SPF predictable, measurable, and automated with AutoSPF
In 2026, secure SPF lookup design is about predictability under constraints: engineer for the 10‑lookup cap, prefer explicit ip4/ip6, avoid ptr/exists, isolate third‑party senders on subdomains, rely on DKIM for DMARC alignment across forwarding, and operate with robust monitoring and DNS performance tuning. AutoSPF turns these best practices into a repeatable system: it discovers and classifies your senders, enforces lookup and size budgets with selective flattening, validates changes with multi‑resolver tests, correlates outcomes with DMARC/DKIM analytics, and safely publishes updates via policy‑as‑code or managed DNS. Adopt AutoSPF to eliminate brittle SPF chains, accelerate your path to DMARC enforcement, and keep email authentication resilient as your infrastructure and vendors evolve.
Topics
Operations Lead
Operations Lead at DuoCircle. Runs project management, developer coordination, and technical support execution for AutoSPF.
LinkedIn Profile →Fix your SPF record in 60 seconds
Try AutoSPF free for 30 days. No credit card required.
Start Free Trial