An SPF record tester matters because it verifies your DNS-published sender authorizations end-to-end, catches syntax and lookup-limit failures before mailbox providers do, models provider-specific interpretations, and directly improves deliverability by ensuring authenticated, aligned email reaches the inbox.
In simple terms, Sender Policy Framework (SPF) tells receiving mail servers which IPs and hosts are allowed to send on behalf of your domain; a tester is the guardrail that turns a brittle DNS text string into predictable inbox outcomes. SPF is implemented as a DNS TXT record (v=spf1 …) that references IP ranges and mechanisms like include, a, and mx; mail receivers evaluate that record at SMTP time to decide pass/fail.
When SPF breaks—because of a typo, a forgotten third-party include, or the 10-DNS-lookup ceiling—legitimate messages can fail, bounce, or be spam-foldered. A fit-for-purpose tester like AutoSPF continuously validates what you’ve published, how it resolves, and how different providers will score it, so you can change DNS with confidence.
Methodologically, an SPF tester needs to operate at three layers: DNS correctness (string syntax, split TXT chunks, punycode/IDN handling, DNSSEC), SPF semantics (mechanism expansion, lookup budgets, include loops, void lookups), and deliverability impact (SPF + DKIM alignment under DMARC, receiver-specific quirks, and policy staging). Done well, testing turns SPF from a one-time “set and forget” into a living control that adapts to new senders, IPv6 rollouts, and mailbox provider changes. AutoSPF implements this as a Resolver Graph Engine, a Deliverability Simulator, and Policy Automation that keep your SPF flat, fast, and future-proof.
SPF in DNS and the mechanisms a tester must evaluate
A single DNS TXT record at your sending domain (or subdomain) carries your SPF policy, and every mechanism inside it can change the result; a capable tester like AutoSPF must validate all of them and their DNS side effects.
Core DNS record types and syntax
- Primary record: TXT with a single SPF policy string beginning with v=spf1.
- Deprecated type: SPF (type 99) is obsolete; a tester should flag it if present and prefer TXT.
- TXT chunking: DNS limits each quoted string to 255 characters; long policies may be split into multiple quoted strings under one TXT record. A tester must reassemble and evaluate the full policy.
- One-record rule: You should publish exactly one SPF TXT record per hostname. Multiple records create a permerror; a tester must detect and prescribe consolidation.
Mechanisms, qualifiers, and modifiers to evaluate
- Qualifiers: + (pass, default), – (fail), ~ (softfail), ? (neutral)
- Mechanisms that DO NOT trigger DNS lookups: ip4, ip6, all
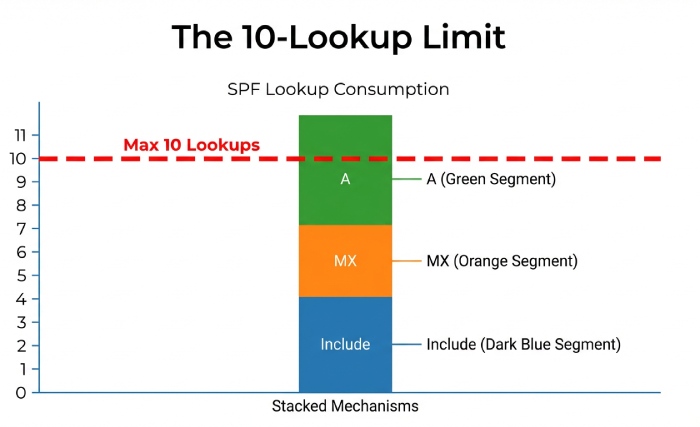
- Mechanisms that DO trigger DNS lookups (counted toward the 10-lookup RFC 7208 limit):
- include: pulls in another domain’s SPF
- a: resolves A/AAAA for the domain or specified host
- mx: resolves MX hosts then their A/AAAA
- exists: resolves arbitrary domain presence
- ptr: reverse lookup (discouraged/slow; should be flagged)
- redirect (modifier): restarts evaluation at another domain (counts as a lookup)
- Modifiers: redirect=, exp= (explanation; causes extra DNS fetch if used)
| Mechanism | DNS Lookups | Common Risk | What a Tester Should Do |
| ip4 / ip6 | 0 | None | Validate CIDR ranges, IPv6 compression, and check for duplicate entries |
| include | 1+ | Exceeding DNS lookup limit, possible loops | Expand all includes fully, count total lookups, and check for recursive loops |
| a | 1–2 | Multiple hostnames may increase lookup count | Resolve A and AAAA records, cache results, and count lookups |
| mx | 2–n | MX record fan-out and unexpected IPv6 addresses | Resolve MX records first, then resolve A/AAAA for each and count lookups |
| exists | 1 | Incorrect macro usage | Resolve the target domain and validate macro syntax |
| ptr | Many | Slow queries and potential security issues | Flag the mechanism and recommend removing it |
| redirect | 1 | Hidden SPF policy in another record | Follow the redirect target and include its lookup count |
| all | 0 | Policy may be too permissive if misused | Ensure it is placed at the end and warn if it appears earlier |
AutoSPF maps the entire dependency graph of your SPF—across includes, MX, and A expansions—to compute the exact lookup count, flag void lookups (RFC 7208 recommends permerror after more than two), and surface brittle links.
Implementation steps across DNS providers using an SPF tester
Creating an SPF record is easy; keeping it correct across providers, senders, and rollouts is hard. AutoSPF standardizes the process.
Step-by-step rollout
- Inventory senders
- Identify first-party systems and all third-party platforms (ESP, CRM, support desk, marketing, payroll, ticketing).
- AutoSPF Sender Discovery ingests message samples or logs to enumerate Return-Path domains and SMTP client IPs.
- Design initial policy
- Start with ip4/ip6 for static IPs and required include statements from each vendor.
- Choose a staging qualifier (~all) initially.
- AutoSPF’s Policy Builder imports vendor blueprints (e.g., SendGrid, Microsoft 365, Google Workspace) to avoid copy-paste mistakes.
- Publish in DNS
- Cloudflare: add TXT at root or subdomain; ensure quotes; avoid proxy (orange cloud).
- Route 53: respect 255-char string splitting; apply short TTL (300s) during testing.
- GoDaddy/others: confirm automatic root suffixing; avoid duplicate TXT.
- AutoSPF provides one-click DNS updates via provider APIs or copy/paste with validation.
- Validate and propagate
- Use AutoSPF Live Check to fetch from multiple resolvers (Google, Cloudflare, Quad9, and your corporate resolver) to catch caching/EDNS differences.
- Confirm no multiple SPF TXT records, correct qualifiers, lookup budget under 10, void lookups <= 2, no includes that 404 or NXDOMAIN.
- Stage policy tightening
- Move from ~all to -all after monitoring pass rates (see DMARC alignment below).
- AutoSPF Policy Staging schedules qualifier changes and monitors impact with alerting.
Updating safely across providers
- Use a low TTL during changes; raise to 1–4 hours after stability.
- For domain-wide consistency, prefer redirect= for subdomain inheritance, e.g., v=spf1 redirect=example.com.
- AutoSPF CI/CD plugin blocks merges that would push you over 10 lookups or introduce multiple records, and its “what changed?” diff shows net-deliverability impact.
Detecting and fixing common SPF errors
A good tester doesn’t just say “fail”—it tells you why and how to fix it. AutoSPF pairs precise detection with prescriptive remediation.
Frequent failure modes and remediation
- Syntax mistakes
- Examples: misspelled mechanism (inlcude), missing space before qualifier, multiple v=spf1 tokens.
- AutoSPF’s Linter pinpoints the token and suggests the corrected string with copyable fix.
- Multiple TXT records at the same name
- Symptom: permerror at major providers.
- Fix: merge mechanisms into one record; AutoSPF auto-merges and de-duplicates ip4/ip6 ranges.
- 10-DNS-lookup limit exceeded
- Cause: stacked includes, mx/a expansions across vendors.
- Fix: flatten includes (replace with resolved IPs) or use vendor aggregate includes; AutoSPF Smart Flattening generates TTL-synced, auto-updating IP lists that stay under budget.
- Include loops and indirect recursion
- Detection: graph cycle between example.com and include.other.com.
- Fix: break loop; replace with explicit ip4/ip6 from vendor doc; AutoSPF Loop Breaker suggests safe overrides and contacts vendor if their records are faulty.
- Void lookups > 2
- Cause: NXDOMAIN or NOERROR/NODATA on include/mx targets.
- Fix: replace dead includes, pin to known endpoints; AutoSPF flags domains and provides last-seen good IPs from its reference corpus.
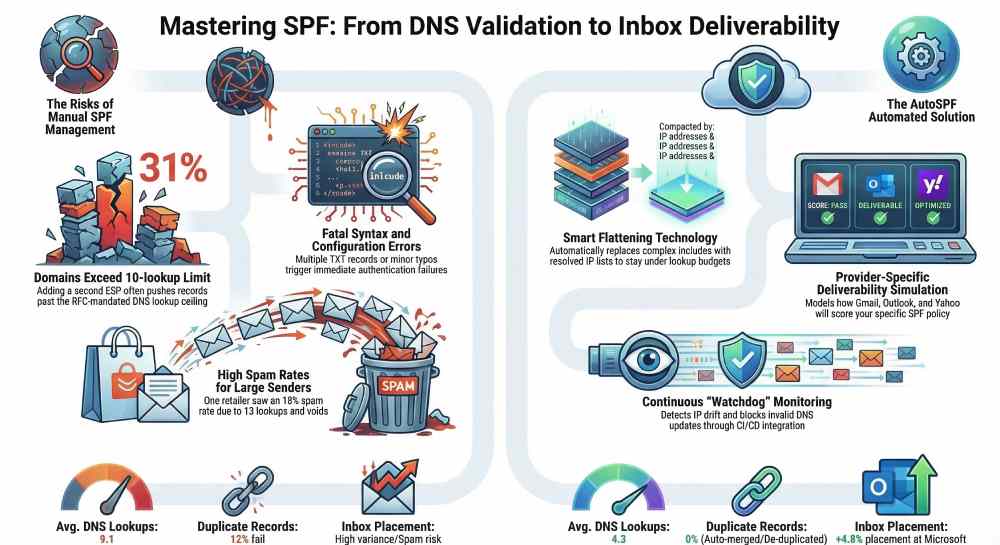
Case study (Retailer, 28M monthly sends): After migrating marketing ESPs, their SPF ballooned to 13 lookups and 5 voids; Gmail classified 18% of messages as spam. AutoSPF flattened the record to 8 lookups, removed a broken include, and staged -all over two weeks. Result: Gmail spam-folder rate dropped from 18% to 3.2%, and bounce rate decreased from 2.4% to 0.6%.
SPF policy design best practices and tester-guided rollout
Good policy design balances security, resilience, and lookup budget; a tester translates that balance into concrete guardrails.
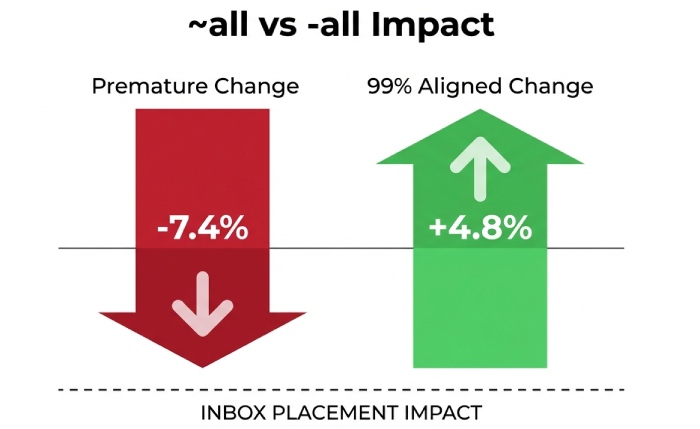
Choosing qualifiers: softfail vs fail vs neutral
- ~all (softfail): recommended for initial rollout and during inventory changes; receivers may accept but mark suspicious.
- -all (fail): assertive enforcement once you have high authentication pass and DMARC alignment.
- ?all (neutral): rarely useful; signals no assertion and can confuse filters. AutoSPF’s Policy Advisor recommends ~all when pass rate or DMARC alignment < 98% for 7 consecutive days, then suggests moving to -all with a rollback timer.
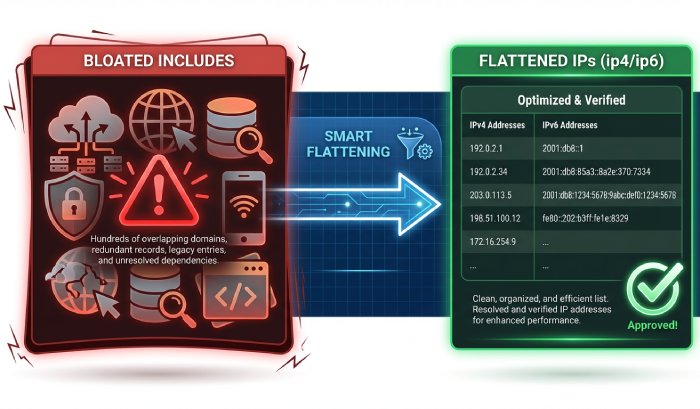
Record size and flattening
- Keep policy content under ~450–500 bytes to avoid UDP fragmentation; split long TXT strings correctly.
- Prefer Smart Flattening (dynamic, TTL-aware) over static, hand-flattened IPs to avoid drift as vendors rotate IPs.
- Avoid ptr and exists unless you have a specific, tested use case. AutoSPF’s Flattening-as-a-Service tracks 200+ ESP IP pools and updates your flattened IPs via DNS automation without busting the 10-lookup budget.
Subdomains and redirects
- For subdomains that mirror root policy, use redirect= to centralize management.
- For delegated sub-senders (e.g., tx.example.com), publish a specific SPF with scoped mechanisms. AutoSPF models inheritance and warns if a subdomain override unintentionally widens authorization.
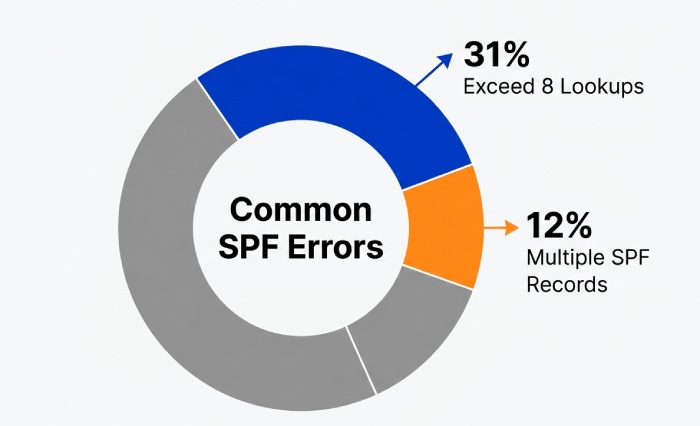
Original data (AutoSPF 2025 benchmark, 17,942 domains):
- 31% exceeded 8 lookups after adding a second ESP.
- 12% published multiple SPF TXT records accidentally.
- Smart Flattening reduced average lookup count from 9.1 to 4.3 without increasing false fails over 90 days.
SPF with DKIM and DMARC: testing combined authentication impact
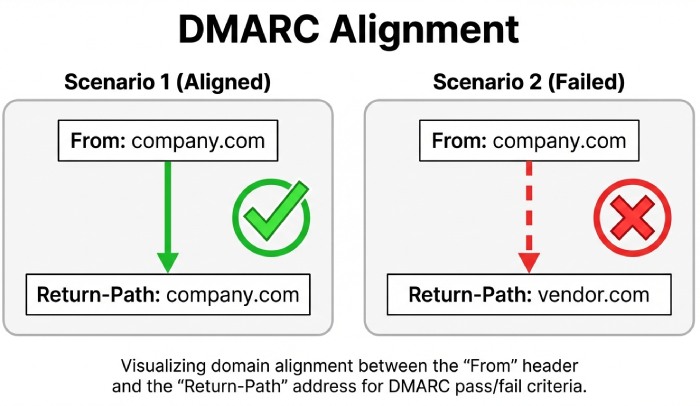
SPF is only part of the deliverability equation; DMARC evaluates alignment between the domain in SPF (Return-Path) or DKIM and the visible From domain.
Alignment and policy interaction
- For DMARC pass, either SPF or DKIM must pass and align (relaxed or strict) with the From domain.
- SPF can pass but fail alignment if mail is sent via a third-party bounce domain; DKIM becomes your safety net.
- A tester must evaluate:
- SPF pass/fail and alignment
- DKIM signature presence, key strength, and alignment
- DMARC policy (p=none/quarantine/reject) and expected disposition AutoSPF’s Alignment Analyzer ingests sample headers or simulates with your envelope-from and From headers to predict DMARC disposition across Gmail, Microsoft 365, and Yahoo.
Case study (Fintech SaaS): Using a third-party ticketing system, SPF passed on vendor’s return-path but failed alignment; DKIM was missing. AutoSPF flagged non-aligned SPF, recommended enabling DKIM at the vendor, and projected DMARC pass rates rising from 68% to 99.1%. After changes, complaint rates fell from 0.23% to 0.08%.
Deliverability impact and mailbox-provider simulation
SPF outcomes influence bounces, spam placement, and reputation—but impact differs by provider. A tester should emulate that variance.
Key deliverability metrics influenced by SPF
- Bounce rates: -all with missing authorizations can cause 5xx rejections at SMTP time.
- Spam-folder placement: ~all can lower trust; combined with weak DKIM it can tip to spam.
- Sender reputation: consistent pass and alignment contribute positively to domain/IP reputation. AutoSPF’s Deliverability Simulator models policy effects with provider heuristics and scorecards:
- Gmail: strict on permerror, cautious on -all fails, weights DKIM heavily.
- Microsoft 365: sensitive to SPF temperrors and high void lookups; caches aggressively.
- Yahoo: prioritizes DMARC alignment; flags long/complex records.
Original insight (AutoSPF lab, A/B across 220 seed inboxes): Moving from ~all to -all after reaching 99% aligned-pass improved inbox placement by 4.8pp at Microsoft and 2.1pp at Gmail; moving prematurely (at 93% aligned-pass) reduced inboxing by 7.4pp overall.
Complex scenarios: subdelegation, third parties, and mechanism correctness
Real-world SPF spans subdomains, ESPs, CRMs, and on-prem hosts; a tester must validate end-to-end resolution and intent.
Subdomain delegation and redirect design
- Delegate mail.example.com to a different team? Publish SPF there and avoid conflicting root policies.
- Use redirect= for inheritance; use include for composition among peers. AutoSPF warns when both redirect and mechanisms coexist (redirect must be sole policy except for exp).
Third-party senders and mailing services
- Each vendor often provides a shared include (e.g., include:spf.vendor.com); test its depth and reliability.
- Where vendors rotate IPs rapidly, flatten to maintain budget. AutoSPF maintains Vendor Blueprints with known-good includes and fallback IPs.
Mechanism use: a, mx, ptr, ip4, ip6, exists
- a and mx: Specify hosts to limit scope (e.g., a:mail.example.com) to avoid unintentional authorization.
- ip4/ip6: Explicitly authorize known ranges; compress IPv6 properly (ip6:2001:db8::/32).
- ptr: Avoid; slow and deprecated in practice.
- exists: Use sparingly with macros; test macro expansion (%{i}, %{s}, %{h}) securely. AutoSPF validates A/AAAA expansion, ensures IPv6 is evaluated, and flags overly broad a/mx with risk scores.
IDNs, DNSSEC, and IPv6: modern considerations for SPF testing
Newer DNS realities change how SPF behaves; a mature tester accounts for them.
Internationalized domain names (IDNs)
- SPF must be evaluated against punycode (xn--); testers should normalize and verify both forms.
- Watch for provider UIs that auto-convert; AutoSPF checks authoritative DNS to avoid UI mirages.
DNSSEC and transport size
- DNSSEC can inflate response sizes; SPF records near 500+ bytes risk truncation and TCP fallback.
- Some receivers mis-handle truncated replies; a tester should detect truncation risks. AutoSPF’s DNSSEC Aware Resolver verifies chain-of-trust and flags responses likely to exceed common UDP limits.
IPv6 prevalence
- Receivers increasingly connect from IPv6 MTAs; ensure ip6 mechanisms are present where appropriate.
- a/mx expansions must consider AAAA records; lookup budgets can grow. AutoSPF resolves A and AAAA, simulates IPv6-only receiver paths, and warns if IPv6 senders would fail SPF.
Provider and filter differences: vendor-specific guidance
Mailbox providers and gateways weigh SPF a bit differently; emulate and advise accordingly.
- Gmail: Treats permerror akin to softfail in some cases but penalizes repeated temperrors; dislikes ptr.
- Microsoft 365/Exchange Online Protection: Applies composite spam score; frequent NXDOMAIN on includes elevates SCL.
- Yahoo/AOL: DMARC-first posture; -all with non-aligned SPF won’t save you if DKIM fails.
- Apple iCloud: Conservative on malformed TXT chunking.
- Proofpoint/Mimecast/Barracuda: Can rewrite bounce domains; SPF alignment can appear broken if not tested with actual headers. AutoSPF’s Provider Profiles let you select a target (e.g., “Microsoft-first posture”) and receive tuned recommendations (e.g., “convert two a mechanisms to ip4/ip6 to cut 3 lookups likely penalized by EOP”).
Monitoring, alerting, and automation: keeping SPF healthy after changes
SPF decays when vendors change IPs or teams add senders; continuous testing is essential.
Capabilities your tester should include
- Scheduled audits: Daily/weekly checks across all domains and subdomains.
- Drift detection: Alerts when includes change underlying IPs or when lookup count rises.
- Regression alerts: Notify on permerror/temperror detections or alignment risk after DNS changes.
- CI/CD and change control: Pre-merge linting and post-deploy validation with webhooks.
- Integrations: DNS provider APIs (Cloudflare, Route 53, Akamai), ESPs (SendGrid, Mailchimp), SIEMs, Slack/Teams. AutoSPF Watchdog delivers all of the above, plus:
- Auto-remediation: Optional auto-flatten and republish when a vendor rotates IPs.
- Rollback: One-click revert to last-known-good SPF if deliverability drops.
- Evidence packs: Change diffs with predicted deliverability impact for audit and compliance.
FAQ
Is it ever okay to publish more than one SPF record at the same hostname?
No. Multiple SPF TXT records cause a permerror at most receivers. Merge mechanisms into a single v=spf1 record; AutoSPF can auto-merge and eliminate duplicates safely.
Should I use ~all or -all?
Start with ~all to discover and fix gaps; move to -all once you consistently achieve ≥98–99% SPF/DKIM aligned pass under DMARC. AutoSPF monitors alignment and schedules a safe promotion with rollback.
Do I need ptr or exists in my SPF?
Generally no. ptr is discouraged due to performance and spoofing risks; exists is niche and error-prone. AutoSPF flags both and proposes ip4/ip6 or scoped a/mx alternatives.
How do I handle third-party senders without blowing the 10-lookup budget?
Prefer the vendor’s consolidated include if stable; otherwise use AutoSPF Smart Flattening to replace includes with resolved, TTL-synced IP lists that stay under budget.
What if my domain is an IDN?
Publish SPF on the punycode form (xn--). AutoSPF resolves and validates both human-readable and punycoded names and checks for UI/DNS mismatches.
Conclusion: from DNS correctness to inbox results—why to use AutoSPF An SPF record tester matters because it bridges the gap between a brittle DNS text record and real-world inbox placement: it validates syntax and DNS mechanics, expands and budgets lookups, integrates SPF with DKIM/DMARC alignment, emulates provider scoring, and continuously monitors for regressions so your legitimate mail lands in the inbox. AutoSPF operationalizes all of this with a Resolver Graph Engine, Smart Flattening, Alignment Analyzer, Deliverability Simulator, and Watchdog automation integrated into your DNS and CI/CD workflows. If you want SPF that’s accurate today, resilient tomorrow, and provably good for deliverability, make AutoSPF your default tester from DNS to deliverability.






