Google & Yahoo’s Bulk Sender Mandate: What Changed in Two Years

Quick Answer
On October 3, 2023, Google and Yahoo jointly announced new sender requirements that would take effect February 1, 2024. It was the first time two of the world’s largest inbox providers coordinated mandatory authentication requirements at scale, and it caught most of the industry flat-footed.
The Numbers, the Gaps, and What Senders Still Need to Fix
TL;DR
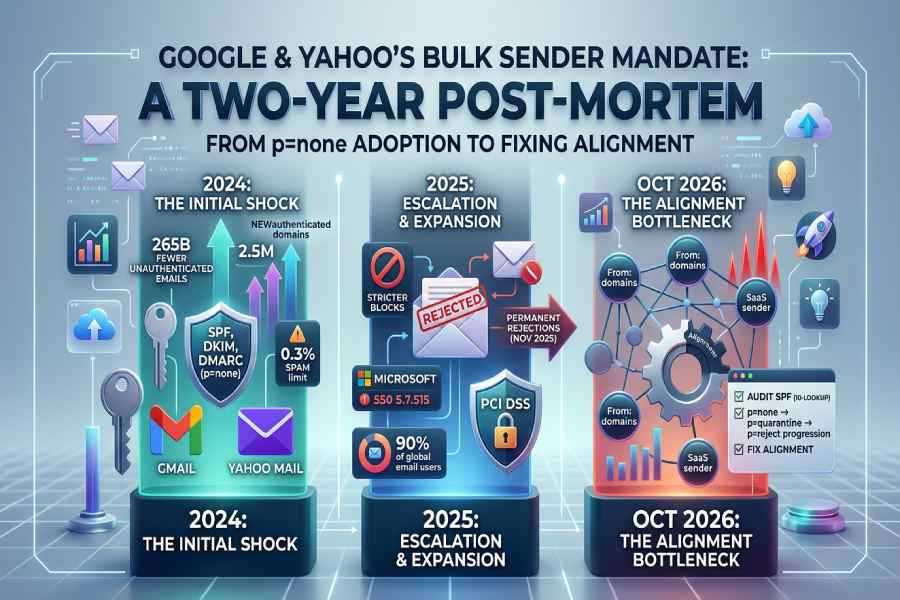
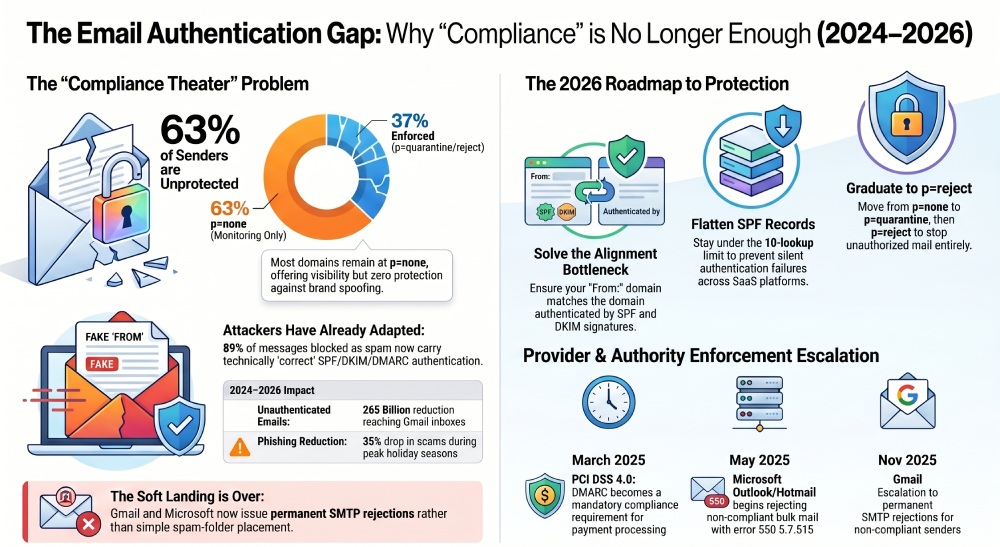
- The mandate worked, at macro scale. 265 billion fewer unauthenticated emails reached Gmail inboxes in 2024 (a 65% reduction), 2.5 million domains newly implemented authentication in the first 60 days of 2024, and holiday-season phishing dropped 35% (Valimail; Dark Reading).
- But adoption was shallow. dmarcian found that ‘the vast majority of domains that came in during this surge have stayed at p=none’ (dmarcian). Fortra’s Q2 2025 data shows 63% of DMARC-publishing senders sit at p=none, visibility without protection (Fortra).
- The mandate is expanding, not contracting. Microsoft matched in May 2025 with error 550 5.7.515. PCI DSS 4.0 added DMARC as a compliance mandate in March 2025. Gmail escalated to permanent rejections in November 2025. Apple, Google, Yahoo, and Microsoft together reach ~90% of global email users.
- Attackers adapted faster than many expected. Cloudflare found 89% of messages blocked as spam now carry correct SPF/DKIM/DMARC (Cloudflare via Dark Reading). Authentication is necessary but insufficient.
- Alignment is the new bottleneck. As SaaS sprawl grows, misalignment between ‘From:’ domains and authentication domains is now the #1 rejection reason (Mailbird; Mimecast). This is where most post-2024 ‘compliance’ quietly breaks.
- What to do next: audit SPF for the 10-lookup limit, publish rua= reporting addresses on every domain, plan the p=none → p=quarantine → p=reject progression, and fix alignment across every SaaS sender. The action plan at the end of this article walks through each step.
1. A brief recap: what changed on February 1, 2024
On October 3, 2023, Google and Yahoo jointly announced new sender requirements that would take effect February 1, 2024. It was the first time two of the world’s largest inbox providers coordinated mandatory authentication requirements at scale, and it caught most of the industry flat-footed. Senders dispatching more than 5,000 emails per day to personal Gmail or Yahoo Mail accounts were now required to implement SPF, DKIM, and DMARC (minimum policy p=none), enable one-click unsubscribe, and keep spam complaint rates below 0.3%.
The threshold matters. The 5,000/day number applies specifically to messages reaching consumer inboxes, @gmail.com, @googlemail.com, and Yahoo-hosted domains. Subdomains roll up to the parent. Internal Google Workspace traffic is exempt. New domains that started sending bulk email after January 2024 face accelerated enforcement scrutiny from day one.
At launch, Google’s context for the move was already striking: Gmail blocks approximately 15 billion unwanted emails every day and stops 99.9% of spam, phishing, and malware. The mandate wasn’t designed to create a filter where none existed, it was designed to tighten what was already the strictest filter in the industry. The question going into 2024 was whether the industry would comply, how fast, and what it would actually change.
Two years in, we have answers. Some of them are better than expected. Some of them are worse. And one of them, about where compliance quietly breaks, has specific operational implications for every enterprise still sending at scale in 2026.
2. The mandate timeline, how enforcement escalated
The single most important thing to understand about the Google/Yahoo mandate is that it was never a one-time event. It is a rolling enforcement program that has added new providers, new requirements, and stiffer consequences approximately every six months. Here is the timeline as of April 2026.
| Date | Event | What it meant for senders |
|---|---|---|
| October 3, 2023 | Google & Yahoo announce joint mandate | First industry-wide authentication requirement. 90-day runway to February 1, 2024 enforcement. |
| February 1, 2024 | Enforcement begins (Google, Yahoo, Apple) | Temporary errors on small percentage of non-compliant traffic. Soft landing, not immediate rejection. |
| April 2024 | Google begins progressive rejections | Rejection rate gradually ramped. If 75% of a sender’s traffic was compliant, Google started rejecting the remaining 25%. |
| June 1, 2024 | One-click unsubscribe deadline | RFC 8058 List-Unsubscribe-Post header required for commercial email. |
| October 2024 | Google publishes 1-year results at M3AAWG | 265 billion fewer unauthenticated emails; 65% reduction; 2.5M new authenticated domains in 60 days. |
| January 1, 2025 | Microsoft ERR limit (new tenants) | 2,000 recipients/24hr limit on Exchange Online for newly created tenants. Phase 1 of broader rollout. |
| March 31, 2025 | PCI DSS v4.0 DMARC mandate | DMARC required for any company handling credit cards. Non-compliance threatens payment processing rights. |
| May 5, 2025 | Microsoft matches Google/Yahoo | Outlook.com, Hotmail, Live.com reject non-compliant bulk mail with error ‘550 5.7.515 Access denied.’ |
| July-Dec 2025 | Microsoft ERR limit (existing tenants) | 2,000 recipients/24hr limit rolled out to all existing Exchange Online tenants. |
| November 2025 | Gmail escalates to permanent rejection | Non-compliant messages now receive SMTP rejection codes (5.7.26, 5.7.25), not spam-folder placement. |
| April 2026 | Current state | Four providers = ~90% of global email users enforcing uniform authentication. Mandate now regulatory, not aspirational. |
What it means: If your organization implemented the bare minimum in early 2024 and considered the work complete, you have already fallen behind three additional enforcement waves. The mandate’s trajectory has been strictly tightening. There is no scenario under which the requirements relax; every signal from Google, Yahoo, Microsoft, and the regulatory side (PCI DSS v4.0) points to stricter enforcement, not looser.
3. Google’s measured results: what actually worked
At the October 2024 M3AAWG meeting, Google shared the first comprehensive measurement of the mandate’s impact. The numbers, widely circulated through Valimail and Dark Reading, are the best available data on what authentication enforcement achieves at scale.
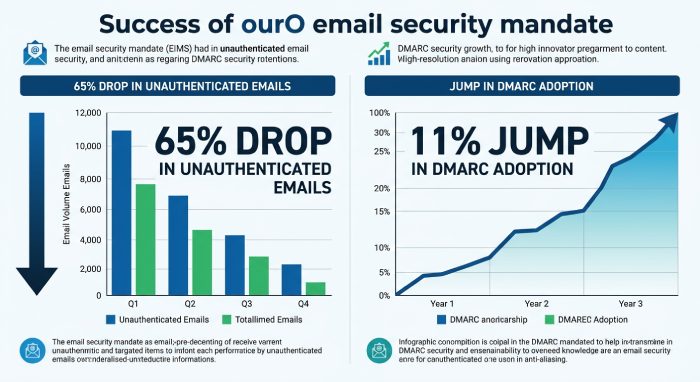
The headline number is difficult to comprehend. Gmail users received 265 billion fewer unauthenticated emails in 2024 than in 2023, a 65% year-over-year reduction in unauthenticated messages reaching Gmail inboxes. Google described this as a ‘lasting structural reduction’ in the email ecosystem, not a temporary compliance blip. In pure volume terms, that is roughly equivalent to every person on Earth receiving 33 fewer unauthenticated messages that year.
The behavioral shift is equally important. 50% more bulk senders began following email security best practices in 2024 compared to the pre-mandate baseline, the largest single-year shift in sender-side authentication behavior in DMARC’s decade-plus history. And the attack impact was measurable during peak conditions: during the 2024 holiday shopping season, historically the highest-volume phishing period of the year, Gmail users encountered 35% fewer phishing scams than during the equivalent 2023 period (Dark Reading citing Neil Kumaran, Google).
The adoption velocity was unprecedented. In the first 60 days of 2024 alone, 2.5 million domains newly implemented email authentication and/or DMARC policy records, including over 500,000 domains within the top 10 million most-trafficked internet domains. DMARC adoption rate among Google-received email doubled year-over-year, from 55,000 new domains per month in 2023 to 110,000 new domains per month in 2024. Overall DMARC adoption grew from 42.6% in 2023 to 53.8% in 2024, an 11-percentage-point jump in a single year, the largest single-year gain DMARC has ever recorded.
“These changes are like a tune-up for the email world, and by fixing a few things under the hood, we can keep email running smoothly. But just like a tune-up, this is not a one-time exercise.”
What it means: When mandates have teeth, the industry moves. The 2024 data demonstrates that authentication adoption, long described as ‘slow,’ ‘complicated,’ and ‘resistant’, can shift by double-digit percentage points in a single year when the commercial consequence of non-compliance is clear. That is the single most important takeaway for any internal case for accelerated DMARC deployment: the infrastructure-side delays that most IT organizations cite for slow adoption are, in practice, organizational rather than technical.
4. The p=none problem: why the adoption numbers are misleading
Here is where the mandate’s success story gets complicated. Published DMARC records come in three flavors: p=none (monitoring only, no protection), p=quarantine (failed mail goes to spam), and p=reject (failed mail is rejected at SMTP level). The 2024 mandate required only p=none, the lowest rung on the DMARC ladder. Organizations could check the compliance box without actually protecting their domain from spoofing.
Most did exactly that. dmarcian’s November 2024 retrospective, based on the platform’s direct visibility into millions of domains, found that the vast majority of domains that came in during the surge have stayed at p=none, and will likely remain so until Google or Yahoo require a stronger level of enforcement. This finding is the single most important ‘one year later’ number that isn’t on anyone’s celebration slide.
“The vast majority of the domains that came in during this surge have stayed at p=none, and will likely remain so until Google or Yahoo update their guidance and require a stronger level of enforcement.”
The broader industry picture confirms dmarcian’s direct observation. Across the top 10 million internet domains, Fortra’s Q2 2025 analysis found that only 37% of senders implementing DMARC use enforcement policies, meaning 63% sit at p=none with no protection against spoofing. Post-mandate, two-thirds of DMARC-publishing domains are still effectively unprotected.
The quality problem compounds. Valimail’s post-mandate analysis noted that most email marketers who rushed to comply implemented DMARC records without rua= reporting mechanisms. Aggregate reporting (rua=) is the feature that tells a domain owner when authentication fails, which sources are sending legitimate mail, and who is attempting to spoof the domain. A DMARC record without rua= is a checkbox. A DMARC record at p=none without rua= is a checkbox that can’t even detect its own failures.
Meanwhile, domains stuck at p=none are actively attractive targets. Attackers scan for them specifically, because the record signals that the domain owner has not yet graduated to enforcement, which means spoofed mail from that domain still has a shot at delivery. In the post-mandate landscape, publishing p=none without progressing further can increase your attack surface, not decrease it.
What it means: The difference between ‘we published DMARC’ and ‘we are protected by DMARC’ is enormous. If your organization falls in the 63%-at-p=none majority, your compliance story is technically true but operationally false. The advertised benefits of DMARC, spoofing prevention, brand protection, measurable reduction in phishing, all require enforcement. p=none gives you visibility at best, and a false sense of security at worst.
5. The cascade: Microsoft, Apple, PCI DSS, and the regulatory layer
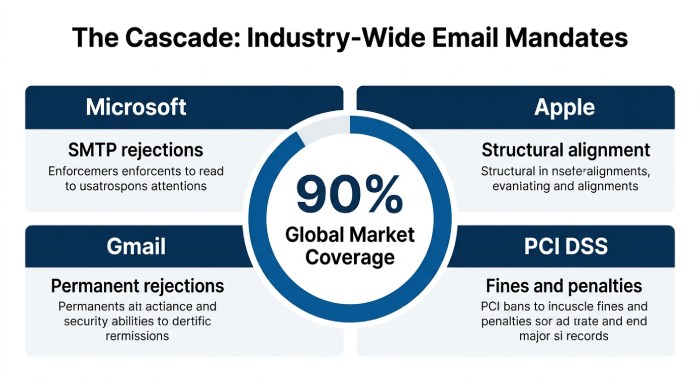
One of the most consequential second-order effects of the 2024 mandate is how fast it spread beyond Google and Yahoo. In 2025, three separate expansions turned what began as an ISP-driven guideline into an industry-wide regulatory posture.
Microsoft (May 5, 2025). Microsoft matched the Google/Yahoo requirements for Outlook.com, Hotmail, and Live.com, rejecting non-compliant bulk-sender mail (5,000+/day) with the specific error code ‘550 5.7.515 Access denied, sending domain does not meet the required authentication level.’ This was a decisive change: Microsoft had previously spam-foldered non-compliant mail, giving senders a soft landing. The May 2025 shift made rejection explicit at the SMTP level. Anyone seeing that error code in their bounce logs is being told, unambiguously, that their authentication posture has failed Microsoft’s filter.
Microsoft ERR (January-December 2025). Less discussed but operationally critical: Microsoft introduced an External Recipient Rate limit of 2,000 recipients per 24 hours on Exchange Online, rolled out to new tenants in January 2025 and to existing tenants between July and December 2025. Microsoft is actively pushing bulk senders off Exchange Online and toward Azure Communications Services for Email. Organizations that had been using Exchange Online as a quasi-ESP are being forced to either migrate or restructure.
Apple (February 2024). Apple joined the authentication-mandate movement quietly but simultaneously with Google and Yahoo in early 2024. Apple’s announcements were less publicized, but the requirements are structurally similar. Combined with Google, Yahoo, and Microsoft, the four providers now serve approximately 90% of consumer and business email users globally. There is effectively no ‘escape hatch’ inbox provider that allows bulk senders to skip authentication.
PCI DSS v4.0 (March 31, 2025). The Payment Card Industry Security Standards Council added DMARC as a mandatory requirement in PCI DSS version 4.0, applicable to any company handling credit cards or operating in financial services. The teeth are significant: non-compliance with PCI DSS can lead to fines, penalties, and, at the extreme, loss of the right to process payments. For the first time, DMARC is not just a deliverability concern or an ISP-compliance concern but a direct regulatory-compliance requirement. For e-commerce, fintech, and any organization in the card-acceptance ecosystem, DMARC moved from ‘should do’ to ‘must do’ in a single quarter.
Gmail permanent rejections (November 2025). Gmail escalated enforcement from progressive temporary errors to outright permanent rejections in November 2025. The transition removed the ‘soft landing’ that had given non-compliant senders a year-plus to fix their setups. Common enforcement codes now include 5.7.26 (authentication failure) and 5.7.25 (invalid PTR records). Each of these appears in bounce logs of enterprises that never fully completed their 2024 compliance work.
“The 2024-2025 cascade removed the last economically rational reason to delay authentication. Every organization that processes payments, sends commercial email, handles federal data, or operates in a regulated market is now subject to at least one DMARC-related mandate.”
6. Attacker adaptation: what the mandate didn’t fix
No analysis of the mandate is honest without engaging the counter-narrative. Authentication mandates shift attacker economics; they don’t eliminate attacker behavior. The evidence for that is uncomfortable and quantitative.
Cloudflare’s analysis, cited in Dark Reading’s coverage of the mandate, found that 89% of messages blocked as spam had correct SPF, DKIM, or DMARC information. Read that again. Nine out of ten messages that email filters correctly identify as spam are, technically, properly authenticated. Attackers have not been defeated by the mandate; they have adapted to it.
Three specific adaptations are now dominant in the post-mandate attack landscape:
- Lookalike domains with their own authentication. Attackers register domains that look like legitimate brands (examplebank.com → exsamplebank.com, or examplebank.scam.com), then publish complete SPF, DKIM, and DMARC records for the fraudulent domain. The receiving server sees properly authenticated mail from a legitimate-looking domain. As Roger Grimes noted in Dark Reading: ‘Phishers just created new illegitimate domains, often with lookalike names, that they then applied DMARC on.’
- Subdomail attacks. Attackers hunt SPF records that include unregistered or orphaned domains, typically abandoned vendor subdomains or acquired-company domains, and then take control of the abandoned domains to run authenticated spam campaigns. One documented case: the SPF record for msnmarthastewartsweeps.com included two orphaned domains that attackers weaponized. The attacker’s mail passed SPF alignment because the SPF record specifically authorized them.
- Exploitation of legitimate ESP infrastructure. Attackers compromise legitimate bulk-sender accounts at major ESPs and send from infrastructure that is already authenticated and reputation-scored as trustworthy. Mailbox providers see mail from Mailgun, SendGrid, or Constant Contact IPs with valid authentication; the filter trusts it. This is the hardest vector to defend against, because legitimate and illegitimate mail is sharing sending infrastructure.
The sector-specific gap is also instructive. Healthcare DMARC adoption is struggling to surpass 40%-50%, despite healthcare being repeatedly named as the costliest industry for breaches, with the longest containment times, and the most sensitive data. Authentication gaps in healthcare compound the sector’s existing exposure rather than mitigating it.
What it means: Authentication is necessary but not sufficient. The mandate’s genuine success is that it shifted the baseline, legitimate mail now arrives authenticated, which gives receiving filters cleaner signal on which to base classification. But treating DMARC-at-enforcement as a complete anti-phishing solution will produce exactly the kind of complacency that leaves organizations vulnerable to the adapted attack techniques documented above. Authentication + content inspection + URL isolation + user training is the only posture that handles the current threat model.
7. The real bottleneck in 2026: alignment, not authentication
Here is the finding most enterprise IT teams are not prepared for. In the post-November-2025 enforcement environment, the most common cause of Gmail message rejection is not missing authentication, it is alignment failure. Mailbird’s post-enforcement analysis identifies this specifically: a sender can have SPF, DKIM, and DMARC all properly configured and still have their mail rejected if the ‘From:’ domain shown to recipients doesn’t match the domain authenticated by SPF or DKIM.
Why does alignment fail so often? Because enterprises have dozens of SaaS platforms sending on their behalf, and each one’s alignment configuration is independent. Mimecast’s 2026 analysis is blunt about where this lands: ‘As organizations adopt more SaaS and third-party email services, alignment problems have become one of the most common DMARC issues. Ensuring proper alignment across all email channels, marketing platforms, ticketing systems, CRM automation, and cloud applications, is now essential for maintaining deliverability.’
The mechanism is specific. SPF alignment requires that the ‘Return-Path’ domain match the organizational ‘From:’ domain. DKIM alignment requires that the d= parameter in the DKIM signature match the organizational ‘From:’ domain. Most SaaS vendors default to sending from their own infrastructure with their own domain in the Return-Path or d= parameter, which causes alignment to fail even when authentication itself passes. The result is a sender who has dutifully enabled SPF, DKIM, and DMARC and still has mail rejected at SMTP level.
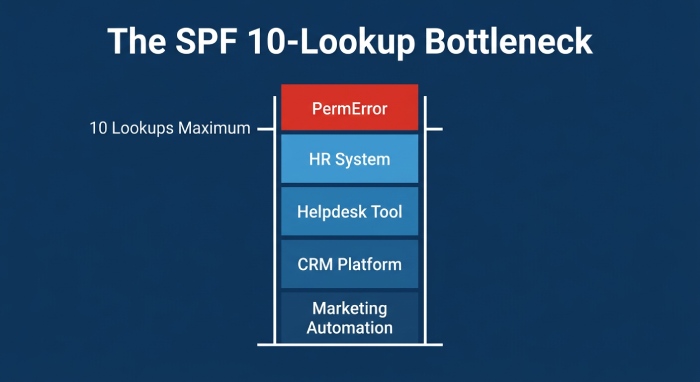
The underlying enabler is the 10-lookup SPF limit defined in RFC 7208. Every include: mechanism in an SPF record counts against the ceiling, and vendor includes nest. A typical enterprise today authorizes SPF includes for marketing automation, transactional email (SendGrid, Mailgun, Postmark), HR platforms, CRM (Salesforce, HubSpot), helpdesk (Zendesk, Freshdesk), ERP notifications, and security vendors. Each one consumes 1-3 lookups. The ceiling is reached roughly when an enterprise adopts its third major SaaS platform. Exceed it, and SPF returns PermError. DMARC then loses half of its authentication basis. A domain at p=reject with broken SPF starts rejecting its own legitimate mail. A domain at p=none silently lets spoofed mail through.
This is the gap that cost most of the 63%-stuck-at-p=none their progression. They tried to move from p=none to p=quarantine. Legitimate mail started bouncing. They rolled back. They never returned.
What it means: Authentication work that didn’t solve SPF lookup and alignment is authentication work that will eventually fail. In 2024, most enterprises could get to p=none without confronting this problem. In 2026, with Gmail at permanent rejection and Microsoft at 550 5.7.515, the alignment problem is the specific reason compliant-on-paper senders are losing mail. The fix is: SPF flattening to stay under the 10-lookup ceiling, DKIM signing with your domain (not the vendor’s) as d=, delegation of bulk mail to subdomains, and automated refresh cycles because vendor IP pools change weekly.
8. The 90-day action plan: compliance → protection → resilience
The gap between ‘our domain is DMARC-compliant’ and ‘our domain is DMARC-protected‘ is operational, not conceptual. The plan below gets you across that gap in three phases. It is the same plan that would have worked in 2024, but with two years of enforcement escalation behind us, the consequences of not executing it are significantly sharper.
Days 1-30: Measure the gap
- Audit SPF lookup counts across every sending domain. Use a tool that counts nested DNS lookups, not just visible mechanisms. If any active domain is at 8 or higher, you are one vendor addition away from silent PermError. Flatten before doing anything else.
- Inventory every sending source. List every SaaS platform, vendor, and internal system that sends email on your behalf. Typical enterprises discover 30-60+ legitimate senders they hadn’t documented. Each one is a potential alignment failure.
- Publish DMARC records on every active domain, including parked domains. Attackers prefer unmonitored parked domains for lookalike spoofing. Adding a p=none record with a valid rua= address costs nothing and gives you immediate visibility into impersonation attempts.
- Validate that every existing DMARC record has a rua= reporting address. If you inherited a DMARC record from a 2024 rush-to-comply deployment, check this first. Records without rua= are invisible; you cannot fix what you cannot measure.
- Check Google Postmaster Tools Compliance Status for every sending domain. Google’s free tool tells you which domains are ‘Compliant’ vs ‘Needs Work’ and flags specific failures. If any domain shows ‘Needs Work,’ that is your priority queue.
Days 31-60: Fix the plumbing
- Flatten SPF. Resolve nested includes into an IP-based record under the 10-lookup ceiling. Automate the refresh cycle, vendor IP pools change weekly, so static flattening breaks within a month.
- Enable DKIM signing on every sending source, with your domain in the d= parameter, not the vendor’s. This is the step most enterprises skipped in 2024. It is also the step that makes DMARC enforcement feasible when SPF breaks.
- Delegate bulk mail to subdomains. Marketing from marketing.example.com; transactional from mail.example.com; HR from hr.example.com. This isolates reputation, enables differentiated DMARC policies, and protects the primary domain if any single vendor fails.
- Wire aggregate DMARC reports to a parser. Raw XML is unusable at scale. Use a DMARC analysis platform to categorize senders automatically. Without this, the rest of the plan is invisible.
- Verify one-click unsubscribe is implemented correctly. Both List-Unsubscribe-Post: List-Unsubscribe=One-Click and List-Unsubscribe headers must be present. The unsubscribe endpoint must use POST, not GET, GET endpoints are frequently triggered by email security scanners and cause unintended unsubscribes.
Days 61-90: Move to enforcement and sustain
- Move to p=quarantine with pct=10. DMARC’s pct tag lets you apply the policy to a percentage of failing mail. Start small. Monitor aggregate reports daily for legitimate senders you didn’t know about.
- Ramp the percentage. pct=10 → 25 → 50 → 75 → 100. Each step should run for 2-3 weeks with no legitimate-mail failures before advancing. Complex sending environments take 90-180 days; simpler ones move faster.
- Move to p=reject. At p=reject with pct=100, receiving servers silently drop mail that fails DMARC alignment. This is the only posture that actually prevents domain spoofing. By this point, aggregate reports should show 99%+ alignment on legitimate mail.
- Monitor spam complaint rates in Google Postmaster Tools. The hard ceiling is 0.3%. The operational target is 0.1%. Rates above 0.3% trigger enforcement territory where mail faces delivery problems regardless of technical authentication status.
- Establish a quarterly re-audit cycle. SaaS sprawl is continuous. Every new vendor added after your initial cleanup is a potential SPF-lookup or DKIM-alignment regression. The enterprises losing mail in 2026 are the ones who treated 2024 compliance as a project, not a process.
9. The bottom line: compliance was the easy part
Two years in, the Google/Yahoo mandate has produced the largest authentication adoption shift in internet history. 265 billion fewer unauthenticated emails in a single year is a genuine, measurable improvement in the email ecosystem’s hygiene. 2.5 million newly authenticated domains in 60 days is the kind of result cybersecurity programs rarely achieve. Neil Kumaran was right to call it a tune-up, the ecosystem genuinely runs better than it did in January 2024.
But the dmarcian finding is the one to internalize. The vast majority of domains that came in during the surge stayed at p=none. The Fortra data quantifies it: 63% of DMARC-publishing senders are at p=none and providing no actual spoofing protection. The Cloudflare data adds the attacker side: 89% of messages now blocked as spam carry correct authentication. And the Mailbird and Mimecast findings close the loop: alignment, not the presence or absence of DMARC records, is the specific reason compliant-on-paper senders are losing mail to Gmail and Microsoft in 2026.
The question for every enterprise reading this is the same: are you in the 37% with enforcement, or the 63% with compliance theater? The mandate’s first phase asked whether you had a DMARC record. The second phase, the one that is playing out right now, unevenly and without a single announcement date, is asking whether that record does anything. Senders who planned only for phase one are finding out the hard way.
If you take one number into your next quarterly planning meeting, take this one: 63% of DMARC-publishing domains are still unprotected. That is the size of the remaining opportunity for attackers and the size of the remaining work for defenders. The next enforcement wave, whatever provider announces it, will assume you’ve already done the work. The soft landing is over.
References
Every statistic in this article is sourced from a publicly accessible document, direct Google data shared at M3AAWG and contextualized by Valimail and Forbes, dmarcian’s November 2024 one-year retrospective (the canonical post-mandate analysis), Fortra’s Q2 2025 enforcement-quality data, Cloudflare’s authenticated-spam analysis (via Dark Reading), and industry coverage from Mimecast, PowerDMARC, MarTech, Sinch Mailgun, and EmailWarmup. All URLs are written out in full so attribution survives format conversion.
- BleepingComputer, Google bulk sender defenses announcement. https://www.bleepingcomputer.com/news/security/google-to-bolster-phishing-and-malware-delivery-defenses-in-2024/
- dmarcian, The Rise of DMARC Adoption: Google and Yahoo’s Mandate. https://dmarcian.com/dmarc-adoption-google-yahoo/
- Valimail, Google Stats Show Why DMARC Matters (M3AAWG data). https://www.valimail.com/blog/google-stats-dmarc/
- Dark Reading, Google’s DMARC Push Pays Off, But Challenges Remain. https://www.darkreading.com/remote-workforce/google-dmarc-push-email-security-challenges
- Dark Reading, Google, Yahoo Push DMARC, Forcing Companies to Catch Up. https://www.darkreading.com/cybersecurity-operations/google-yahoo-push-dmarc-forcing-companies-to-catch-up
- B2B Email Deliverability Report 2025 (Fortra Q2 2025 data). https://thedigitalbloom.com/learn/b2b-email-deliverability-benchmarks-2025/
- Higher Logic, New Bulk Sender Requirements (Microsoft enforcement detail). https://support.higherlogic.com/hc/en-us/articles/21639835567124-New-Bulk-Sender-Requirements
- MarTech, Bulk email restrictions from Google, Yahoo and Microsoft. https://martech.org/new-rules-for-bulk-email-senders-from-google-yahoo-what-you-need-to-know/
- Mimecast, DMARC Google Workspace, Yahoo, & Microsoft Requirements. https://www.mimecast.com/blog/guide-to-google-dmarc-setup/
- Mailbird, Gmail Spam Filter Changes and Alignment. https://www.getmailbird.com/gmail-spam-filter-changes-legitimate-emails/
- Sinch Mailgun, State of Email Deliverability: Yahoogle Bulk Senders. https://www.mailgun.com/state-of-email-deliverability/chapter/yahoogle-bulk-senders/
- PowerDMARC, Google and Yahoo Email Authentication Requirements 2025-2026. https://powerdmarc.com/google-and-yahoo-email-authentication-requirements/
- EmailWarmup, Gmail and Yahoo Bulk Sender Requirements [2026 Update]. https://emailwarmup.com/blog/gmail-and-yahoo-bulk-sender-requirements/
- Security Boulevard, Email Phishing and DMARC Statistics. https://securityboulevard.com/2024/11/email-phishing-and-dmarc-statistics/
Topics

General Manager
Founder and General Manager of DuoCircle. Product strategy and commercial lead for AutoSPF's 2,000+ customer base.
LinkedIn Profile →