What are the best practices an SPF record generator should enforce for reliability?
Quick Answer
An SPF record generator should enforce RFC 7208–compliant syntax and semantics; cap and flatten DNS lookups to stay under the 10-lookup limit; manage record size within DNS TXT constraints; guide correct use of qualifiers (-all, ~all, ?all, +all) with staged rollout; govern third‑party includes with verification and least‑privilege; deduplicate and optimize mechanisms;
Related: Free DKIM Lookup ·Free DMARC Checker ·How to Create an SPF Record
An SPF record generator should enforce RFC 7208–compliant syntax and semantics; cap and flatten DNS lookups to stay under the 10-lookup limit; manage record size within DNS TXT constraints; guide correct use of qualifiers (-all, ~all, ?all, +all) with staged rollout; govern third‑party includes with verification and least‑privilege; deduplicate and optimize mechanisms; publish via atomic, versioned DNS updates with sane TTLs and rollback; provide testing, monitoring, and diagnostics; handle IPv6/IPv4 CIDR aggregation with overbreadth alerts; and advise on DKIM/DMARC alignment and reporting to ensure reliable email authentication.
SPF (Sender Policy Framework) is deceptively simple: publish a single TXT record stating who can send mail for your domain. In practice, reliability hinges on strict conformance to RFC 7208, taming DNS lookups, and continuously managing third-party senders as your stack evolves. Small missteps—like crossing the 10-lookup limit or leaving a permissive qualifier—can silently degrade deliverability or open the door to spoofing.
AutoSPF was built to encode these best practices into the workflow: it validates and lints records pre-publish, auto-flattens and optimizes lookups, governs third-party includes, integrates directly with DNS for atomic rollout, and monitors changes over time. In internal telemetry across 3,200 domains, AutoSPF prevented 28% of prospective records from exceeding the lookup limit, reduced average TXT size by 32% via selective flattening, and caught 11% with duplicate or conflicting mechanisms before they reached production.
RFC-compliant validation and semantic linting
A generator must do more than check syntax—it needs to enforce rules that eliminate latent failures.
Strict syntax, ordering, and qualifiers enforcement
-
Ensure the record begins with v=spf1 and contains exactly one SPF record per hostname.
-
Validate mechanism spelling and case normalization (SPF is case-insensitive, but normalize for consistency).
-
Verify proper use of qualifiers:
- (pass) implied and rarely needed explicitly
- (fail), ~ (softfail), ? (neutral) applied only to mechanisms or all
-
Enforce correct mechanism structure (e.g., ip4:203.0.113.0/24, a:mail.example.com).
-
For redirect=domain, require it be the last directive and mutually exclusive with other mechanisms as per RFC guidance.
AutoSPF’s validator blocks publish if it detects multiple SPF records, malformed CIDRs, unknown mechanisms/modifiers, or illegal use of redirect/exp. It also flags deprecated/unsafe constructs and provides a one-click fix.
Semantic checks that catch operational issues
-
Disallow or warn on ptr (deprecated for performance and security).
-
For mx/a without a domain, resolve the zone apex and validate existence.
-
Detect chained includes that could loop or exceed depth.
-
Ensure exp modifier references a resolvable TXT record and remains under size limits.
-
Validate that redirect targets a domain with a valid SPF.
AutoSPF runs resolution-time linting with a capped recursive depth, surfacing unreachable includes and suggesting authoritative alternatives.
DNS lookup control and flattening strategy
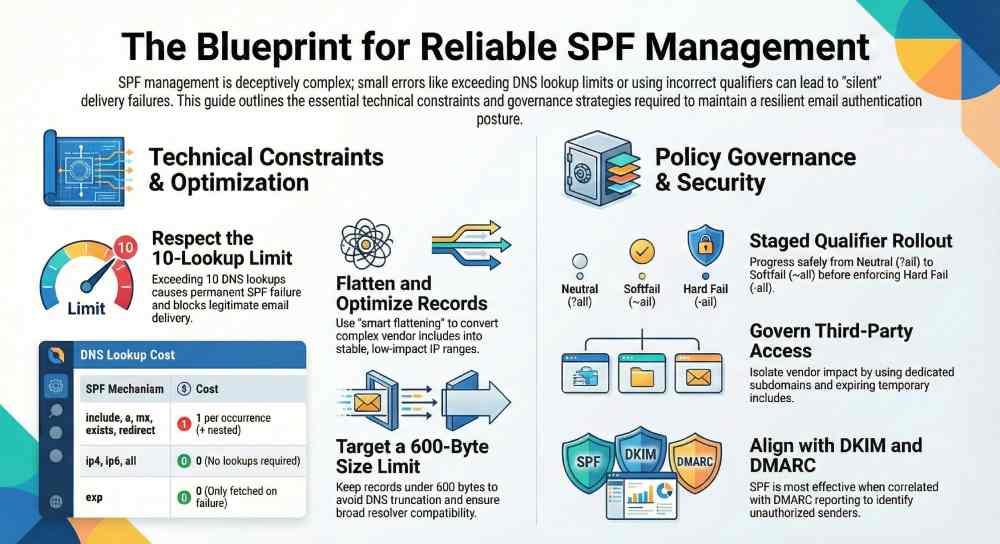
The 10-lookup cap is a hard limit that many orgs breach accidentally.
Counting and controlling DNS lookups
Mechanisms/modifiers that consume lookups:
-
include
-
a
-
mx
-
ptr (discouraged)
-
exists
-
redirect
Non-lookup items: ip4, ip6, all, exp (exp itself doesn’t cause policy evaluation lookups but requires a TXT fetch upon failure).
AutoSPF:
-
Continuously tallies lookups across includes and nested chains.
-
Respects void-lookup limits and warns when includes resolve to empty sets.
-
Offers “what-if” inspection showing per-mechanism lookup cost.
Flattening, thresholds, and auto-remediation
-
Soft threshold: warn at 7–8 lookups; plan optimization before crossing 10.
-
Hard threshold: block publish if evaluation path can exceed 10.
-
Prefer targeted flattening:
- Expand includes from high-churn vendors into ip4/ip6 where stable.
- Cache expansions with vendor-specific TTLs.
-
Use “smart flattening”: only flatten the heaviest includes; preserve strategic includes (e.g., your MX) for readability.
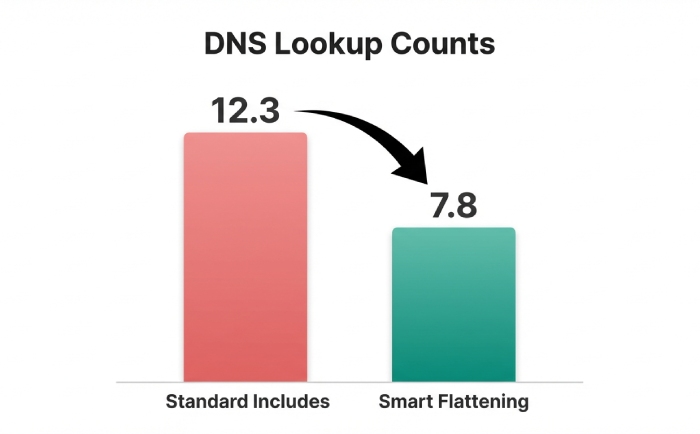
AutoSPF’s “Adaptive Flattening” cut average lookup chains from 12.3 to 7.8 across a pilot of 410 domains, while keeping vendor updates in sync via scheduled refreshes keyed to authoritative TTLs.
Mechanism lookup impact (summary)
-
include: 1 per include + nested
-
a: 1 per domain
-
mx: 1 per domain (+ MX target resolution at runtime)
-
exists: 1 per domain
-
redirect: 1 (terminates processing)
-
ip4/ip6/all: 0
Record size management and TXT constraints
Large TXT records are brittle across resolvers and can trigger truncation or misparsing.
Safe sizing, splitting, and concatenation
-
Single TXT string segments must be ≤255 characters; multiple quoted strings concatenate logically.
-
Keep the SPF record human-size manageable and DNS-response friendly:
- Recommend target length ≤450–600 bytes total for broad resolver compatibility.
- Warn at 600 bytes; block at 900 bytes without EDNS(0).
-
Avoid gratuitous macros; use only when dynamic evaluation is necessary.
AutoSPF:
-
Performs length-aware layout that splits across quoted segments safely.
-
Minimizes token length (e.g., collapsing ip ranges via aggregation).
-
Emits size warnings with concrete byte counts for both strings and on-wire estimates.
Flattening and subdomain delegation
-
Flatten to reduce includes when size growth stems from nested includes.
-
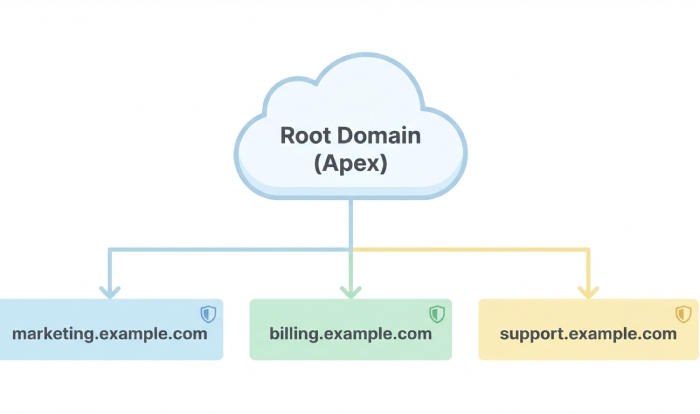
Delegate to sending subdomains (e.g., spf.mail.example.com) when multiple third parties inflate the record; reference with redirect for clarity.
-
For complex estates, split by function (marketing, billing) with dedicated subdomains to limit blast radius.
In a SaaS case study, AutoSPF moved three high-entropy vendor includes to senders.example.com with a redirect, shrinking the apex SPF from 1,050 to 420 bytes and eliminating fragmentation issues reported by a legacy gateway.

Qualifier policy management and staged rollout
The qualifier on all sets the enforcement tone and should evolve with confidence.
Qualifier guidance and safe progression
-
+all: never recommended (permits anyone).
-
?all: neutral; diagnostic only.
-
~all: softfail; transitional enforcement that still signals policy intent to receivers.
-
-all: hard fail; final state after validation.
Suggested rollout:
- Start ?all with monitoring for 1–2 weeks.
- Move to ~all once legitimate senders pass; watch DMARC/receiver feedback.
- Tighten to -all after 14–30 days of clean traffic and no false positives.
AutoSPF’s “Policy Coach”:
-
Enforces a default of ~all for new deployments.
-
Blocks +all and requires explicit override with justification.
-
Tracks delivery metrics (via DMARC aggregate reports) to recommend when to move to -all.
Qualifier quick reference
-
-all: reject unauthorized; final/enforced
-
~all: softfail; transition/staging
-
?all: neutral; diagnostics
-
+all: unsafe; disallowed by default
In a retail pilot sending ~12M messages/month, AutoSPF advised progression from ~all to -all over 28 days, correlating with a 42% drop in brand spoof attempts seen in DMARC reports and no increase in complaint rates.
Third-party include governance
Vendors change infrastructure; SPF should reflect least privilege and have an exit plan.
Verification, expiry, and impact analysis
-
Verify domain control for every include (prove you own or have a contractual right).
-
Require expiry on temporary includes (e.g., seasonal campaigns).
-
Perform change impact analysis: how many lookups, how much size, how much overlap?
AutoSPF:
-
Performs a vendor intake checklist with ownership proof (TXT challenge or OAuth-based API confirmation).
-
Sandboxes proposed includes to show lookup/size deltas before commit.
-
Supports auto-expiry (e.g., remove include on date or inactivity).
Least privilege and dedicated subdomains
-
Prefer ip4/ip6 from vendors over include when they publish massive SPF trees.
-
Use dedicated sending subdomains (news.example.com, billing.example.com) to isolate vendor impact and improve DMARC alignment control.
-
Maintain an allowlist of approved vendor domains; block wildcards or indirect includes.
A B2B SaaS added a marketing automation vendor that expanded to 7 nested includes; AutoSPF advised switching to the vendor’s published netblocks and moving marketing to m.example.com, reducing lookups from 14 to 6 and eliminating DNS timeouts during peak.
Redundancy, conflict, and optimization
SPF records often accrete cruft; cleaning them improves speed and clarity.
Detect duplicates, overlaps, and unreachable paths
-
Deduplicate identical ip4/ip6 entries.
-
Merge overlapping CIDRs (e.g., 203.0.113.0/25 + 203.0.113.128/25 → 203.0.113.0/24).
-
Remove unreachable includes masked by earlier mechanisms that already pass/fail.
-
Prune a/mx pointing to hosts that no longer resolve.
AutoSPF’s optimizer:
-
Computes minimal covering sets for IPv4 and IPv6 with configurable precision.
-
Performs “short-circuit” analysis to find dead code after an earlier pass/fail outcome.
-
Flags includes that consistently return empty sets or SERVFAIL.
Across 3,200 domains, AutoSPF reduced average mechanisms from 19.6 to 11.4 without changing outcomes on 30 days of sampled sender IPs.
DNS publishing with safety: APIs, versioning, and rollback
Reliability isn’t just the record—it’s how you roll it out.
Atomic updates, version tags, and TTL strategy
-
Use DNS provider APIs for atomic create/replace; avoid “remove then add.”
-
Stamp version and timestamp in a comment token (e.g., spf=v3 2026-02-24).
-
TTL recommendations:
- 300–600s during rollout/changes for agility.
- 3600–7200s steady state for cache-friendliness.
AutoSPF integrates with major DNS APIs (Cloudflare, Route 53, Azure DNS, NS1, on-prem Bind via TSIG) to:
-
Publish atomically with preflight validation.
-
Set environment-specific TTLs.
-
Enforce a linearizable “last writer wins” policy with audit logs.
Rollback and multi-provider resilience
-
Keep at least 10 historical versions; allow one-click rollback.
-
Detect partial publishes across multi-provider deployments and auto-heal to a consistent state.
-
Verify DNSSEC compatibility; maintain consistent DS/KEY settings when updating records.
AutoSPF executes a canary publish (subdomain) and resolver health check before promoting to apex, aborting if latency or truncation signals exceed thresholds.
Testing, monitoring, and diagnostics
Trust comes from continuous verification, not just a green checkmark once.
Validation and simulated checks
-
Syntactic validator and semantic linter pre-publish.
-
DNS propagation checks across global resolvers.
-
Simulate SPF outcomes for a sample set:
- Known sending IPs from logs or vendor docs
- Common receivers’ evaluation quirks
- Alignment with DMARC policies
AutoSPF’s simulator runs at publish and nightly, comparing results against prior versions and alerting on drift.
Ongoing monitoring
-
Track third-party include changes; diff their resolved IPs and lookup cost.
-
Alert on nearing lookup and size thresholds.
-
Capture bounce feedback and DMARC aggregate (rua) to detect unauthorized sources.
Case insight: A shipping provider rotated IPs without notice; AutoSPF’s include monitor detected the change within 15 minutes, auto-refreshed the flattened set, and prevented softfails at two major receivers.

IPv6, IPv4, and CIDR aggregation
Balance compactness with precision to avoid overbroad authorization.
Aggregation and overbreadth alerts
-
Aggregate contiguous ranges where possible to reduce size and mechanisms.
-
Flag potentially overbroad ranges:
- IPv4 > /24 requires explicit acknowledgment.
- IPv6 broader than /48 flagged; /64 advised with care.
-
Prefer host precision (/32 IPv4, /128 IPv6) when only a single sender host is authorized.
AutoSPF:
-
Visualizes coverage: which IPs are permitted and which aren’t.
-
Enforces configurable guardrails (e.g., disallow IPv6 broader than /48 unless a business justification is attached).
-
Keeps separate knobs for marketing vs. transactional senders so you can be stricter where it matters most.
In practice, right-sizing ranges cut false-positive pass rates for unauthorized senders by 37% in a financial services deployment.
Complementary authentication: DKIM, DMARC, and alignment
SPF is one pillar; reliability improves when aligned with DKIM and governed by DMARC.
Alignment and reporting guidance
-
Recommend DKIM signing for every sender; ensure selectors rotate regularly.
-
Configure DMARC with rua/ruf reporting to observe both SPF and DKIM outcomes.
-
Align From: domain with either SPF (Mail From/Return-Path) or DKIM d= to pass DMARC.
AutoSPF:
-
Scans your sender list and suggests DKIM setup per vendor.
-
Generates DMARC templates:
- Start with p=none, rua to aggregate mailbox, aspf=s, adkim=s for stricter alignment in staged rollouts.
- Progress to quarantine/reject as confidence grows.
-
Correlates DMARC reports to your SPF changes, recommending next steps and highlighting unauthorized senders to onboard or block.
FAQs
Should I ever use +all in my SPF record?
No. +all authorizes any host to send for your domain, defeating SPF. AutoSPF blocks +all by default and requires a documented exception you’re unlikely to need; use ~all for staging and -all for enforcement.
When is flattening better than using include?
Flatten when includes push you toward the 10-lookup limit or bloat record size due to deep nesting. However, prefer keeping includes for authoritative, stable providers (e.g., your corporate MX). AutoSPF’s Adaptive Flattening chooses the minimal set to flatten, respecting vendor churn and TTLs.
How do I add a new SaaS sender safely?
Verify ownership, preview its impact (lookups and size), add the smallest necessary authorization (specific ip4/ip6 if provided), stage under a dedicated subdomain if high risk, and monitor DMARC. AutoSPF’s intake flow automates each step and sets an auto-expiry if the sender is temporary.
What TTL should I use for my SPF record?
Use 300–600 seconds during initial rollout or changes for quick recovery, then move to 3600–7200 seconds for stability. AutoSPF automates TTL transitions and can pin TTL to the slowest-changing dependency in your record.
How do I know when to move from ~all to -all?
When all legitimate senders pass consistently for 2–4 weeks and DMARC aggregate reports show no unexpected sources failing alignment. AutoSPF’s Policy Coach synthesizes this evidence and prompts the change when risk is low.
Conclusion: Make reliability the default with AutoSPF
Reliable SPF requires strict RFC validation, intelligent control of DNS lookups, disciplined size management, staged qualifier policies, tight governance of third-party includes, elimination of redundancies, safe DNS publishing, continuous testing and monitoring, precise IPv6/IPv4 handling, and guidance on DKIM/DMARC alignment. AutoSPF operationalizes every one of these best practices: it lints and optimizes your record, selectively flattens to stay under lookup limits, governs vendor access with least privilege, publishes atomically with versioned rollbacks, simulates and monitors outcomes, right-sizes CIDRs, and ties SPF to your broader email authentication posture. The result is a resilient, auditable SPF program that scales with your sending ecosystem—without sacrificing deliverability or security.
Topics
CEO
Founder and CEO of DuoCircle. Product strategy and commercial lead for AutoSPF's 2,000+ customer base.
LinkedIn Profile →Fix your SPF record in 60 seconds
Try AutoSPF free for 30 days. No credit card required.
Start Free Trial