RFC stands for Request for Comments, a series of documents used by the Internet community to publish technical guidelines, protocols, and standards that keep the Internet functioning consistently. These documents describe how different systems should behave so that technologies developed by different vendors can work together reliably.
Over time, some RFCs become official Internet standards because they are widely adopted and proven to work well. Many technologies that people rely on every day, such as email, web communication, and internet routing, are based on RFC specifications.
By documenting these technologies clearly and openly, RFCs help ensure that internet systems remain compatible, secure, and stable across different platforms and service providers.
What is RFC 7208
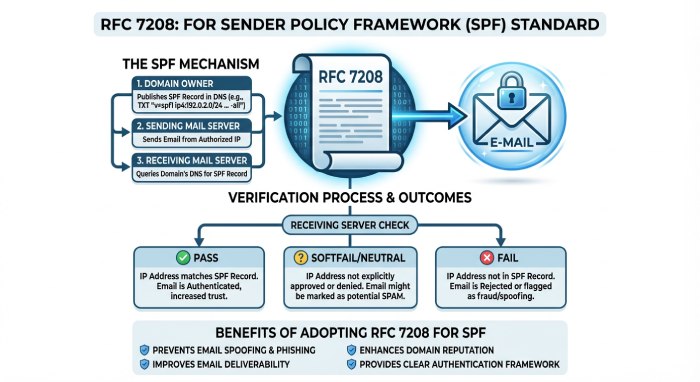
RFC 7208 is the official Internet standard that explains how the Sender Policy Framework (SPF) works for email authentication. It was published by the Internet Engineering Task Force (IETF) and describes how domain owners can specify which mail servers are allowed to send emails from their domain. The document focuses entirely on SPF, an email authentication method that helps receiving mail servers check whether an email is coming from an authorized sender. It explains how SPF records are added to a domain’s DNS, how receiving mail servers look up those records, and how they evaluate them when an email arrives.
In simple terms, RFC 7208 provides clear instructions on how SPF should be implemented and interpreted. Because of this standard, email providers and security tools follow the same rules when checking SPF records.
This consistency is important. It helps email systems accurately verify senders and detect messages sent from unauthorized sources. As a result, RFC 7208 plays an important role in preventing domain spoofing and improving overall email security.
RFC 7208 and the standardization of SPF
SPF existed before RFC 7208, but in the early days, it was not a fully standardized protocol. It started as a community effort to reduce email spoofing, and different email providers implemented it in slightly different ways. This sometimes led to confusion or inconsistent results when mail servers checked SPF records.
RFC 7208 helped solve this problem by clearly documenting how SPF should work. Published by IETF, the RFC provides detailed guidelines on how SPF records should be written and how they should be evaluated when an email is received.
The document explains how domain owners can list authorized sending sources in DNS and how receiving mail servers should check these records during the authentication process. It also introduces certain rules, such as limits on DNS lookups, to prevent performance issues and reduce the risk of misuse.
RFC 7208 also standardizes how SPF results are reported. When a mail server checks an SPF record, the result can be pass, fail, softfail, or neutral, depending on whether the sender is authorized.
By defining these rules, RFC 7208 made SPF more reliable and consistent across email systems. This helped transform SPF from an informal anti-spoofing technique into a recognized internet standard used worldwide for email authentication.
How SPF works according to RFC 7208
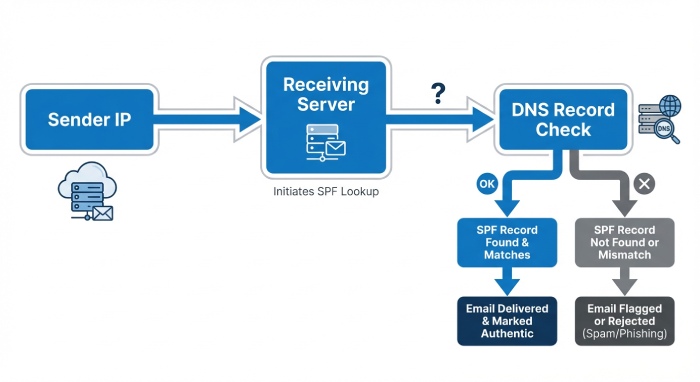
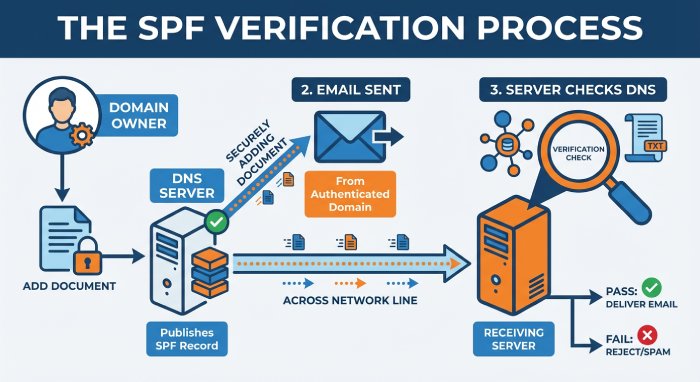
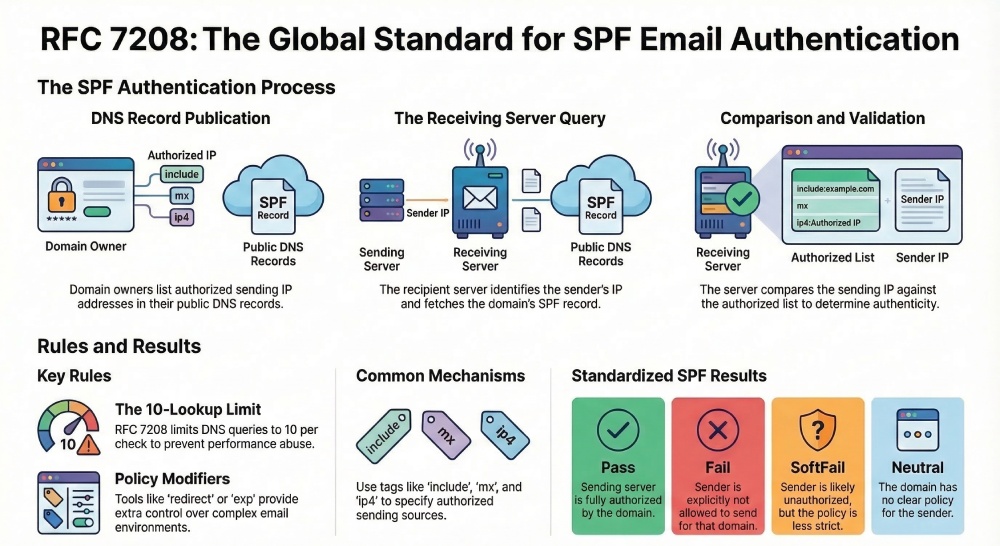
Every time an email is sent, the receiving server quietly performs a few background checks before deciding whether the message should be trusted. One of these checks is SPF. RFC 7208 explains exactly how this verification process should happen so that different email systems evaluate SPF in the same way.
Publishing SPF records in DNS
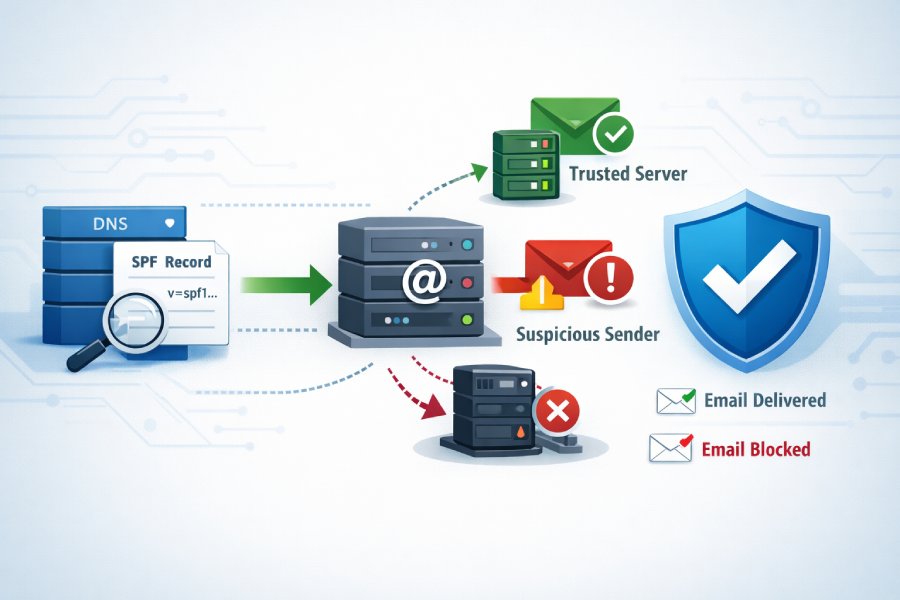
The SPF process starts with the domain owner. To use SPF, a domain publishes an SPF record in its Domain Name System (DNS). This record is essentially a list of servers that are allowed to send emails on behalf of the domain. When the record is published, it acts like a public reference that receiving mail servers can check whenever an email claiming to come from that domain arrives.
How receiving mail servers perform SPF checks
When an email reaches a receiving mail server, the server first looks at the sending IP address of the message. It then identifies the domain used in the email’s return-path (also called the envelope sender).
Next, the server queries the DNS to find the SPF record for that domain. The sending IP address is compared with the list of authorized servers mentioned in the record. If the IP address appears in the record, the message is considered to come from an approved source. If it does not match, the email may be treated as suspicious.
SPF authentication results explained (Pass, Fail, SoftFail, Neutral)
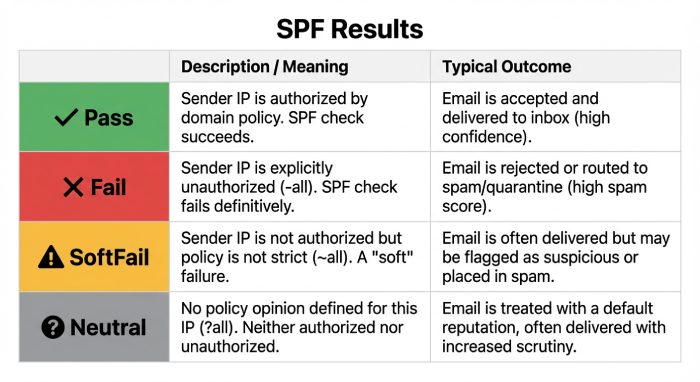
After evaluating the SPF record, the receiving server assigns an SPF result.
- A Pass means the sending server is authorized by the domain.
- A Fail means the sender is not allowed to send emails for that domain.
- A SoftFail indicates the sender is probably not authorized but the policy is less strict.
- A Neutral result means the domain has not clearly stated whether the sender should be trusted.
These results help receiving systems decide how to handle the message, such as accepting it, flagging it, or applying additional spam checks.
Key mechanisms and tags defined in RFC 7208
Understanding the mechanisms and modifiers makes it easier to see how SPF decides whether a sender is authorized or not.
Common SPF mechanisms
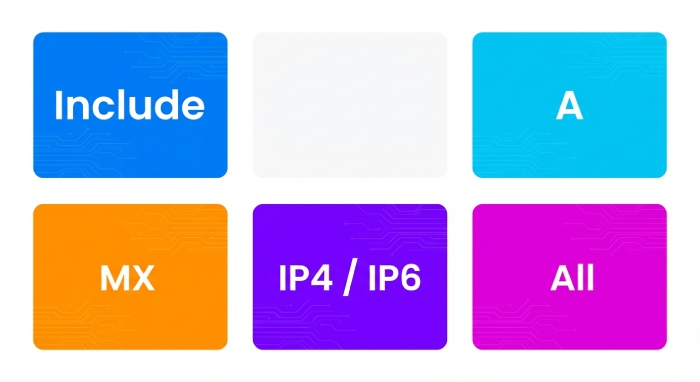
SPF records rely on several mechanisms that specify which sources are allowed to send emails for a domain.
- The ‘include’ mechanism allows a domain to authorize another domain’s SPF record. This is commonly used when companies rely on third-party email services.
- The ‘a’ mechanism allows the IP address linked to the domain’s A record to send emails. If the sending server matches that IP address, the SPF check can pass.
- The ‘mx’ mechanism authorizes the mail servers listed in the domain’s MX records. Since MX records already define the domain’s mail servers, this mechanism lets them send emails as well.
- The ‘ip4’ and ‘ip6’ mechanisms allow specific IPv4 or IPv6 addresses to send emails for the domain. These are useful when organizations want to directly allow certain servers.
- The ‘all’ mechanism acts as the final rule in the SPF record. It tells receiving servers how to treat senders that do not match any previous rule.
SPF modifiers and policy control
In addition to mechanisms, SPF records can contain modifiers that provide extra instructions. Modifiers help control how the SPF record behaves and how results are reported.
- The ‘redirect’ modifier: It tells the receiving server to check another domain’s SPF record instead. This is useful when multiple domains use the same email infrastructure.
- The ‘exp’ modifier: It provides an explanation message when an SPF check fails. This message can help administrators understand why the email was rejected.
These modifiers allow domain owners to manage SPF policies more clearly and maintain flexibility in complex email environments.
The SPF lookup limit and why it matters

RFC 7208 also introduces an important technical rule called the DNS lookup limit. During an SPF check, the receiving server may need to perform DNS queries to evaluate mechanisms like include, a, or mx.
To prevent excessive DNS queries and potential abuse, SPF limits the number of lookups to 10 per evaluation. If this limit is exceeded, the SPF check may fail.
Because of this rule, organizations must carefully design their SPF records. Using too many includes or mechanisms can quickly reach the lookup limit and cause authentication issues. Keeping SPF records simple and efficient helps ensure reliable email authentication.
Limitations of SPF and why DMARC completes the framework
SPF is an important step in verifying where an email comes from, but it does not solve every email security problem on its own. While SPF can check whether a sending server is authorized, it does not always guarantee that the message truly represents the domain shown to the recipient. Because of these gaps, additional authentication layers are needed to make email verification stronger and more reliable.
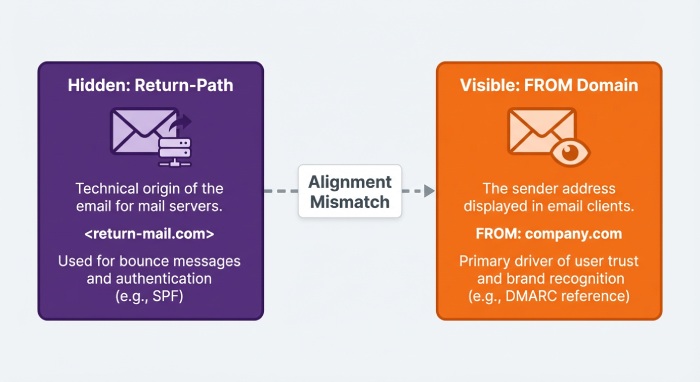
The SPF alignment problem
One major limitation of SPF is something called the alignment problem. SPF checks the domain used in the Return-Path or envelope sender address, which is often hidden from the recipient. However, the email address that people actually see in their inbox is the From address.
These two domains do not always have to match. In some cases, an attacker can send an email from an authorized server but display a different domain in the visible From address. The SPF check may still pass because the sending server is technically allowed to send mail for the return-path domain. This creates a gap where a message can pass SPF but still mislead the recipient about who actually sent it.
Forwarding and SPF failures
Another challenge appears when emails are forwarded. When a message is forwarded, the original sending server stays the same, but the email is resent through another mail server.
Because SPF checks the sending server’s IP address against the original domain’s SPF record, forwarding can break the authentication process. The forwarding server’s IP address is usually not listed in the original domain’s SPF record. As a result, the SPF check may fail even though the email is legitimate.
How DMARC builds on SPF and DKIM
To address these issues, organizations use DMARC, which stands for Domain-based Message Authentication, Reporting, and Conformance. DMARC works together with SPF and DKIM to provide stronger verification.
One of the key improvements DMARC introduces is domain alignment. It checks whether the domain used in authentication matches the domain shown in the From address that users see. This helps prevent attackers from passing authentication while impersonating another domain.
DMARC also allows domain owners to publish policies that tell receiving servers what to do when authentication fails. For example, a message can be monitored, quarantined, or rejected. In addition, DMARC provides reporting features that help organizations see how their domains are being used in email traffic. By combining SPF, DKIM, and alignment checks, DMARC creates a more complete system for protecting domains from spoofing and impersonation.
Final thoughts
Email authentication may seem like a purely technical topic, but standards such as RFC 7208 show how much coordination is required to keep something as common as email trustworthy. Every message that travels across the internet passes through many independent systems, and each must interpret the authentication checks consistently. Without shared standards, even well-configured security controls could produce inconsistent results.
RFC documents like 7208 quietly form the foundation that allows this cooperation to happen. They give engineers, email providers, and security teams a common reference point for building and maintaining reliable systems. As email threats continue to evolve, the importance of clear, well-defined standards becomes even greater.
Understanding these standards is not only useful for security professionals. It also helps organizations better manage their domains, improve deliverability, and build stronger trust in their email communications.