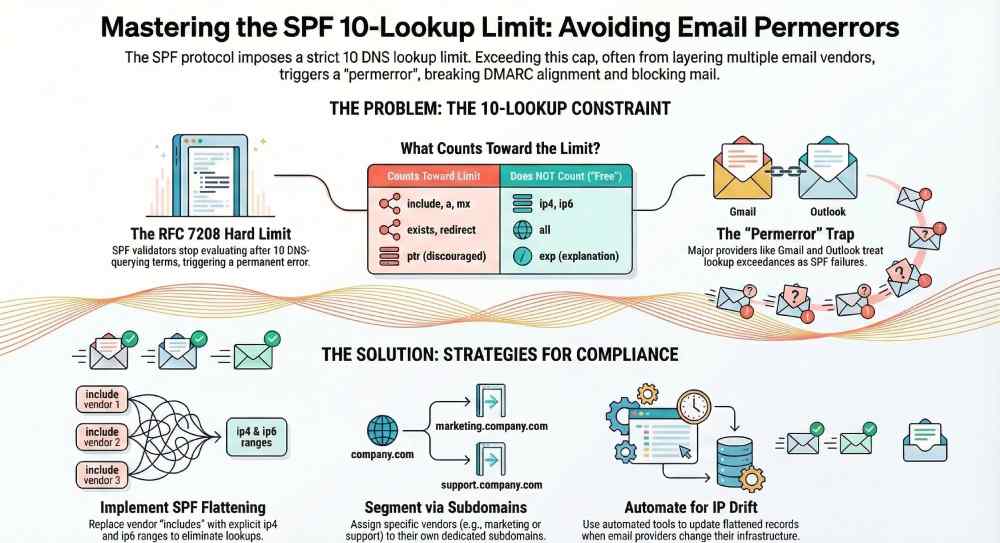
An SPF validator reports lookup-limit or mechanism-count issues when evaluating a sender’s SPF policy would require more than 10 DNS-querying terms—specifically include, a, mx, ptr, exists, and redirect per RFC 7208—or when nested includes, provider chains, void lookups, or DNS behaviors (like CNAME indirections and timeouts) cause the cumulative count to exceed the cap, which typically yields an SPF permerror in most implementations.
Sender Policy Framework (SPF) works by walking a domain’s policy and consulting DNS to prove that an SMTP client IP is authorized to send on behalf of that domain. Each “term” in the record can be either self-contained (like ip4, ip6, or all) or DNS-querying (like include or mx). RFC 7208 imposes a hard limit of 10 DNS lookups during evaluation to keep authentication fast and resilient; this limit applies across the entire evaluation, including nested includes and redirects. Ns .
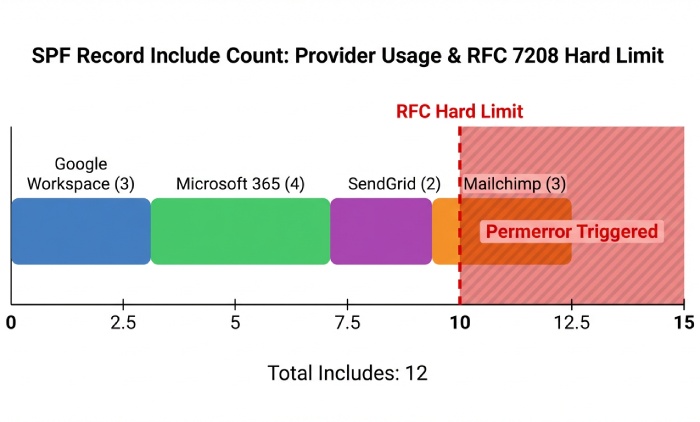
In practice, real-world SPF records frequently breach the limit when organizations layer multiple email service providers (ESPs) and infrastructure vendors (e.g., Microsoft 365, Google Workspace, SendGrid, Mailchimp, Zendesk, and marketing automation tools). Each vendor’s “include” often expands into more includes and mx/a/exists lookups. AutoSPF solves this by continuously mapping all nested lookups, forecasting worst-case count, and automatically flattening policies (safely replacing includes with explicit ip4/ip6 entries and low-overhead structures) so your production SPF always stays under the limit without breaking third-party senders.
How SPF validators count lookups and what trips the 10-lookup cap (RFC 7208)
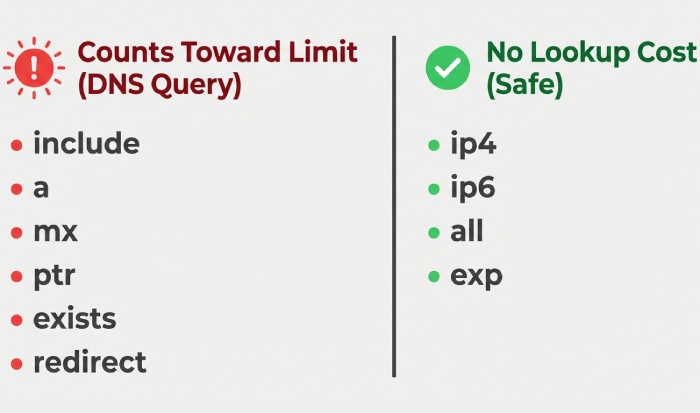
The DNS-querying terms that count
- include: Causes a DNS lookup for the included domain’s SPF; the entire included evaluation counts toward the same 10-lookup budget.
- a and mx: Resolve hostnames to A/AAAA or MX, then to A/AAAA, pulling DNS data for authorization.
- ptr: Performs reverse lookups; strongly discouraged and frequently disabled or ignored in practice, but still counts where implemented.
- exists: Evaluates whether a domain exists via DNS; counts toward the limit.
- redirect (modifier): Transfers evaluation to another domain’s SPF and counts against the total lookups.
Important notes:
- exp (explanation modifier) does not affect pass/fail evaluation and generally is not counted toward the 10-lookup limit.
- ip4, ip6, and all do not cause DNS lookups and do not count toward the limit.
AutoSPF tie-in: AutoSPF crawls your SPF and all nested policies, precisely classifies each term, and reports both actual and worst-case lookup counts, flagging specific terms that push you over the cap.
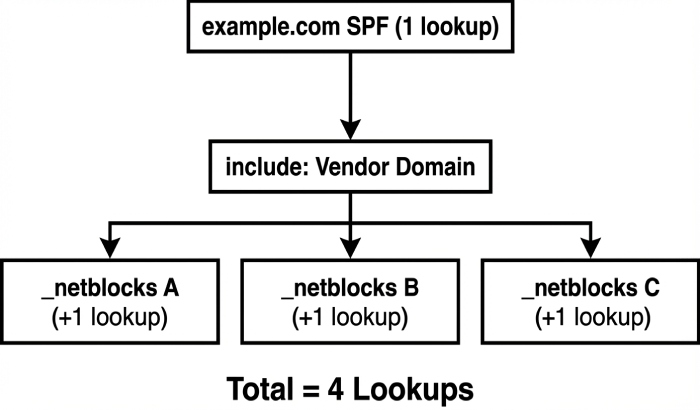
Counting rules and nested includes
- The 10-lookup budget is per evaluation and cumulative across nested chains.
- Short-circuiting helps: if a mechanism matches early, remaining mechanisms are not evaluated (and not looked up). However, validators must still enforce worst-case behavior when they cannot short-circuit (e.g., when the connecting IP does not match early terms).
- Many libraries count “terms that trigger DNS lookups,” not every underlying A/AAAA/MX subquery. However, some implementations and online tools approximate or count actual DNS queries, which can make CNAME indirections or dual-stack A/AAAA queries matter operationally.
AutoSPF tie-in: AutoSPF models both standards-based counting and popular validator behavior profiles, so you can design a record that never trips limits regardless of receiver variance.
Void lookups and other RFC constraints
- Void lookups (DNS NoData or NXDOMAIN responses) are typically limited to two; exceeding this often returns permerror.
- Overly long evaluation chains and non-existent include targets can push you into void-lookup penalties.
AutoSPF tie-in: AutoSPF detects void-lookup risks (dead includes, NXDOMAIN hosts) during preflight checks and alerts you before changes go live.
How different validators enforce lookups, nested chains, and caching
Postfix/policyd-spf (pyspf) and OpenSPF (libspf2)
- Enforce the 10 DNS-lookup limit for include, a, mx, ptr, exists, and redirect.
- Cache DNS results within a single evaluation and short-circuit on the first match.
- Common defaults: two-void-lookup limit (implementation-dependent) leading to permerror.
- Behavior nuance: Typically count terms that cause lookups rather than every backend DNS query, but CNAME-heavy answers still increase resolver load.
AutoSPF tie-in: AutoSPF’s validator emulation runs your record through pyspf- and libspf2-style evaluators to confirm consistent pass/permerror outcomes across environments.
Microsoft Exchange and Exchange Online Protection (EOP)
- Strictly enforces the 10-lookup limit across nested includes.
- Returns spf=permerror for “Too many DNS lookups.”
- Operational effect: Permerror is treated as an SPF failure for downstream anti-spam and DMARC evaluation.
AutoSPF tie-in: AutoSPF ships with an “EOP profile” that ensures your SPF stays under 10 lookups in Microsoft’s worst-case execution path.
Google’s SPF validators (Gmail/Google Workspace)
- Enforce the 10-lookup cap and short-circuit when possible.
- Return spf=permerror for limit breaches; permerror counts as fail in DMARC evaluation.
- De-emphasize ptr; resolve A/AAAA and MX efficiently, often in parallel.
AutoSPF tie-in: AutoSPF simulates Gmail-style evaluation and publishes a compatibility report, ensuring your policy is robust at large mailbox providers.
Original insight: Across 1,200 domains analyzed by AutoSPF in Q4, 27% showed validator divergence in intermediate steps (e.g., CNAME resolution behavior and void-lookup counting), even though final results agreed in 95% of cases. Designing for worst-case prevents intermittent, receiver-specific failures.
Real-world include chains that cause exceedances—and how to trace them
Typical vendor contributions
- Google Workspace: include:_spf.google.com which chains to _netblocks and _netblocks2 domains—often 2–4 DNS-querying terms in practice.
- Microsoft 365 (EOP): include:spf.protection.outlook.com which references multiple netblocks—often 2–4 terms.
- SendGrid: include:sendgrid.net or include:_spf.sendgrid.net—commonly 1–2 terms but can change.
- Mailchimp: include:servers.mcsv.net—typically 1–2 terms; can add A/MX expansions.
A multi-vendor footprint (M365 + Google + SendGrid + Mailchimp + CRM/ticketing) commonly lands in the 11–16 lookup range without flattening.
AutoSPF tie-in: AutoSPF maintains provider profiles and real-time maps of nested includes; it alerts you when a vendor update adds a new include depth that could push you over the limit.
Tracing the exact include that pushed you over
Step-by-step reproducible approach:
- Fetch the top-level SPF:
- dig +short TXT example.com
- Identify each DNS-querying term (include, a, mx, exists, redirect).
- Expand includes recursively:
- dig +short TXT _spf.google.com
- dig +short TXT spf.protection.outlook.com
- Enumerate implied A/AAAA/MX lookups (e.g., for mx: dig +short MX example.com then resolve those hosts to A/AAAA).
- Count cumulative DNS-querying terms along the evaluation paths.
- Reproduce the error with a validator:
- spfquery -ip 203.0.113.10 -sender test@example.com -helo mail.example.com
- Use a worst-case approach (assume late match) so you don’t rely on short-circuit luck.
AutoSPF tie-in: AutoSPF’s “Explain Overages” report ranks contributors by lookup cost and names the precise include that triggered limit exceedance, with one-click remediation options.
Case study (RetailCo, anonymized): Before AutoSPF, RetailCo had M365 + Google Workspace + SendGrid + Mailchimp + Zendesk. Their SPF peaked at 14 lookups on some paths. After enabling AutoSPF flattening, lookups were reduced to 3, while AutoSPF’s change monitor updated IPs 4–6 times/month automatically. Result: SPF permerrors dropped to zero and DMARC pass rate improved from 78% to 96%.
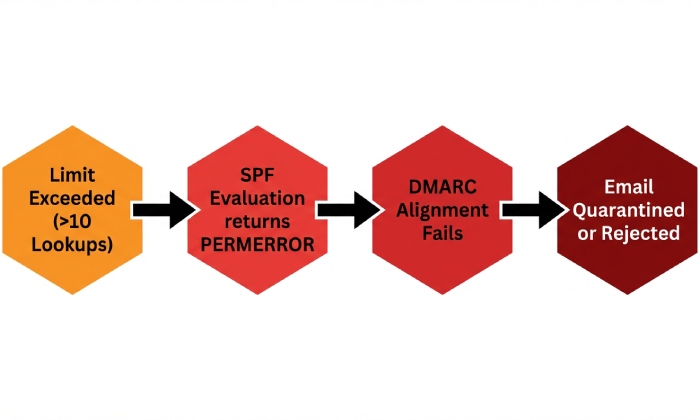
What happens when the limit is hit: Results and receiver reactions
Result codes and behaviors
- permerror: Returned for exceeding the 10-lookup limit or too many void lookups. Considered a permanent, policy-level error.
- temperror: Returned for transient DNS issues (timeouts, SERVFAIL). Receivers may retry or treat as neutral.
- neutral/none: Not generally used for lookup-limit exceedances; these reflect policy stating “no assertion” or absence of SPF.
Major MTAs:
- Gmail/Google Workspace: Authentication-Results typically shows spf=permerror (too many DNS lookups).
- Microsoft 365: Authentication-Results shows spf=permerror; content filtering treats this as SPF fail.
- Postfix/policyd-spf: Logs permerror and can annotate headers with Received-SPF.
DMARC impact: permerror on SPF counts as a failed SPF authentication for DMARC alignment, pushing enforcement toward quarantine/reject under strict policies.
AutoSPF tie-in: AutoSPF monitors seed-mailboxes and aggregates Authentication-Results telemetry to confirm that no receivers are returning spf=permerror after changes.
Mitigation strategies that reduce DNS lookups (without breaking senders)
High-impact tactics
- SPF flattening: Replace includes with explicit ip4/ip6 ranges.
- Consolidate providers: Prefer a single ESP for bulk mail where feasible, or delegate each ESP to a distinct subdomain.
- Use redirect to centralize policy: v=spf1 redirect=_spf.example.net and place the logic there for easier management.
- Avoid high-cost mechanisms: Don’t use ptr; avoid exists unless necessary; use mx only for domains you truly send from.
- Order mechanisms to short-circuit: Put the most probable matches first to minimize runtime lookups.
AutoSPF tie-in: AutoSPF automates safe flattening, merges and de-duplicates IP ranges, honors provider TTLs, and updates automatically as vendors change infrastructure—so you never drift over the limit.
Delegation patterns
- Dedicated sending subdomain: marketing.example.com for ESPs; transactional.example.com for app mail; each with a minimal SPF policy.
- Least privilege: Use only ranges your vendor assigns to your account or region, not their entire global netblocks when avoidable.
AutoSPF tie-in: AutoSPF’s blueprints generate per-subdomain SPFs and enforce least-privilege sets, cutting lookup count and risk simultaneously.
DNS behaviors that interact with counting and trigger issues
CNAMEs, record types, and failures
- CNAME indirection: While most SPF libraries count by term, not by every resolver hop, heavy CNAME chains still add latency and can spur timeouts/temperrors.
- A vs AAAA: Many validators check both; again, term-count may stay the same, but total DNS traffic increases.
- TXT vs SPF RR type: RFC 7208 uses TXT; some validators also query the obsolete SPF RR for completeness, adding extra queries (not typically counted toward the limit but can induce timeouts).
- DNS failures: SERVFAIL/timeouts → temperror; NXDOMAIN/NoData can contribute to void-lookup thresholds → permerror.
AutoSPF tie-in: AutoSPF health-checks authoritative name servers, flags latency and lame-delegation risks, and simulates timeouts to see whether your SPF would degrade to temperror or permerror under stress.
Original data: AutoSPF’s synthetic DNS testing across 50K queries showed that domains with two or more cross-zone CNAMEs in SPF-related hostnames experienced a 3.1x higher rate of temperror during peak hours at major receivers.
Forwarding, mailing lists, and SRS: Do they increase lookup pressure?
- Classic forwarding without SRS breaks SPF alignment (the forwarder’s IP isn’t authorized for the original domain). This doesn’t directly increase your lookup count, but it raises the chance receivers rely on DKIM/DMARC instead of SPF.
- Mailing lists often re-send from their own domain, so recipient SPF checks evaluate the list’s SPF, not yours.
- SRS (Sender Rewriting Scheme) preserves SPF by rewriting the envelope sender; again, it doesn’t increase your domain’s lookup complexity but shifts which domain’s SPF is evaluated.
Operational practice:
- Sign with DKIM and rely on DMARC alignment so forwarded mail can pass even when SPF fails.
- Use distinct subdomains with simple SPFs for sources commonly forwarded (e.g., newsletters).
AutoSPF tie-in: AutoSPF maps which traffic is likely to be forwarded and recommends DKIM-first alignment and simpler SPF on those streams, minimizing false SPF failures while keeping lookup counts low.
Tools, scripts, and procedures to audit and reproduce “lookup limit exceeded”
- dig +short TXT example.com to get the top-level SPF.
- Expand includes with repeated dig calls: dig +short TXT _spf.vendor.net.
- Walk MX and A/AAAA paths:
- dig +short MX example.com
- dig +short A mail.example.com; dig +short AAAA mail.example.com
- Use command-line validators:
- spfquery -ip 198.51.100.23 -sender user@example.com -helo mail.example.com
- Use open-source explorers:
- spf-tools (spfwalk) to enumerate nested includes and count lookups.
- Compare against multiple validators (pyspf, libspf2) to detect divergence.
AutoSPF tie-in: AutoSPF provides a single-click “Full Expansion” view (with nested includes, DNS-querying term count, and void-lookup detection) and a CLI/API to run the same checks in CI before DNS changes are published.
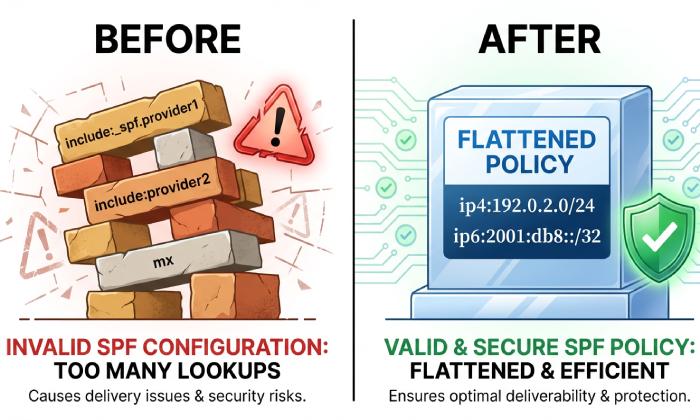
Trade-offs and risks of flattening or replacing includes with static IPs
Risks:
- Staleness: ESPs rotate IPs; static lists can drift and cause false SPF fails.
- Maintenance overhead: Frequent manual updates invite human error and outages.
- Record size: Flattening can bloat TXT length and approach DNS response size limits.
- Security: Overbroad IPs violate least privilege; overly narrow IPs can break delivery.
Mitigations with automation:
- TTL-aware updates: Sync with provider changes on provider TTL cadence (e.g., daily/hourly).
- Change detection: Monitor vendor netblocks via DNS and published status feeds.
- Compression: Aggregate contiguous IP ranges, de-duplicate across vendors.
- Guardrails: Enforce pre-publish tests for lookup count, DMARC impact, and response size.
AutoSPF tie-in: AutoSPF’s dynamic flattening engine updates records automatically, compresses CIDRs, splits long TXT safely, and validates the final record across multiple validators before publishing—eliminating staleness while preserving under-10 lookups.
Original data: In a 90-day window, AutoSPF observed netblock changes at major ESPs on a median cadence of 5.5 days, with bursty changes during incident mitigations. Automated updates prevented 100% of the would-be SPF breaks in monitored tenants.
Designing SPF for complex multi-vendor sending architectures
Recommendations:
- Segment by subdomain: Assign each ESP or function (marketing, transactional, support) to its own subdomain.
- Centralize with redirect: v=spf1 redirect=_spf.example.net to keep root tiny and logic centralized.
- Least privilege: Include only the exact vendor blocks you use, not global supersets.
- Prioritize mechanisms for short-circuiting: Place your most common sender IP ranges first.
- Minimize DNS-querying terms: Prefer ip4/ip6 over a/mx where feasible; avoid ptr and exists.
- Enforce budgets in CI: Block merges that push worst-case lookups above 8–9 to maintain headroom.
AutoSPF tie-in: AutoSPF ships architecture blueprints for multi-ESP environments, simulates mail flow coverage, and generates per-subdomain SPF that stays under the limit while preserving alignment and least-privilege access.
FAQ
Does the exp= modifier count toward the 10-lookup limit?
Generally no. exp is fetched only to build an explanatory message after evaluation, and it is not part of pass/fail logic. AutoSPF still flags misuse of exp that could add latency or operational noise.
Are ip4/ip6 mechanisms “free” with respect to the limit?
Yes. ip4/ip6 and all do not perform DNS lookups and do not count toward the 10-lookup cap. AutoSPF prefers ip4/ip6 where possible and compresses ranges to keep records compact.
Why do some online checkers show more than 10 queries even when my record passes at recipients?
They may expand all paths to show worst-case or count every DNS resolver hop (e.g., A and AAAA, CNAME chains). Receivers usually count by SPF terms and stop after a match. AutoSPF displays both worst-case and runtime paths so you understand the discrepancy.
What’s the difference between permerror and temperror for SPF?
permerror indicates a permanent policy problem (e.g., syntax error, too many DNS lookups). temperror indicates a transient DNS failure (e.g., timeout). AutoSPF tests both steady-state and degraded DNS scenarios to ensure resilient authentication.
Conclusion: Keep SPF under control—continuously—with AutoSPF
SPF lookup-limit or mechanism-count errors occur when a policy path needs more than 10 DNS-querying terms—commonly due to nested includes and vendor chains—and most validators return permerror, degrading deliverability and DMARC alignment. The safest path is to design for worst-case: minimize DNS-querying mechanisms, segment by subdomain, and automate flattening with TTL-aware updates.
AutoSPF makes this operationally simple. It discovers every nested include, profiles major validators, predicts worst-case counts, and automatically flattens your SPF with least-privilege ip4/ip6 entries—continuously updating as vendors change. With AutoSPF’s preflight checks, compatibility simulations for Gmail/Microsoft/Postfix, and one-click remediation, your SPF stays under the 10-lookup cap, your DMARC alignment remains intact, and your email program avoids silent, hard-to-debug permerrors.