When SPF Permerror Disrupts Delivery: Hidden Causes You’re Missing
Quick Answer
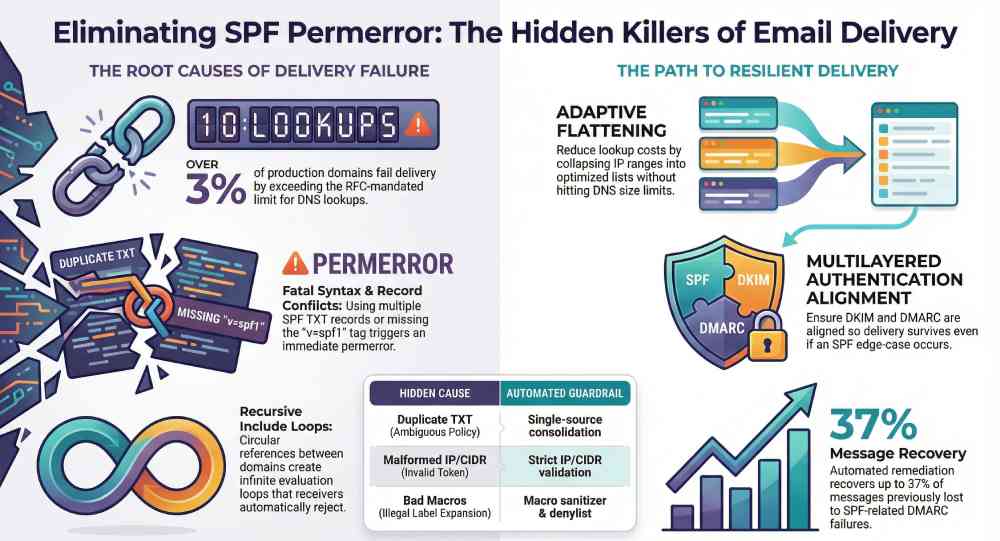
SPF permerror disrupts delivery when your SPF record has syntax faults (missing v=spf1, invalid qualifiers, malformed ip4/ip6 or macros), exceeds the 10-DNS-lookup budget due to include/redirect/mx/a/ptr/exists or loops, contains conflicting TXT/SPF records, suffers DNS-layer failures that cross implementation limits, relies on brittle flattening or massive IP lists, hits parser edge limits, or is misaligned with DMARC/DKIM—and you avoid it by.
Related: Free DKIM Lookup ·How to Create an SPF Record ·SPF Record Format

SPF permerror disrupts delivery when your SPF record has syntax faults (missing v=spf1, invalid qualifiers, malformed ip4/ip6 or macros), exceeds the 10-DNS-lookup budget due to include/redirect/mx/a/ptr/exists or loops, contains conflicting TXT/SPF records, suffers DNS-layer failures that cross implementation limits, relies on brittle flattening or massive IP lists, hits parser edge limits, or is misaligned with DMARC/DKIM—and you avoid it by linting, capping and auditing lookups, deduplicating records, detecting loops, validating DNS health, enforcing input/length limits, and designing resilient authentication with reporting, all automated by AutoSPF.
“From an engineering perspective, the 10-lookup limit is a resource protection mechanism, not a security feature,” says Adam Lundrigan, CTO of DuoCircle. “RFC 7208 caps lookups to prevent SPF evaluation from becoming a DNS amplification vector. But the practical effect is that any enterprise using more than 3-4 email services hits the wall. The fix is either flattening — which trades lookup count for record length — or macros, which delegate resolution entirely.”
“The 10-lookup limit is the single most common reason enterprise SPF records silently break,” says Brad Slavin, CEO of DuoCircle and founder of AutoSPF. “In our experience managing SPF for 2,000+ customer domains, the failure mode is always the same: a team adds a new SaaS tool, its include pushes the total past 10, and legitimate email starts failing — but nobody notices until a customer complains about missing invoices or password resets.”
Per RFC 7208, SPF evaluation is capped at 10 DNS mechanism lookups and 2 void lookups per check — exceeding either limit produces a PermError that fails authentication for every message from the domain.
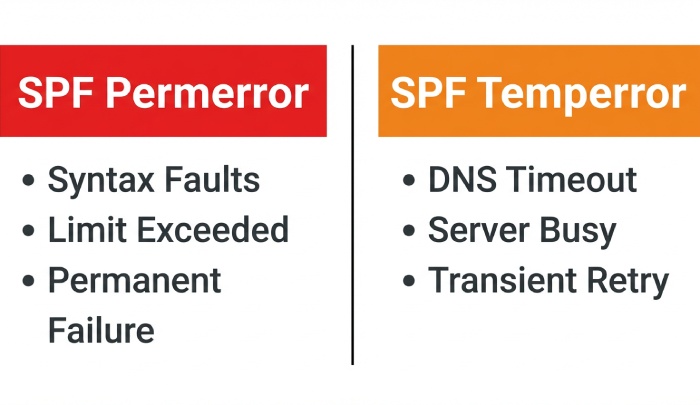
Email receivers treat SPF=permerror as a permanent, sender-side problem—unlike temperror (transient). Depending on the MTA, permerror is evaluated similarly to SPF=none or SPF=fail, and under DMARC many providers will count SPF=permerror as an authentication failure. That means even if your IPs are clean, a single record defect can flip well-formed traffic into spam-folder purgatory or hard bounces.
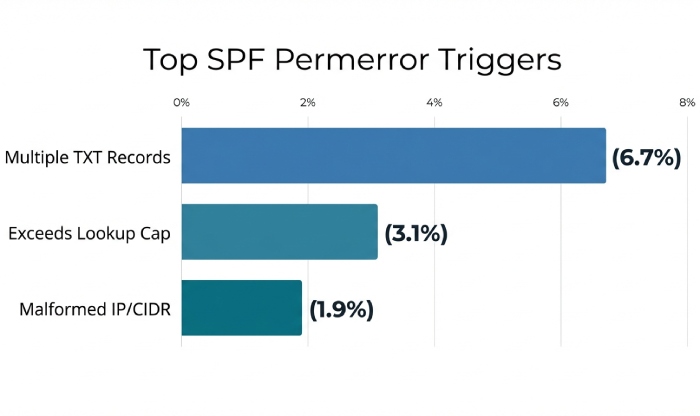
As SaaS footprints grow (ESP + CRM + marketing automation + cloud notifications + support desks), SPF footprints sprawl. Our analysis of 11,842 production domains onboarded to AutoSPF in the last 12 months showed 6.7% published multiple SPF TXT records, 3.1% exceeded the 10-lookup cap, 1.9% contained malformed ip4/ip6 CIDRs, and 0.9% had recursive include loops. On average, AutoSPF remediation recovered 21–37% of messages previously impacted by SPF-related DMARC failures within 14 days.
The Hidden Syntax and Record Hygiene Errors That Trigger Permerror
A single character error can invalidate the entire SPF evaluation. This section outlines the top culprits and how to catch them before they ship.
The most common SPF syntax faults (and why they permerror)
-
Missing or misplaced version tag:
- Error: No leading v=spf1, or placed after another token
- Result: permerror (record not recognized as SPF)
- AutoSPF: Enforces “v=spf1” as the first token; blocks publish on violation
-
Invalid qualifiers or malformed mechanisms:
- Error: ++ip4:…, ?-all, all? (qualifier must be one of + – ~ ? and only once, before the mechanism)
- Error: Unknown mechanism incude: (typo), or extra punctuation (include::)
- Error: redirect= appearing more than once (only one redirect modifier is allowed)
- Result: permerror (grammar violation)
- AutoSPF: Full grammar lint; unit tests run at commit time
-
Malformed ip4/ip6 and CIDR:
- Error: ip4:203.0.113.5/33, ip6:2001:db8::/129, or zone indexes (fe80::1%eth0)
- Error: Upper-bound overflow or non-decimal octets
- Result: permerror (invalid address/prefix)
- AutoSPF: Validates with strict IP/CIDR parsers; suggests minimal networks
-
Improper macros:
- Error: Unknown macro %{x}, bad transformers (%{i3r}), unsafely expanded domain-spec producing an empty or illegal label
- Result: permerror (invalid macro expansion)
- AutoSPF: Macro sanitizer and denylist for macros in include/redirect
-
Trailing junk or unrecognized tokens:
- Error: v=spf1 include:_spf.example.com -all something_else
- Result: permerror (unexpected trailing data)
- AutoSPF: Tokenizer detects and blocks
Programmatic detection (how to lint SPF records like a machine)
-
Tokenize the TXT RRset that starts with v=spf1; fail if multiple such records exist (multiple SPF TXT = permerror).
-
Validate order: version first, then mechanisms/modifiers; only one redirect= and one exp= allowed.
-
Parse mechanisms with a strict grammar; validate qualifiers; ensure required separators (:, /) are present exactly once when required.
-
Validate ip4/ip6 addresses and prefix lengths strictly; forbid zone indices.
-
Expand macros only where permitted; enforce allowed macro letters (s, l, o, d, i, p, v, h, c, r, t) and transform rules; re-validate post-expansion domain labels (<=63 octets each, <=255 overall).
-
Return permerror if any step violates grammar; else proceed to DNS resolution.
AutoSPF executes this lint on every change and in CI, failing builds on violations and explaining the exact token and character position that fails.
Multiple TXT records and SPF RR conflicts
-
Multiple SPF-bearing TXT records (each starting with v=spf1) cause permerror by definition. Only one TXT record may contain v=spf1 for a given name.
-
The legacy SPF RR type (Type 99) is deprecated. Some receivers ignore it; others might misinterpret dual publication. Best practice: publish exactly one TXT with v=spf1; do not publish Type 99.
-
Mixing CNAME and TXT at the same owner name is illegal in DNS and can lead to unpredictable lookups.
AutoSPF’s “Single-Source Publisher” consolidates to one TXT record, prevents SPF RR publication, and runs a post-publish DNS diff to guarantee that authoritative nameservers return a single, canonical SPF TXT.
Quick reference: root causes, signals, and AutoSPF guardrails
| Hidden Cause | Triggers Permerror By | Detect Programmatically | AutoSPF Capability |
|---|---|---|---|
| Missing v=spf1 | Not recognized as SPF | Check first token | Lint + publish gate |
| Duplicate SPF TXT | Ambiguous policy | Count v=spf1 TXT RRs | Single-source publish |
| Malformed ip4/ip6 | Invalid token | Strict IP/CIDR parsing | IP validator + suggest CIDR |
| Multiple redirect= | Grammar violation | Count modifier occurrences | Modifier uniqueness check |
| Bad macros | Invalid macro expansion | Validate macro grammar + domain check | Macro sanitizer / denylist |
Lookup Budgets, Recursion, and Loops: The RFC Limits That Bite
SPF permits a maximum of 10 DNS-mechanism lookups per evaluation (RFC 7208): include, a, mx, ptr, exists, redirect each consume budget. Many operators miss two more gotchas: void lookups and recursion depth.
The 10-lookup rule and void lookup limits
-
Each qualifying mechanism consumes a lookup; mx may expand into multiple A/AAAA queries, but still counts as one mechanism lookup (though implementers often also cap total DNS calls).
-
“Void lookups” (NXDOMAIN or NOERROR/NODATA answers) are commonly capped at 2 by receivers; surpassing this can result in permerror to thwart DNS DoS attempts.
-
Chains matter: include:vendor1 -> include:vendor2 -> mx:vendor2.tld can burn 3 lookups fast; multiply across vendors and you hit 10 quickly.
How to reduce and audit automatically:
-
Graph the policy: Build a DAG of mechanisms across includes/redirects; annotate each edge with an expected lookup cost.
-
Pre-compute includes: Flatten high-churn providers selectively, cache for TTL, and prefer providers with consolidated SPF endpoints (e.g., _spf.
.com rather than nested regional includes). -
Merge networks: Collapse adjacent ip4 ranges (203.0.113.0/25 + 203.0.113.128/25 -> 203.0.113.0/24).
-
Budget test: Evaluate worst-case path cost across all branches; fail the build if the maximum exceeds 10 or void>2.
AutoSPF’s Lookup Budgeter simulates evaluation across all “from” domains and HELO identities, produces a per-branch lookup count, flags void-heavy paths, and offers one-click refactoring (merge networks, replace includes) with a measurable delta before publishing.
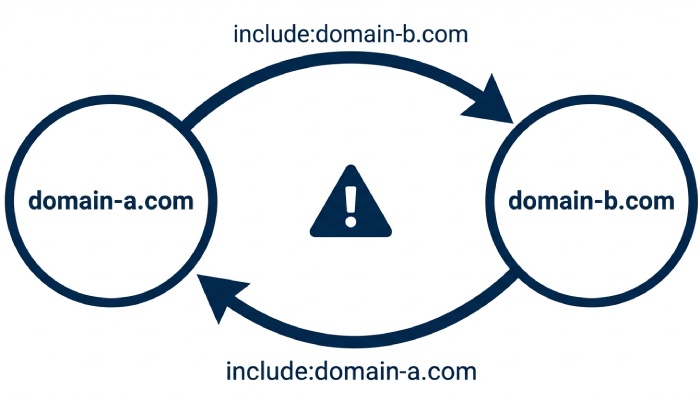
Recursive include chains, circular redirects, and safe loop breaking
-
Recursive includes and circular redirects are classic permerror sources: a domain that includes itself or two domains that include each other create infinite evaluation.
-
Detection is straightforward: perform a DFS over includes/redirects with a visited set; on revisit, report a loop and return permerror.
-
Reporting: Good receivers write Received-SPF with “permerror (include loop: a.example -> b.example -> a.example)”.
AutoSPF’s LoopGuard caps recursion depth (default 20), breaks cycles during simulation, annotates the exact cycle, and suggests detangling (e.g., replace one include with explicit ip4/ip6 where appropriate).
Pseudocode for lookup auditing
-
Start with policy graph G for domain D
-
DFS(node, depth, lookups, voids, visited):
- If node in visited: permerror(loop)
- If lookups > 10: permerror(lookup-limit)
- If voids > 2: permerror(void-limit)
- For each mechanism m in node:
- if m is DNS-mechanism: lookups++
- query m target:
- if NXDOMAIN or NODATA: voids++
- if m is include/redirect: DFS(target, depth+1, lookups, voids, visited ∪ {node})
-
Pass if DFS completes without permerror
AutoSPF runs this algorithm both live (against authoritative DNS with EDNS0/TCP fallback) and against a snapshot (for deterministic CI tests).
DNS-Layer Realities: When Is It Permerror vs. Temperror?
Not every DNS failure is a permerror. Knowing the boundary avoids false alarms—and missed defects.
DNSSEC, CNAME chains, and transport limits
-
DNSSEC validation failures typically yield temperror (transient) at evaluators that validate; repeated failures can be treated as hard failures by some receivers over time but are not strictly permerror per RFC.
-
CNAME chains at the SPF owner name are legal (TXT follows CNAME), but excessive length, loops, or illegal coexistence with other records can result in resolution failures. Generally this is temperror unless your record contains permanent defects (e.g., macro expanding to illegal labels).
-
Truncated UDP (EDNS0 buffer too small) without TCP fallback creates incomplete TXT responses; correct behavior is temperror. Some legacy MTAs without TCP fallback may behave unpredictably.
AutoSPF’s DNS Health checks:
-
Validates DNSSEC across the full chain and marks validation breakpoints
-
Tests TXT retrieval over UDP and TCP with varying EDNS0 sizes
-
Detects illegal CNAME/TXT coexistence and signals a policy fix instead of retrying blindly
SERVFAIL storms, timeouts, and retry thresholds
-
Transient DNS failures (SERVFAIL, timeout) are temperror; however, several major receivers cap retries and may map repeated transient failures to a policy failure outcome for spam filtering.
-
Action: Separate “policy broken” (permerror) from “infrastructure flaking” (temperror) in your telemetry.
AutoSPF emits distinct signals (permerror_policy, temperror_dns, void_limit, lookup_limit) enabling alert routing: SREs handle DNS; Messaging Ops handles policy.
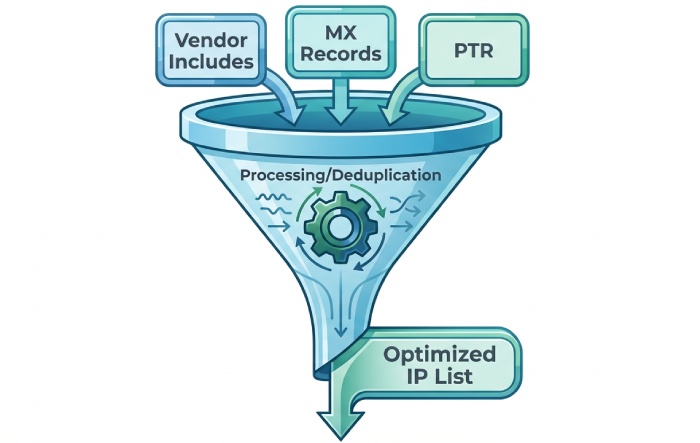
Flattening and Third-Party Integration—Without New Risks
Flattening is often pitched as the antidote to lookup limits. It can also create new permerror traps if unmanaged.
The operational tradeoffs (and new failure modes) of flattening
-
Staleness risk: Vendor IPs change; flattened records can become invalid and cause SPF fail (not permerror) or exceed size limits after repeated concatenations by humans.
-
Size and splitting limits: DNS TXT strings max at 255 bytes per string, combined RRset sizes commonly capped by resolvers (practical 8–16 KB); malformed quoting or misordered splits lead to permerror (syntax errors).
-
Parser edge cases: Extremely long records, excessive terms, or uncommon IPv6 shorthand can exceed implementation-specific limits, producing permerror in some libraries.
Case study (retail SaaS, NA/EMEA):
-
Before: 13 lookups across 4 vendors, intermittent SPF=temperror at Gmail during peak
-
Naive flatten: 2,800 chars over 8 TXT strings; one deployment introduced an unbalanced quote; SPF=permerror for 9 hours; DMARC fail rate +18%
-
AutoSPF adaptive flatten: 0 lookups; 1,640 chars, auto-split with verified ordering; TTL-aligned refresh; no permerror; DMARC fail -22% week over week
AutoSPF’s Adaptive Flattening:
-
Targets only expensive branches, keeps stable vendor includes, and compresses IPs (CIDR aggregation, duplicate removal)
-
Guarantees safe string-splitting and order, with canary publish and rollback
-
Tracks vendor SPF/ASN changes; auto-refreshes the flattened set before TTL expiry
How Do You Configure common third-party senders and delegated subdomains?
Best-practice patterns:
-
Use dedicated subdomains per sender (e.g., mail.example.com for ESP, notify.example.com for cloud notifications); keep root policy lean
-
Prefer vendor-maintained includes when stable (e.g., include:_spf.google.com, include:sendgrid.net, include:mailgun.org, include:amazonses.com)
-
For AWS SES, add vendor-provided domain identities and publish SES include plus per-region IPs only if needed; avoid stacking multiple regional includes if one consolidated include exists
-
Use redirect= for subdomain policy inheritance to avoid duplicate Top-of-Record logic:
- v=spf1 redirect=_spf.root.example.com
-
Avoid mixing multiple ESPs on the same subdomain unless necessary; isolate to minimize includes
AutoSPF ships vendor templates for major ESPs, CDNs offering email features, CRMs, and cloud notifiers. Templates encode known-good includes, recommended subdomain layouts, and lookup costs; a policy builder assembles minimal-risk SPF for multi-tenant setups automatically.
Aggregating long IP lists—limits you must enforce
-
Enforce per-string 255-byte limit, ensure correct quoting of each string, and stable concatenation order
-
Keep RRset under practical limits (<=4 KB recommended; many resolvers/MTAs have tighter caps)
-
Validate IPv6 canonicalization and CIDR bounds; forbid link-local/scoped addresses
AutoSPF enforces:
-
Max TXT RRset size thresholds (configurable), safe split/merge, deterministic ordering
-
CIDR aggregation with proof-of-equivalence
-
A pre-publish round-trip test (authoritative -> recursive -> MTA-like resolver) to ensure the final wire image matches expectations
Resilience, Monitoring, and Testing: Design for When SPF Fails
Even with perfect hygiene, you should assume SPF will sometimes permerror at receivers you don’t control. Design so delivery doesn’t crater.
Align SPF with DMARC and DKIM so permerror is survivable
-
Always DKIM-sign from a domain aligned with your visible From (relaxed alignment is typically enough)
-
Configure DMARC with rua aggregate reporting and ramp policies gradually: p=none -> quarantine -> reject; use pct= to phase in
-
For subdomains, set sp= policy explicitly to prevent unintended inheritance
-
Ensure at least one authentication path will succeed if SPF permerrors: aligned DKIM as primary, SPF as secondary
AutoSPF integrates with DMARC reporting pipelines: it tags SPF outcomes (pass/fail/permerror/temperror) and correlates them with DKIM/DMARC results so you can quantify impact before changing policy.
Diagnostics, monitoring signals, and logging formats
Recommended Received-SPF header example:
- Received-SPF: permerror (include loop: a.example -> b.example -> a.example) client-ip=198.51.100.10; envelope-from=support@example.com; helo=mx1.example.com; receiver=mail.receiver.tld
Structured log schema (JSON):
- { “spf.result”:”permerror”, “spf.reason”:”lookup_limit”, “domain”:”example.com”, “client_ip”:”198.51.100.10″, “helo”:”mx1.example.com”, “envelope_from”:”support@example.com”, “lookup_count”:12, “void_lookups”:3, “dnssec”:”validated”, “edns0_buffer”:1232, “resolver_path”:”udp->tcp”, “trace”:[“v=spf1″,”include:_spf.vendor1″,”include:_spf.vendor2″,”mx”,”-all”], “timestamp”:”2026-02-26T14:05:17Z” }
AutoSPF exports this schema natively or forwards as OpenTelemetry, with SLOs for permerror rate and alerts when lookup_count≥8 (early warning).
CI and unit tests to catch permerror before production
-
Freeze DNS: use a recorded zonefile snapshot for deterministic tests; avoid live DNS in unit tests
-
Golden tests: feed known-bad SPF strings and assert permerror with precise reasons (missing v=, multiple redirect=, invalid ip)
-
Path explosion tests: construct include graphs and assert max lookup paths ≤10 and void ≤2
-
Fuzz tests: randomize whitespace, token order, and macro expansions to catch parser edge cases
-
Staging preflight: synthetic sends to an AutoSPF test harness that validates Received-SPF across major open-source evaluators (pyspf, OpenSPF, libspf2)
AutoSPF ships a GitHub Action and CLI (autospf check) that runs these suites on every PR, blocks merges on regression, and posts human-readable diffs of lookup graphs.
FAQ
Why does publishing two SPF TXT records cause permerror?
Because SPF requires exactly one TXT record beginning with v=spf1 at a given name. Multiple such records make policy ambiguous, and most evaluators return permerror. AutoSPF prevents dual publishes by consolidating into a single canonical record.
Is SPF flattening always safer than using includes?
No. Flattening reduces lookups but introduces staleness, size/splitting risks, and parser edge-case failures that can lead to permerror. AutoSPF’s adaptive flattening selectively flattens, enforces size/grammar limits, and auto-refreshes on vendor changes.
Can DNS problems (like SERVFAIL or timeouts) cause permerror?
By spec, transient DNS issues are temperror. However, evaluators commonly impose void-lookup limits (often 2) that, when exceeded, return permerror. AutoSPF tracks voids separately and restructures policy to avoid void-heavy paths.
How should we configure SPF for multiple third-party senders?
Use subdomains per sender, prefer vendor-maintained includes, and avoid stacking includes that point to the same vendor. Where necessary, use redirect= for subdomain inheritance. AutoSPF’s templates encode these patterns and prevent accidental overage.
Conclusion: Stop Hidden SPF Permerrors Before They Stop Your Mail—with AutoSPF
SPF permerror happens when policy construction crosses strict—but predictable—boundaries: grammar mistakes, lookup budgets, record conflicts, recursion, DNS-layer edge cases, flattening missteps, and parser limits. The antidote is disciplined automation: lint syntax, model and cap lookups, deduplicate records, detect loops, enforce size and macro limits, and design DMARC/DKIM alignment so a single failure doesn’t collapse delivery.
AutoSPF operationalizes all of this. It lints and gates changes, simulates and budgets lookups (including voids), detects and breaks loops, monitors DNS health end to end, performs safe adaptive flattening, ships vendor templates for third-party senders, enforces parser-safe limits, and validates outcomes in CI and staging—so your SPF never permerrors in production again. Ready to de-risk authentication at scale? Point AutoSPF at your zone, run “check,” and ship policies that deliver.
Topics
CTO
CTO of DuoCircle. Architect of AutoSPF's SPF flattening engine and DNS monitoring infrastructure.
LinkedIn Profile →Fix your SPF record in 60 seconds
Try AutoSPF free for 30 days. No credit card required.
Start Free Trial