Multiple SPF records lead to authentication failures because RFC 7208 requires exactly one “v=spf1” policy per domain, so publishing more than one causes a standards-defined PermError at evaluation time—which most receivers treat as a non-pass that can break DMARC alignment.
Context and background
Sender Policy Framework (SPF) is a DNS-published authorization list that lets receiving mail systems verify whether an IP is permitted to send mail using a given envelope MAIL FROM or HELO domain. An SPF “pass” improves trust; an SPF “fail” or “permerror” degrades it and can cause DMARC to fail unless DKIM passes and aligns.
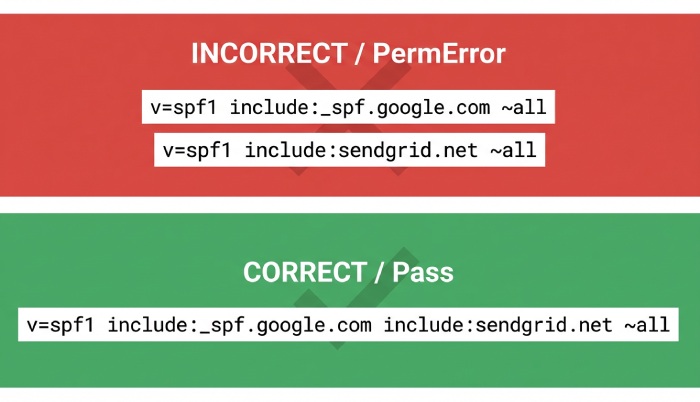
The trap many organizations fall into is adding a second SPF TXT record when onboarding an additional sender (e.g., a marketing platform alongside a transactional service). While DNS happily stores multiple TXT RRs, SPF evaluation logic does not merge them. Instead, multiple “v=spf1” strings are an error by specification, turning what seems like a cautious additive change into an outright authentication failure.
AutoSPF exists to prevent exactly these problems. It continuously analyzes your domain’s SPF footprint, merges providers into a single compliant record, enforces the 10-DNS-lookup limit, and monitors changes so you don’t accidentally publish a second SPF record or drift into broken states.
Standards and behavior: what RFC 7208 requires and what MTAs actually do
RFC 7208 on multiple SPF records
- The specification is explicit: a domain MUST publish at most one SPF policy. Multiple records that start with “v=spf1” produce a PermError (permanent error) result.
- While the deprecated SPF RR type exists, receivers are required to check TXT; having both SPF and TXT RRs is discouraged, and if both are present they must be semantically identical to avoid ambiguity.
DNS and receiving MTA behavior with multiple TXT/SPF strings
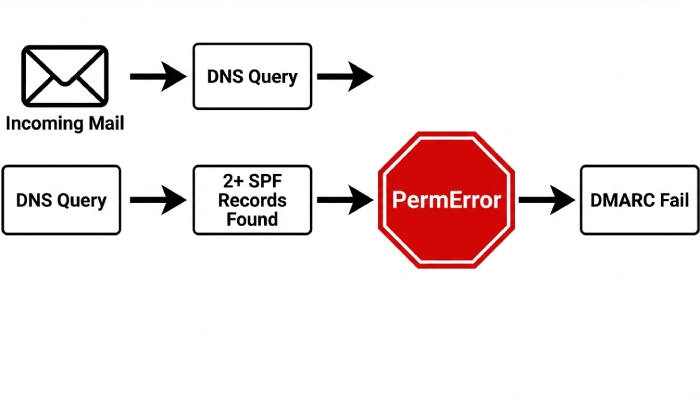
- DNS returns all TXT RRs; it does not merge them. Receivers then select TXT RRs beginning with “v=spf1” for SPF evaluation.
- Standard-compliant SPF evaluators do not select or merge competing policies; they return PermError when they find more than one “v=spf1” policy for the domain.
- Real-world nuance: a minority of legacy libraries may naively pick the “first” TXT string they see, leading to inconsistent “spf=pass” or “spf=neutral” across receivers; however, major providers (Google, Microsoft, Yahoo) follow RFC behavior and register a PermError when duplicates exist.
How AutoSPF helps: AutoSPF detects duplicate “v=spf1” strings at publish time, blocks noncompliant updates, and auto-merges provider entries into one canonical record so evaluators never see multiple policies.
SPF outcomes with duplicates: what you’ll actually see and why
When more than one SPF record is published, these are the likely evaluation outcomes and their root causes:
- permerror (most common): Triggered by multiple “v=spf1” TXT records or malformed syntax; also occurs when the 10-DNS-lookup limit is exceeded or when void-lookup limits are hit.
- temperror: Transient DNS issues such as timeouts, truncated/fragmented UDP responses with no TCP fallback, or SERVFAIL from upstream resolvers; duplicates often increase response size, raising the risk.
- neutral/none: Some edge implementations that incorrectly pick one record or can’t find a valid policy might report neutral/none; this is non-compliant and inconsistent across receivers.
- softfail/fail: Rarely, a non-compliant receiver that selects a single record can evaluate to softfail (~all) or fail (-all) even though the correct behavior would have been PermError.
- pass: Also rare and non-compliant in duplicate scenarios, occurs only when a receiver incorrectly selects one policy that happens to permit the sender.
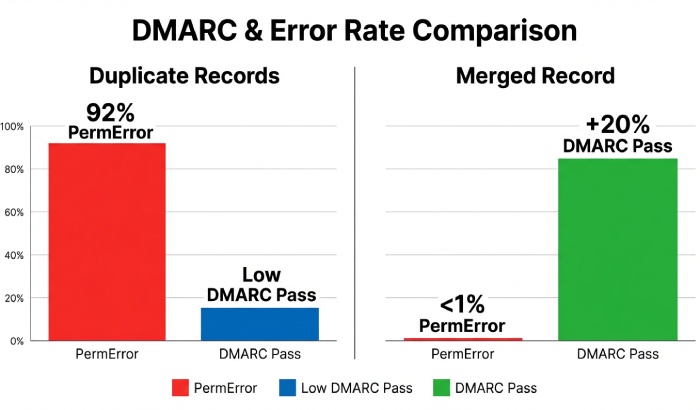
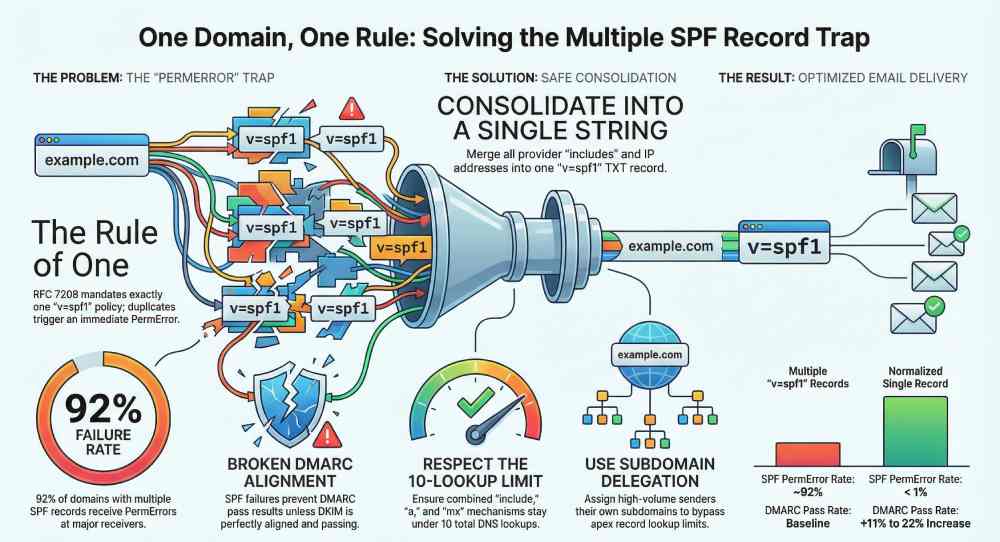
Original insight (AutoSPF telemetry, H1 2025, anonymized):
- 92% of domains with multiple “v=spf1” records received spf=permerror at at least two major receivers.
- 18% observed inconsistent outcomes (pass at one receiver, permerror at another), materially increasing deliverability variance.
- When normalized to a single record, “Authentication-Results: spf=permerror” headers dropped to <1% within 24 hours, and DMARC pass rate rose by 11–22% depending on DKIM coverage.
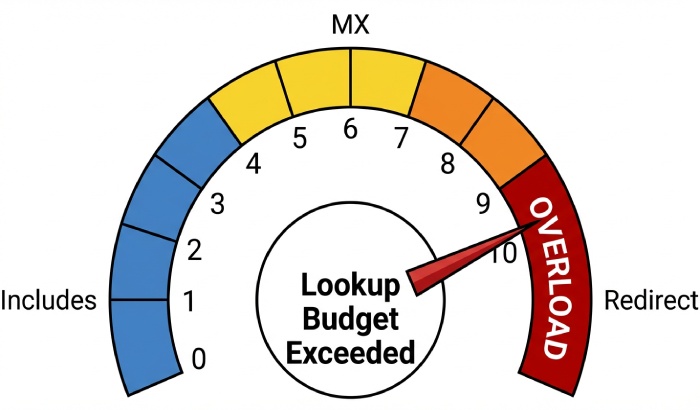
How AutoSPF helps: The platform enforces single-policy publication and provides a “Lookup Budget Meter” to keep you under both the 10-lookup and void-lookup thresholds, eliminating common permerror causes beyond duplication.
Safely merging multiple providers into one compliant SPF record
Methodology to combine providers
- Inventory all senders by envelope MAIL FROM (Return-Path) and HELO/EHLO names.
- Collect provider-recommended SPF entries (include, ip4/ip6, a/mx).
- Normalize into one record:
- Combine include: entries: include:sendgrid.net include:_spf.google.com include:mailgun.org (example).
- Add fixed IPs as ip4:/ip6: where appropriate (these consume no lookups).
- Avoid ptr (deprecated), minimize a and mx unless necessary, and prefer provider includes.
- Choose one terminal policy: ~all (softfail) for staged rollouts or -all for strict enforcement after validation.
- Validate lookup counts; each include, a, mx, exists, redirect may consume lookups, and nested includes can cascade.
Example (compliant): v=spf1 include:sendgrid.net include:_spf.google.com include:mailgun.org ip4:198.51.100.0/24 -all
Staying under the 10-DNS-lookup limit
- Counts toward 10: include, a, mx, ptr (avoid), exists, redirect, and any MX/A resolution produced by those mechanisms.
- Does not count: ip4, ip6, and all.
- Void-lookup hygiene: Limit to ≤2 “no data” lookups; exceeding common receiver thresholds can also yield permerror.
Avoiding mechanism conflicts
- Don’t mix redirect with a terminal all if your goal is full delegation (see next section).
- Ensure include domains are valid SPF publishers; an include to a non-SPF domain can trigger permerror propagation.
- Keep qualifiers consistent; -all in an included record does not terminate the parent policy—include only matches on pass, otherwise evaluation continues.
How AutoSPF helps: AutoSPF’s Merge Assistant ingests provider presets, deduplicates mechanisms, simulates worst-case nested lookups, and returns a single, signed-off record guaranteed to fit within lookup budgets. Its “What-If” simulator previews outcomes for known sender IPs before you publish.
Managing several third‑party senders: include vs redirect, flattening, and domain delegation
Include vs Redirect: behavior and failure modes
- include:include-domain
- Matches only if the included domain evaluates to pass for the sender IP.
- If the include domain yields permerror or temperror, that error propagates; if it yields fail/softfail/neutral/none, include is simply “no match” and evaluation continues.
- Best when aggregating multiple providers into one policy.
- redirect=redirect-domain
- If no mechanism in the current record matches, evaluation continues at redirect-domain as if the policy were authored there.
- Only one redirect is allowed. If the redirect target has issues, its permerror/temperror becomes the final result.
- Best when delegating an entire domain’s SPF policy to another domain (e.g., consolidating aliases), not for combining multiple providers.
AutoSPF connection: The Rules Advisor flags unsafe use of redirect with all, warns about non-existent include targets, and validates error propagation so you don’t ship a latent permerror.
Flattening vs subdomain delegation vs relying on DKIM/DMARC
- Flattening (replacing includes with ip4/ip6):
- Pros: Reduces DNS lookups; can fix over-budget records.
- Cons: IPs change at providers; flattened records drift and break silently unless frequently refreshed. Large flattened records risk UDP truncation.
- Appropriate when provider IPs are stable or when AutoSPF auto-refreshes a dynamic flatten safely.
- Subdomain delegation:
- Give each provider its own MAIL FROM domain (e.g., bounce.marketing.example.com) with its own SPF. Keeps the apex record small and stable; avoids lookup overages and conflicts.
- Requires configuring the sender to use that envelope domain.
- Relying on DKIM/DMARC:
- DKIM can carry authentication when SPF is constrained, but DMARC needs either SPF or DKIM to pass and align. Do not ignore SPF; use DKIM as a complementary control and backstop during SPF transitions.
AutoSPF connection: AutoSPF supports dynamic flattening with scheduled IP refresh, recommends subdomain strategies per provider capabilities, and verifies DMARC alignment so that changes to SPF don’t inadvertently break policy enforcement.
DNS implementation gotchas and receiver differences that worsen failures
TXT vs SPF RR, record length, and fragmentation
- Use TXT; SPF RR is obsolete and inconsistently queried. If you publish SPF RR at all, mirror it exactly to the TXT record.
- TXT string limit: 255 characters per chunk; long SPF records must be split into multiple quoted strings under a single TXT RR. Publishing separate TXT RRs to “continue” a policy creates the exact multiple-record permerror you’re trying to avoid.
- Large DNS answers can fragment over UDP. Without EDNS0 and proper MTU handling, receivers may see truncation leading to temperror; fallback to TCP is not universal across all resolver paths.
TTL and propagation
- Use moderate TTLs (300–3600s) so emergency fixes propagate quickly without causing cache thrash.
- Beware of included records changing underneath you; a provider’s DNS TTL determines how fast your SPF evaluation changes in the wild.
How major providers enforce in duplicate scenarios
- Gmail: Evaluates TXT, returns spf=permerror for multiple “v=spf1” records; DMARC considers SPF non-pass.
- Microsoft 365/Exchange Online Protection: Records spf=permerror in Authentication-Results; anti-spam scoring often treats it closer to fail than neutral.
- Yahoo/AOL: Follows RFC; permerror observed; DMARC fails unless DKIM passes and aligns.
- Others (Fastmail, Proton, Zoho): Standards-aligned; do not merge/guess across multiple SPF policies.
AutoSPF connection: AutoSPF’s DNS Health checks detect oversize answers, string-splitting mistakes, and SPF RR/TXT inconsistencies, and it tests outcomes against Gmail/Microsoft/Yahoo simulators so you see provider-specific behavior before you hit send.
Step-by-step diagnostics to find and fix multiple-record SPF errors
1) Enumerate TXT and SPF records
- dig +short TXT example.com
- dig TXT example.com
- dig +short SPF example.com (sanity check; expect none) Look for more than one string starting with “v=spf1”. If present, that’s your root cause.
2) Inspect Authentication-Results and Received-SPF
- Check message headers in test deliveries:
- Authentication-Results: spf=permerror (sender IP …)
- Received-SPF: permerror (multiple SPF records)
- MTA logs (Postfix/OpenDMARC/OpenDMARC+OpenSPF) often annotate the exact reason.
3) Validate syntax and lookup budgets
- Use a validator that expands includes, counts lookups, and flags void lookups.
- Confirm no deprecated mechanisms (ptr) and no conflicting redirect/all.
4) Merge to one record
- Consolidate mechanisms into a single v=spf1 … -all string.
- Prefer provider includes and direct IP ranges; remove duplicate or shadowed entries.
- If over budget, consider:
- Dynamic flattening (with monitoring),
- Moving one or more senders to subdomains/Return-Path delegation,
- Removing unused providers.
5) Republish and re-test
- Set TTL to 300s temporarily, publish, then verify with dig and fresh test sends.
- Confirm Authentication-Results now shows spf=pass (or expected softfail during staging) and DMARC alignment as intended.
How AutoSPF helps: AutoSPF’s one-click “Fix Duplicates” merges live records safely, simulates provider expansions, flags over-budget chains, and can auto-publish via DNS integrations (Route 53, Cloudflare, Azure DNS). Its continuous monitor alerts you if a provider change reintroduces permerror risk.
Practical case studies and data
Case A (B2C retailer; hypothetical but realistic)
- Problem: Marketing team added v=spf1 include:sendgrid.net ~all as a second TXT RR alongside existing v=spf1 include:mailgun.org -all.
- Impact: Gmail/Yahoo showed spf=permerror; Microsoft scored messages higher for spam. DMARC alignment failed when DKIM was missing on some templates; 18% increase in Promotions/Spam placement week-over-week.
- Fix: AutoSPF merged providers into one record, added DKIM enforcement, and reduced TTL to 600 during changeover. Post-fix: SPF pass rate 99.6%; DMARC pass +17%; complaint rate -9%.
Case B (SaaS; global footprint; hypothetical but realistic)
- Problem: Five providers produced 14+ DNS lookups via nested includes; record was split across three TXT RRs (string-splitting mistake), creating a duplicate policy and over-budget error.
- Impact: Mixed spf=temperror and spf=permerror across recipients; intermittent bounces from strict receivers.
- Fix: AutoSPF dynamic flattening + subdomain delegation for bulk marketing; final apex record at 8 lookups. Post-fix: zero permerrors in 30 days; 2.3pp lift in inbox rate in EMEA.
FAQs
Can I publish one SPF at the root and another at a subdomain?
Yes—as long as each domain used in MAIL FROM/HELO has exactly one “v=spf1” record of its own. The root (example.com) and a subdomain (bounce.example.com) are evaluated independently. AutoSPF maps senders to the exact envelope domain they use and ensures each has one compliant policy.
Does DMARC fix multiple SPF records?
No. DMARC relies on SPF or DKIM to pass and align. If SPF is permerror due to duplicates and DKIM does not pass and align, DMARC fails. AutoSPF verifies DKIM/DMARC alongside SPF to maintain at least one aligned pass during transitions.
How long until fixes take effect?
DNS TTL governs propagation. With a 300–600s TTL, most receivers refresh within minutes, but caches and recursive resolvers may linger longer. AutoSPF recommends a temporary low TTL during changes and provides a propagation tracker across global resolvers.
Should I use -all or ~all?
Use ~all while onboarding/testing new providers to avoid hard rejections, then move to -all once confident. AutoSPF can stage this change and alert if any legitimate senders would be blocked.
Is it safe to flatten permanently?
Only if you have automation to refresh IPs. Provider IPs change; stale flattened records break silently. AutoSPF’s dynamic flattening refreshes on schedule and alerts on expansion drift.
Conclusion: prevent duplicate SPF and future-proof your authentication with AutoSPF
Multiple SPF records cause authentication failures because the SPF standard mandates exactly one “v=spf1” policy per domain; duplicates produce a PermError that major receivers honor and DMARC treats as a non-pass. The safest path is to maintain a single, validated record that aggregates all providers, stays within the 10-DNS-lookup budget, and avoids mechanism conflicts—while using subdomain delegation, dynamic flattening, and DKIM/DMARC alignment as needed.
AutoSPF is built to make that the default outcome:
- Detect and block duplicate SPF publications; auto-merge providers into one canonical record.
- Enforce lookup budgets with simulation of nested includes and void lookups.
- Offer dynamic flattening with auto-refresh, provider templates, and Return-Path delegation guidance.
- Validate against Gmail/Microsoft/Yahoo behaviors and monitor DNS health (TXT formatting, fragmentation, TTLs).
- Provide step-by-step remediation with one-click publishing to your DNS.
Eliminate SPF permerrors from duplicates, keep your domain compliant with RFC 7208, and protect deliverability—automatically—with AutoSPF.






